Premium Only Content
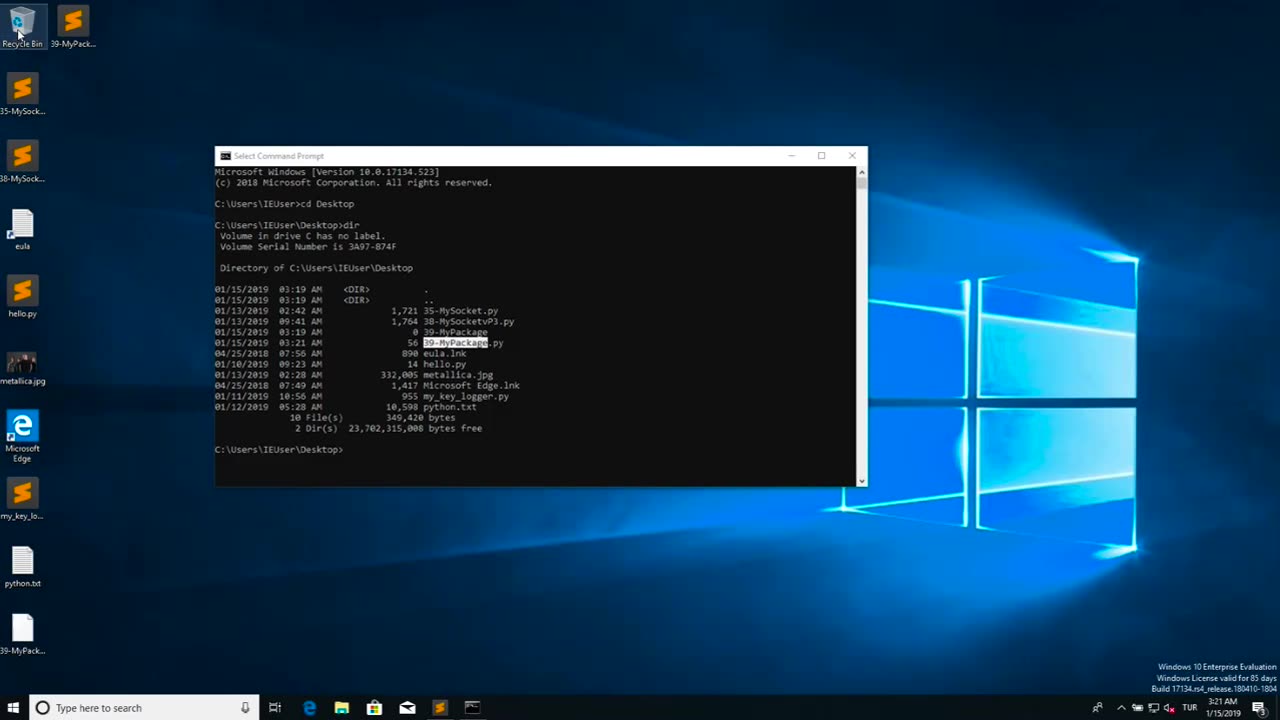
Chapter-39, LEC-2 | Malicious Files | #ethicalhacking #maliciousdiles #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Malicious files refer to digital files, such as software programs or documents, that are intentionally designed to harm or compromise the security of a computer, network, or device. These files may contain malicious code, also known as malware, which can be executed or triggered to perform malicious activities without the knowledge or consent of the user.
Malicious files can come in various forms, including viruses, worms, Trojans, ransomware, spyware, adware, and other types of malware. They are typically disguised as legitimate files or software to deceive users into downloading or executing them. Once the malicious file is executed or opened, it can spread throughout the system, exploit vulnerabilities, steal sensitive information, disrupt operations, or cause other types of damage.
Malicious files are often distributed through various means, such as infected email attachments, compromised websites, infected USB drives, social engineering tactics, and other methods. They can target any type of device or operating system, including computers, servers, smartphones, tablets, and IoT (Internet of Things) devices.
The consequences of encountering and executing malicious files can be severe, ranging from data breaches and financial loss to privacy violations, system downtime, and reputational damage. Therefore, it is crucial to implement robust cybersecurity measures, such as using antivirus software, keeping software and systems updated, being cautious while downloading or opening files, and practicing safe online behavior, to protect against malicious files and other cyber threats.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
Wendy Bell Radio
6 hours agoSunday, Bloody Sunday
12,727 watching -
 LIVE
LIVE
GritsGG
2 hours agoRumble Customs! 3515 Ws! 🫡!
1,199 watching -
 LIVE
LIVE
Lofi Girl
2 years agoSynthwave Radio 🌌 - beats to chill/game to
347 watching -
 LIVE
LIVE
FyrBorne
13 hours ago🔴Warzone M&K Sniping: Finding Season 5's Best Strafe ARs
170 watching -
 4:47:50
4:47:50
The Why Files
2 days agoCOMPILATION: UFOs and Aliens Vol.2 | They are NOT our friends
75.7K51 -
 54:47
54:47
Side Scrollers Podcast
1 day agoSide Scroller Presents KING OF THE KART | MASSIVE MARIO KART TOURNAMENT
145K10 -
 14:47
14:47
GritsGG
19 hours agoRumble Tournament Dubular! Rebirth Island Custom Tournament!
50.4K3 -
 LIVE
LIVE
CassaiyanGaming
2 hours agoClean Water Charity Stream Day 1 - Black Ops 6 Level Grinding
98 watching -
 LIVE
LIVE
PudgeTV
4 hours ago🟣 Greak: Memories of Azur | Gaming on Rumble | September Charity Water Campaign
92 watching -
 11:13:31
11:13:31
LarryDickmanGaming
12 hours agoI am what I am and that's all that I am.
12.5K