Premium Only Content
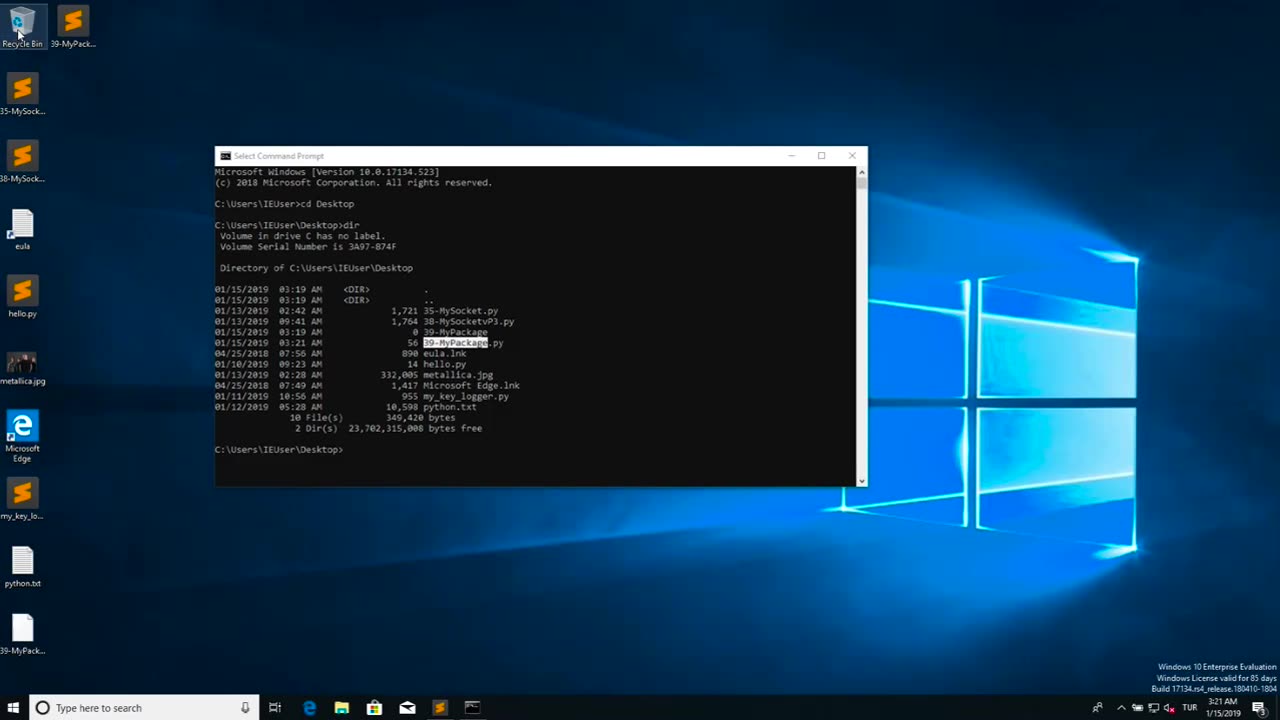
Chapter-39, LEC-2 | Malicious Files | #ethicalhacking #maliciousdiles #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Malicious files refer to digital files, such as software programs or documents, that are intentionally designed to harm or compromise the security of a computer, network, or device. These files may contain malicious code, also known as malware, which can be executed or triggered to perform malicious activities without the knowledge or consent of the user.
Malicious files can come in various forms, including viruses, worms, Trojans, ransomware, spyware, adware, and other types of malware. They are typically disguised as legitimate files or software to deceive users into downloading or executing them. Once the malicious file is executed or opened, it can spread throughout the system, exploit vulnerabilities, steal sensitive information, disrupt operations, or cause other types of damage.
Malicious files are often distributed through various means, such as infected email attachments, compromised websites, infected USB drives, social engineering tactics, and other methods. They can target any type of device or operating system, including computers, servers, smartphones, tablets, and IoT (Internet of Things) devices.
The consequences of encountering and executing malicious files can be severe, ranging from data breaches and financial loss to privacy violations, system downtime, and reputational damage. Therefore, it is crucial to implement robust cybersecurity measures, such as using antivirus software, keeping software and systems updated, being cautious while downloading or opening files, and practicing safe online behavior, to protect against malicious files and other cyber threats.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 12:11
12:11
Nikko Ortiz
1 day agoCrashout 6 Rumble
23.1K3 -
 24:39
24:39
GritsGG
12 hours agoINSANE Ranked Game on Warzone!
2.42K1 -
 LIVE
LIVE
Lofi Girl
2 years agoSynthwave Radio 🌌 - beats to chill/game to
196 watching -
 5:52:00
5:52:00
Akademiks
8 hours agoWAR IN ATLANTA Episode 5. YOUNG THUG FIRST INTERVIEW about SNITCHING, GUNNA... BREAKS DOWN CRYING!
147K7 -
 7:30:25
7:30:25
SpartakusLIVE
11 hours agoVerdansk Duos w/ Nicky || Saturday Spartoons - Variety Later?!
51.7K1 -
 1:38:47
1:38:47
Badlands Media
1 day agoDevolution Power Hour Ep. 387: Trump, Epstein, Durham Mysteries, and North Korea Ops
84.3K21 -
 1:05:23
1:05:23
Man in America
15 hours agoSoaring Gold Exposes the Imminent Crash of the Old System w/ John Perez
43.3K7 -
 2:42:40
2:42:40
TruthStream with Joe and Scott
15 hours agoTHOMAS AND GROK: AI, Bible decodes, The JESUS Cube live 9/6 #487
29.9K6 -
 2:34:46
2:34:46
BlackDiamondGunsandGear
10 hours agoGet Prepped / After Hours Armory / LIVE SHOW /
20.2K1 -
 2:01:39
2:01:39
Tundra Tactical
8 hours ago $8.30 earned🛑LIVE NOW!! This spits in the face of the Second Amendment.🛑
31.2K8