Premium Only Content
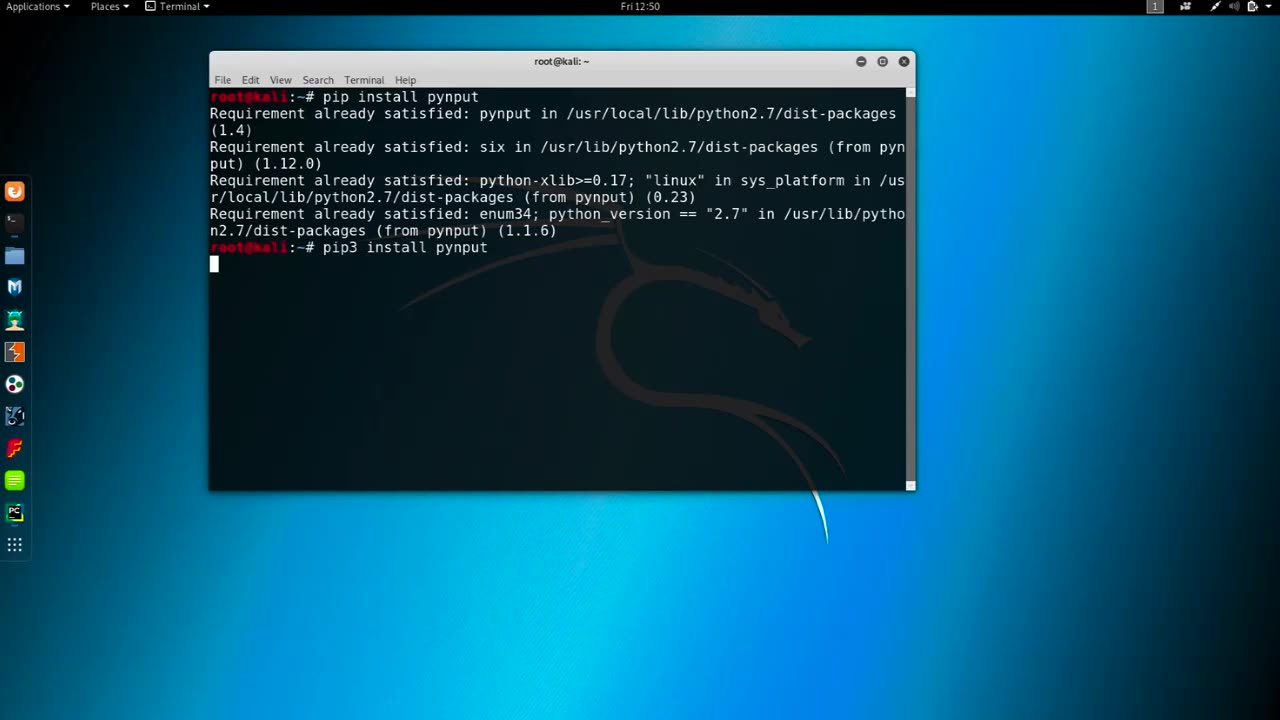
Chapter-37, LEC-4 | Logging Keyboards | #education #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Logging keyboards, also known as keyboard loggers or keystroke loggers, are software or hardware devices that capture and record all keystrokes made on a computer or mobile device's keyboard. They are used for monitoring or surveillance purposes and can capture every key pressed, including letters, numbers, special characters, and function keys, as well as other activities such as mouse movements, screenshots, and websites visited.
Keyboard loggers can operate in stealth mode, meaning they can run in the background without the user's knowledge or consent, and log all keystrokes made on the device. They can capture a wide range of information, including passwords, usernames, credit card numbers, chat messages, and other sensitive data that is entered using the keyboard.
Keyboard loggers may be used for both legitimate and malicious purposes. Legitimate uses include monitoring employee activity in the workplace, parental control to monitor children's online activities, and data recovery. However, keyboard loggers can also be used maliciously for stealing personal information, committing identity theft, financial fraud, and other cybercrimes.
It is essential to note that using keyboard loggers without proper authorization is illegal in many jurisdictions, and ethical considerations should always be taken into account when using them for any purpose. Users should always be informed and give explicit consent before their activities are monitored, and appropriate security measures should be in place to protect the data collected by keyboard loggers.
It is important to use keyboard loggers responsibly and within the legal and ethical boundaries, ensuring that privacy rights are respected, and data security is maintained at all times. Proper consent, transparency, and compliance with applicable laws and regulations are crucial when using keyboard loggers for any purpose.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
Tundra Tactical
2 hours agoProfessional Gun Nerd Plays Battlefield 6
102 watching -
 LIVE
LIVE
Quite Frankly
7 hours ago31/ATLAS to Enoch, Election Night Updates, Open Lines | Timothy Alberino 11/4/25
447 watching -
 1:05:56
1:05:56
vivafrei
2 hours agoComey Doubles Down, Prosecution Doubles Up! Election Day Madness! Boasberg Impeachment & MORE!
21.2K13 -
 LIVE
LIVE
SpartakusLIVE
1 hour agoNEW Meta = EPIC WINS on Battlefield 6 - REDSEC
226 watching -
 4:46:51
4:46:51
StoneMountain64
5 hours agoBattlefield REDSEC leveling guns for attachments
29.6K2 -
 26:19
26:19
Liberty Hangout
4 days agoAnti-Trumpers Make Up Bizarre Theories
9.16K38 -
 LIVE
LIVE
GritsGG
5 hours agoWorld Record Win Streak Attempt! #1 Most Wins 3880+!
40 watching -
 LIVE
LIVE
The Rabble Wrangler
16 hours agoBattlefield with The Best in the West
43 watching -
 13:56
13:56
Cash Jordan
3 hours ago"OPEN BORDERS" Mob BATTERS Portland Jail… 'COMBAT' Marines DEFY Judge, BREAK BONES
4.92K8 -
 16:44
16:44
Russell Brand
4 hours agoAmerica’s Hidden Royalty
29.4K29