Premium Only Content
Chapter-38, LEC-4 | Running Commands | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
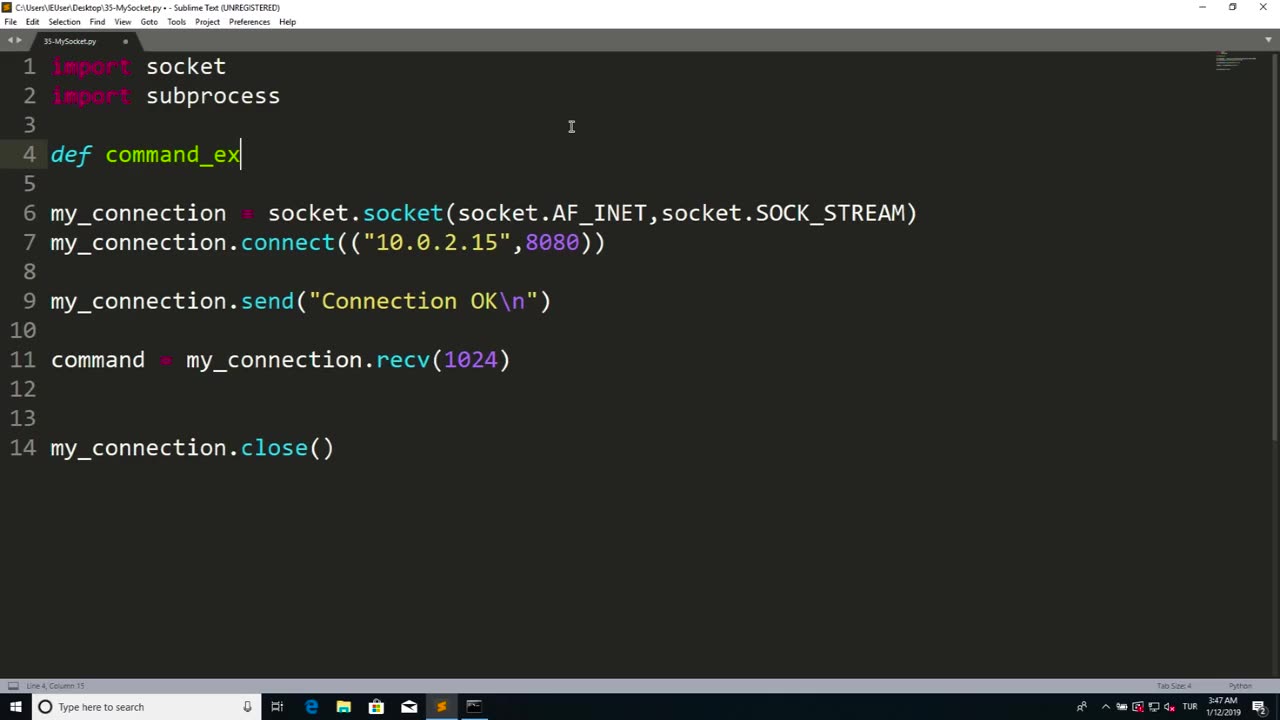
Running commands refers to the process of executing instructions or commands in a computer system or software to perform specific tasks or operations. Commands are typically entered into a command-line interface or terminal, which allows users to interact with a computer system directly through text-based commands.
Running commands can be used for a wide range of purposes, including system administration, software configuration, troubleshooting, automation, and more. Commands can be used to manipulate files and directories, configure settings, install or uninstall software, manage processes, retrieve information, and perform other operations depending on the specific software or system being used.
Running commands requires knowledge of the specific command syntax, options, and parameters for the software or system being used. It is important to understand the implications and potential consequences of the commands being executed, as they can impact the performance, stability, and security of the system or software.
Proper caution and authorization must be exercised when running commands, as some commands may have elevated privileges and can potentially cause harm or damage to the system or data if used improperly or without proper authorization. It is essential to follow best practices, such as using appropriate permissions, verifying the source and integrity of commands, and testing commands in a safe and controlled environment.
Running commands can be a powerful tool in managing computer systems and software efficiently and effectively. However, it requires knowledge, expertise, and responsible use to ensure that commands are executed safely and securely, and that the intended tasks or operations are performed accurately and without any unintended consequences. Always exercise caution, follow proper authorization procedures, and adhere to best practices when running commands in any computer system or software environment.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 1:17:52
1:17:52
Dialogue works
3 days ago $10.17 earnedMartin Armstrong: This Is How World War III Starts… And It Already Has
36.4K18 -
 38:16
38:16
daniellesmithab
3 days agoAlberta Update: Getting Kids Back to the Classroom
28.4K11 -
 20:48
20:48
BlaireWhite
5 days agoTrans TikTokers Are Crashing Out (Over Nothing)
32.6K11 -
 2:07:06
2:07:06
Side Scrollers Podcast
22 hours agoHasan Piker CAUGHT LYING AGAIN + Twitch URGES LEFTIST IDEOLOGY + More | Side Scrollers
74.8K11 -
 8:40
8:40
MattMorseTV
17 hours ago $14.34 earnedSchumer just KICKED OFF the Left-Wing CIVIL WAR.
35.8K33 -
 21:39
21:39
Nikko Ortiz
2 days agoI Take A North Korean Shooting
33.5K6 -
 1:46:26
1:46:26
The Michelle Moore Show
21 hours ago'The Religion Invasion In the U.S. and the Deep State Agenda' Guest, Mark Taylor: The Michelle Moore Show (Nov 3, 2025)
41.9K41 -
 LIVE
LIVE
TruthStream with Joe and Scott
5 days agoSovereign Codes & Cosmic Infrastructure,Ufo's, UAP's, Monads, Matrix Satellites, Interstellar Visitors, SYRONA #505
310 watching -
 LIVE
LIVE
Lofi Girl
2 years agoSynthwave Radio 🌌 - beats to chill/game to
137 watching -
 5:55:11
5:55:11
MattMorseTV
14 hours ago $103.92 earned🔴Trump's '60 Minutes' INTERVIEW + MUCH MORE.🔴
165K53