From Gates to Guardrails Alternate Approaches to Product Security Jason Chan
Loading comments...
-
 42:02
42:02
AllHackingCons
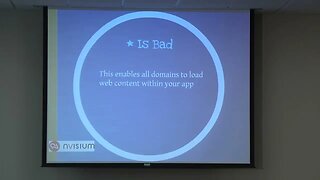
1 year agoMinding The Gap Secure PhoneGap Apps Jack Mannino, Jason Haddix
7 -
 46:34
46:34
AllHackingCons
1 year agoSecure Programming Support in IDE with Bill Chu and Jing Xie
-
 1:10:40
1:10:40
infosectrain01
1 year agoDay - 1 What is Information Security? | Principles of Information Security
8 -
 8:18
8:18
EWU Bodycam
1 year agoMan Breaches The Gates Of Area 51
89 -
 1:20
1:20
KGTV
6 years agoSeeking tighter security after rash of break-ins
-
 10:05
10:05
Cybercram
3 years agoBlack Hat and Defcon Review
84 -
 0:56
0:56
BlackAlchemy
1 year agoPrivacy Tips 101: How to Chose a Security Vendor
1 -
 2:18
2:18
WTMJMilwaukee
6 years ago911 officials guarding against hackers
1 -
 53:50
53:50
infosectrain01
9 months agoCracking the Security Operations Center (SOC) Interview | Expert Tips by Bharat
36 -
 1:12:58
1:12:58
infosectrain01
1 year agoDay - 3 What is Ethical Hacking Concepts? | Hacking Motives | Ethical Hacking Phases
22