Premium Only Content
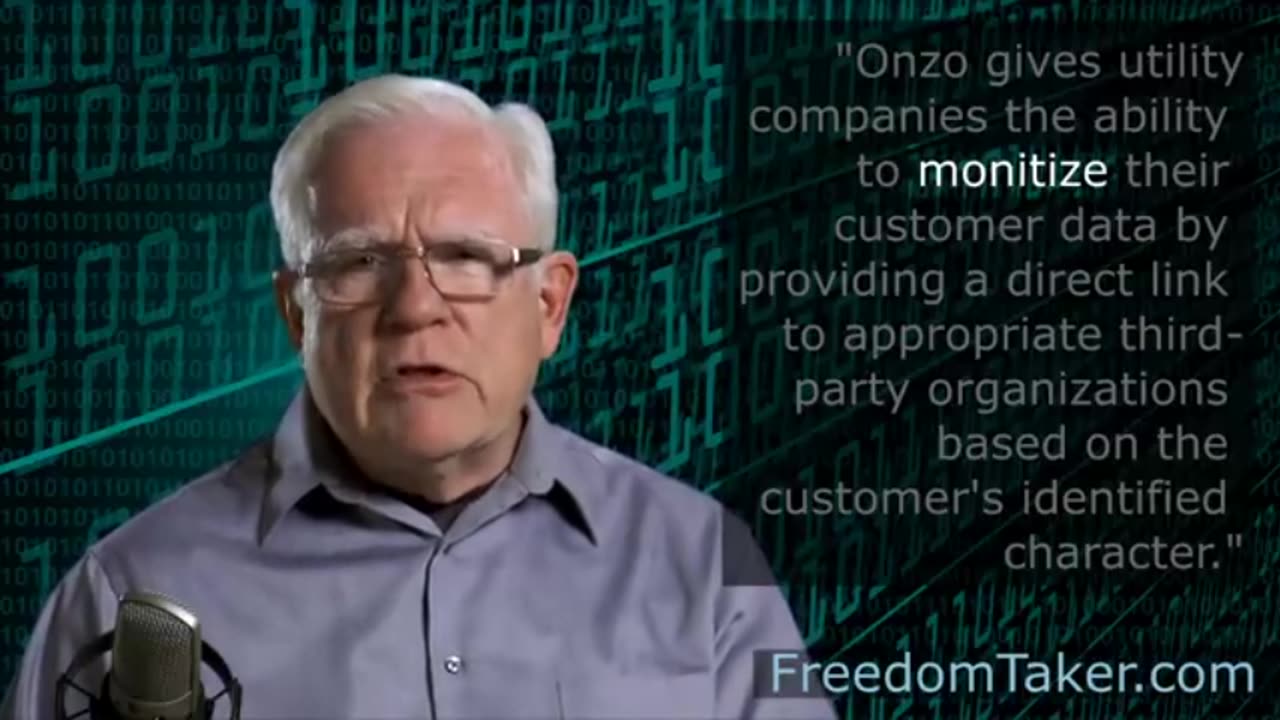
The Role Of Utility Meters In Mass Surveillance
The Role Of Utility Meters In Mass Surveillance
Biometrics
Technologies: Biometric technologies refer to automated methods that are able to identify or recognise the identity of a living person, after analysing some of his/her characteristics (e.g., physiological and/or behavioural characteristics) (Mordini and Petrini 2007; Nwatu 2011). Examples of biometric technologies that consider the physiological characteristics of a person are these of face recognition, facial thermogram, recognition of fingerprints, the geometry of hands, iris or retina scanning, etc. In addition, behavioural oriented biometric technologies include those that can recognise someone’s manner of walking (i.e., gait recognition), analyse the way people type using a keyboard (i.e., keystroke analysis), how they operate a pointing device (e.g., mouse dynamics in the case of a mouse), signature analysis, or even performing a waveform analysis of people’s voices to verify their identity. Finally, another category of biometrics is that of multimodal biometric systems, which refer to systems that include multiple sources in order to establish the identity of an individual (Ross and Jain 2004).
Application areas: The main objective of biometric technologies is to identify, verify, or authorise an individual. That objective is mainly accomplished through the application of pattern-matching algorithms on a set of collected data (usually kept in database systems). Therefore, some of the domains in which biometric technologies find a use are systems applicable to immigration and border control (e.g., use of biometric ‘chipped’ passports (nidirect 2014)); to criminal justice systems and profiling systems (e.g., the Combined DNA Index System (CODIS) (FBI 2011) used by the FBI and U.S. Department of Justice); national identity systems, etc. (Bellanova et al. 2012). Despite the wide spectrum of applications of biometric technologies, their capabilities are mostly restricted to the monitoring of people through identification or verification operations.
Challenges: Despite the high effectiveness of biometric technologies, there are recognised challenges that should be considered when using them. In most of the examined studies, security and privacy concerns are identified as key challenges. Another interesting challenge is that of the reliability level offered by biometric technologies (e.g., reliability with regard to DNA comparison), or even vulnerabilities that might exist in a system operating with biometric technologies (FBI 2006).
-
 18:28
18:28
joegecko's Proxy Channel
2 days agoPOWER PLAY: Iran Hijacks Tanker in Gulf Waters - Here’s What They’re Signaling
531 -
 LIVE
LIVE
Akademiks
36 minutes agoMeg Thee Stallion Back LYING again? Offset vs Finesse2x. 6ix9ine house robbed.. HERES WHO DID IT
999 watching -
 LIVE
LIVE
TimcastIRL
2 hours agoGOP Rep Threatens Hillary Clinton With CRIMINAL CHARGES Over Epstein | Timcast IRL
6,634 watching -
 LIVE
LIVE
Laura Loomer
2 hours agoEP157: Marjorie TRAITOR Greene Turns On Trump
1,233 watching -
 1:35:44
1:35:44
Tucker Carlson
2 hours agoWhy Is Nick Fuentes So Popular? Nikki Haley's Son Explains.
39.3K236 -

T-SPLY
1 hour agoProtesters Clash With Border Patrol In Charlotte!
4.35K2 -
 LIVE
LIVE
ThatStarWarsGirl
55 minutes agoTSWG LIVE: I'm Back From My Channel Strike! Let's Discuss The Elephant In The Room
167 watching -
 LIVE
LIVE
I_Came_With_Fire_Podcast
12 hours agoAmerica's Hidden War | The Propaganda Through Line | An Ally Aids an Enemy
175 watching -
 2:14:16
2:14:16
TheSaltyCracker
3 hours agoDEMs Have Real Bad Week ReeEEStream 11-19-25
96.9K125 -
 LIVE
LIVE
SpartakusLIVE
4 hours agoNEW Redsec UPDATE || STACKS OF LOOT LATER?!
296 watching