Premium Only Content
This video is only available to Rumble Premium subscribers. Subscribe to
enjoy exclusive content and ad-free viewing.
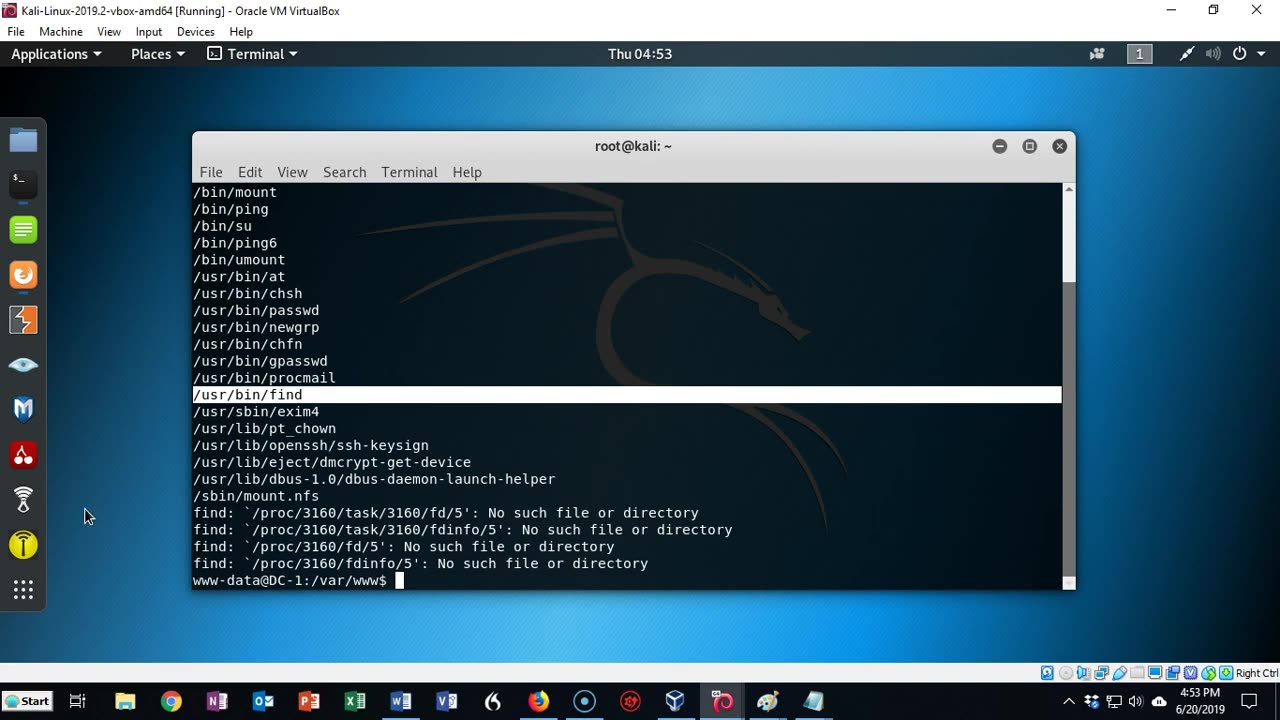
Capture the Flag - DC-1- Exploitation, Privilege Elevation
2 years ago
11
capture the flag
capture the flag hacking
capture the flags
what is capture the flag?
play capture the flag
capture
capture the flag türkçe
defcon capture the flag
capture the flag stapler
security capture the flag
capture the flag explained
Excerpt video from one of my many online courses.
1000+ videos on hacking, operating systems, digital forensics, and Microsoft applications
https://www.syberoffense.net - Official course site.
Have online courses for sale? Contact Syberoffense at [email protected]
Facebook - https://www.facebook.com/sybertraining
Loading comments...
-
 17:02
17:02
Professor K
2 years agoCapture the Flag - DerpnStink - Walkthrough Part I
24 -
 19:02
19:02
The Pascal Show
1 day ago $3.62 earnedNOT SURPRISED! Pam Bondi Is Lying To Us Again About Releasing The Epstein Files
16.2K11 -
 6:05
6:05
Blabbering Collector
19 hours agoRowling On Set, Bill Nighy To Join Cast, HBO Head Comments On Season 2 Of Harry Potter HBO!
16.8K4 -
 57:44
57:44
TruthStream with Joe and Scott
2 days agoShe's of Love podcast & Joe:A co-Hosted interview, Mother and Daughter (300,000+Facebook page) Travel, Home School, Staying Grounded, Recreating oneself, SolarPunk #514
33.1K1 -
 30:49
30:49
MetatronHistory
1 day agoThe Truth about Women Warriors Based on Facts, Evidence and Sources
32.9K15 -
 2:59:08
2:59:08
FreshandFit
14 hours agoA Sugar Baby & A Feminist ALMOST Fight Each Other
265K66 -
 6:24:23
6:24:23
SpartakusLIVE
12 hours agoFriday Night HYPE w/ YOUR King of Content
111K2 -
 2:27:53
2:27:53
Laura Loomer
10 hours agoBREAKING: MTG Resigns From Congress, Mamdani Meets Trump
76.6K132 -
 3:30:10
3:30:10
PandaSub2000
1 day agoDisney & Buzz Trivia | PHOENIX & HAVIX (Original Live Version)
38K1 -
 15:23
15:23
T-SPLY
15 hours agoBUSTED Assistant Principle And Brother Arrested For Wanting To Kill ICE!
35.2K14