Premium Only Content
This video is only available to Rumble Premium subscribers. Subscribe to
enjoy exclusive content and ad-free viewing.
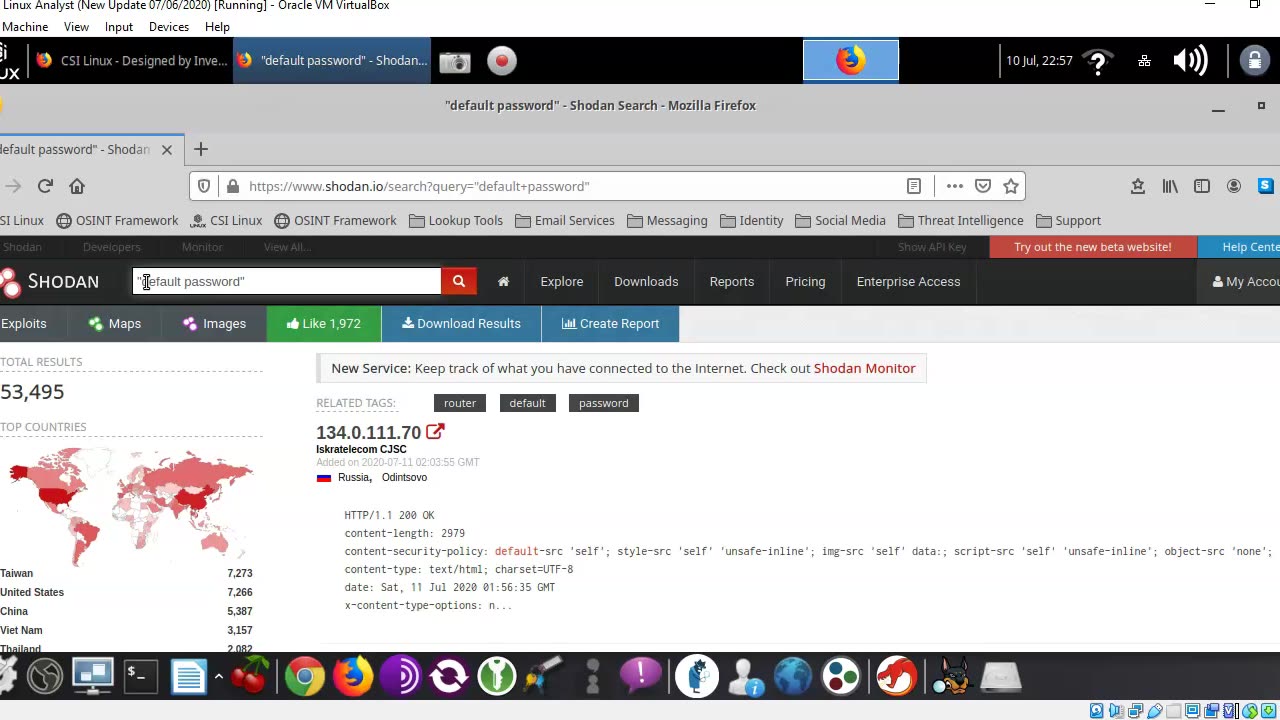
Using Shodan to Find Vulnerable Devices
2 years ago
50
shodan
shodan tutorial
vulnerable devices
shodan search engine
shodan search engine tutorial
shodan hacking tutorial
shodan api
how to use shodan
shodan search
how to find vulnerability using shodan and tamper data
shodan search tutorial
Using Shodan to Find Vulnerable Devices
Excerpt video from one of my many online courses.
1000+ videos on hacking, operating systems, digital forensics, and Microsoft applications
https://www.syberoffense.net - Official course site.
Have online courses for sale? Contact Syberoffense at [email protected]
Facebook - https://www.facebook.com/sybertraining
Loading comments...
-
 LIVE
LIVE
LFA TV
19 hours agoLIVE & BREAKING NEWS! | TUESDAY 12/02/25
1,252 watching -
 UPCOMING
UPCOMING
John Crump Live
3 hours agoDLD Makes His Case For Micro Influencer of The Year
16 -
 UPCOMING
UPCOMING
freecastle
5 hours agoTAKE UP YOUR CROSS- Then you will call on ME and come and pray to ME, and I will LISTEN to you."
851 -
 LIVE
LIVE
The HotSeat With Todd Spears
1 hour agoEP 218: God Bless America, Why Not America Bless GOD? Pt 2
699 watching -
![[Ep 804] HOAX or War Crime? Dems Hysteria | Hakeem’s Threats| Guest Sam Anthony [your]NEWS](https://1a-1791.com/video/fwe2/1c/s8/1/u/K/V/E/uKVEz.0kob-small-Ep-804-HOAX-or-War-Crime-De.jpg) LIVE
LIVE
The Nunn Report - w/ Dan Nunn
2 hours ago[Ep 804] HOAX or War Crime? Dems Hysteria | Hakeem’s Threats| Guest Sam Anthony [your]NEWS
258 watching -
 52:43
52:43
Right Side Broadcasting Network
5 hours agoLIVE REPLAY: President Trump Makes an Announcement at the White House - 12/2/25
41K22 -
 47:27
47:27
The White House
3 hours agoPresident Trump Makes an Announcement, Dec. 2, 2025
17.7K17 -
 53:14
53:14
Professor Nez
3 hours ago🇺🇸 Trump’s SECRET Weapon for American Families (LIVE)
19.8K24 -
 1:07:14
1:07:14
DeVory Darkins
3 hours agoBREAKING: Washington Post suffers Major SETBACK after Hegseth story gets debunked
119K70 -
 LIVE
LIVE
StoneMountain64
3 hours agoArc Raiders EXPEDITION Money Making is Insane
137 watching