Premium Only Content
This video is only available to Rumble Premium subscribers. Subscribe to
enjoy exclusive content and ad-free viewing.
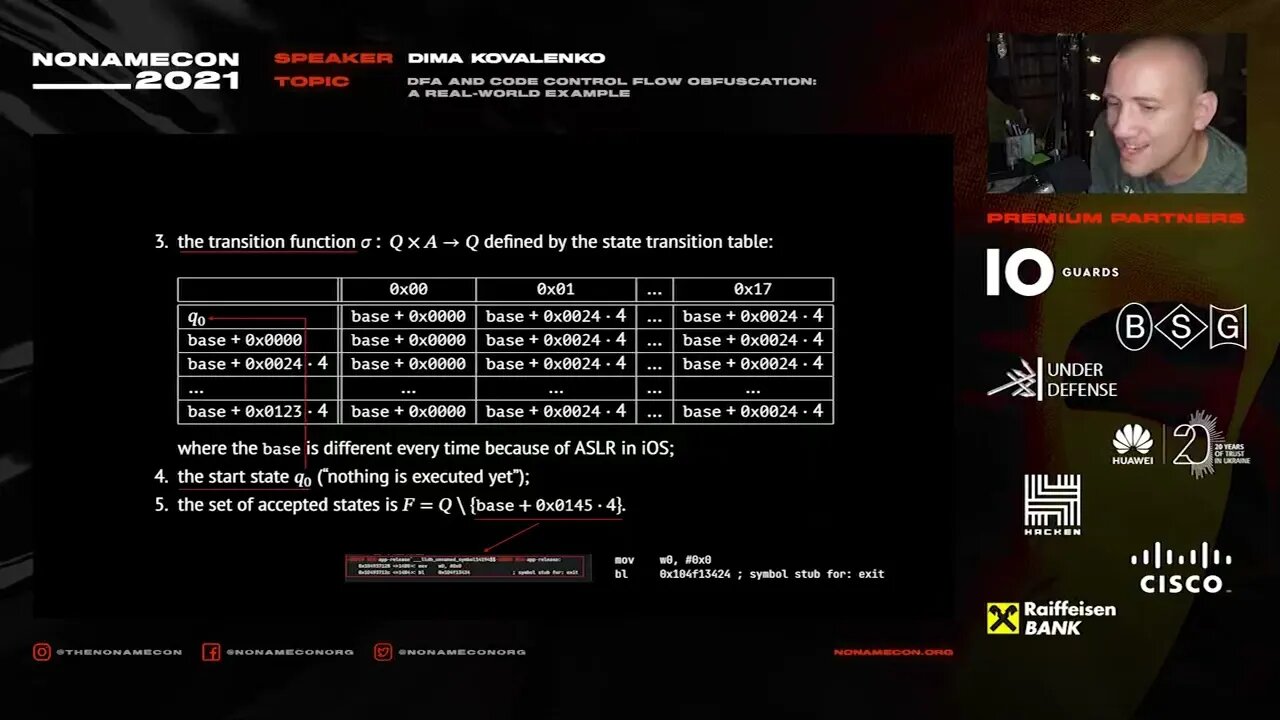
DFA and code control flow obfuscation a real world example Dima Kovalenko
Loading comments...
-
 20:48
20:48
BlaireWhite
5 days agoTrans TikTokers Are Crashing Out (Over Nothing)
22.4K11 -
 2:07:06
2:07:06
Side Scrollers Podcast
21 hours agoHasan Piker CAUGHT LYING AGAIN + Twitch URGES LEFTIST IDEOLOGY + More | Side Scrollers
66.4K10 -
 8:40
8:40
MattMorseTV
17 hours ago $10.71 earnedSchumer just KICKED OFF the Left-Wing CIVIL WAR.
25K31 -
 21:39
21:39
Nikko Ortiz
2 days agoI Take A North Korean Shooting
27K6 -
 1:46:26
1:46:26
The Michelle Moore Show
20 hours ago'The Religion Invasion In the U.S. and the Deep State Agenda' Guest, Mark Taylor: The Michelle Moore Show (Nov 3, 2025)
35.8K39 -
 LIVE
LIVE
TruthStream with Joe and Scott
5 days agoSovereign Codes & Cosmic Infrastructure,Ufo's, UAP's, Monads, Matrix Satellites, Interstellar Visitors, SYRONA #505
344 watching -
 LIVE
LIVE
Lofi Girl
2 years agoSynthwave Radio 🌌 - beats to chill/game to
154 watching -
 5:55:11
5:55:11
MattMorseTV
13 hours ago $100.53 earned🔴Trump's '60 Minutes' INTERVIEW + MUCH MORE.🔴
163K51 -
 2:02:36
2:02:36
Badlands Media
18 hours agoBaseless Conspiracies Ep. 157: Jack the Ripper, the Crash & the Great Disclosure Countdown
41K24 -
 2:06:09
2:06:09
Inverted World Live
14 hours agoMysterious Crash at Area 51 | Ep. 134
44.2K20