Premium Only Content
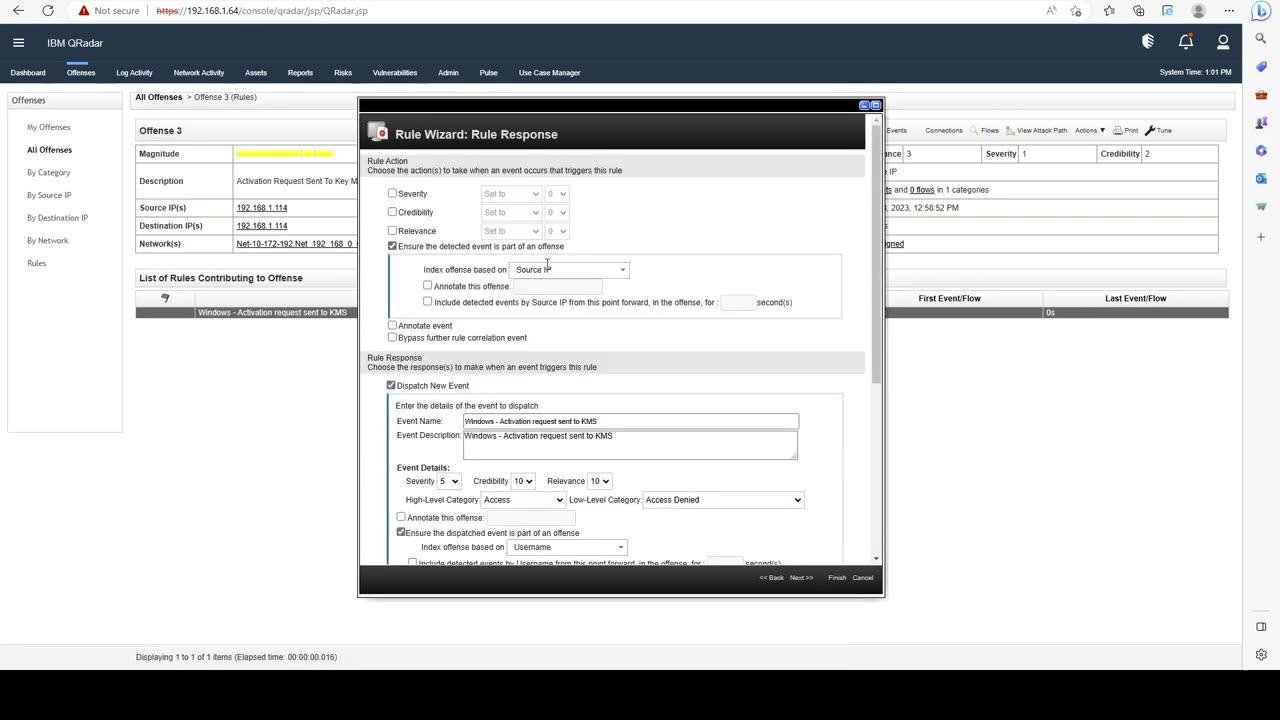
Section 3 - Rules - Lecture 3- Troubleshooting Rules
Introduction to IBM QRadar:
IBM QRadar is a comprehensive security information and event management (SIEM) solution that helps organizations detect and respond to cybersecurity threats effectively. By collecting and analyzing data from various sources across the IT environment, QRadar provides insights into potential security incidents, enabling proactive threat management and rapid incident response.
Key Features and Benefits:
Real-Time Monitoring: QRadar monitors logs, network flows, and user activity in real time to identify anomalies and suspicious behavior.
Threat Detection: It employs advanced analytics and machine learning to identify potential security threats and vulnerabilities.
Incident Response: QRadar streamlines incident investigation and response workflows, aiding in rapid mitigation.
Compliance Management: The solution assists in meeting regulatory compliance requirements by providing detailed audit trails and reporting capabilities.
Installation Guide:
Here's a high-level overview of the installation process for IBM QRadar:
System Requirements:
Ensure your hardware meets the system requirements outlined in the official documentation.
Review supported operating systems and prerequisites.
Software Download:
Access the IBM QRadar software package from the official IBM website.
Obtain necessary licenses and access credentials.
Installation Steps:
Run the installation executable or script on the target system.
Follow the on-screen instructions to configure basic settings.
Set up network and communication settings.
Database Configuration:
Configure the database settings. QRadar typically uses IBM Db2 as its database backend.
Specify database location, credentials, and other required details.
Appliance Setup (Physical or Virtual):
If using a physical appliance, ensure it's properly connected and powered.
For virtual deployments, allocate appropriate resources (CPU, RAM, disk space) based on system requirements.
Initial Configuration:
Access the QRadar web console via a browser.
-
 LIVE
LIVE
Steven Crowder
1 hour ago🔴 Just Release the Damn Epstein Files - End It Once and For All
46,297 watching -
 LIVE
LIVE
The Rubin Report
41 minutes agoPress Goes Silent When Told Ugly Facts of Damage Done by Democrat Shutdown
1,075 watching -
 1:03:48
1:03:48
VINCE
2 hours agoDems' Shutdown Is Gone. Now They've Revived Epstein | Episode 168 - 11/13/25
65.4K43 -
 LIVE
LIVE
LFA TV
13 hours agoLIVE & BREAKING NEWS! | THURSDAY 11/13/25
3,611 watching -
 LIVE
LIVE
Nikko Ortiz
52 minutes agoVETERAN DAY FAILS... | Rumble LIVE
171 watching -
 LIVE
LIVE
Badlands Media
9 hours agoBadlands Daily: November 13, 2025
3,757 watching -
 LIVE
LIVE
Simply Bitcoin
18 hours agoThe Bitcoin Crucible w/ Alex Stanczyk & Tomer Strolight - Episode 8
116 watching -
 LIVE
LIVE
LadyDesireeMusic
1 hour agoLive Piano Renditions & Chat - Good Vibes - Make Ladies Great Again
91 watching -
 LIVE
LIVE
The Big Mig™
2 hours agoSchumer’s Government Shutdown Is Over! Hallelujah
2,667 watching -
 1:34:32
1:34:32
Graham Allen
3 hours agoDems “Bombshell” Epstein Docs Against Trump Are LIES!! + The Gov Shutdown Is Finally OVER!
103K1.03K