Premium Only Content
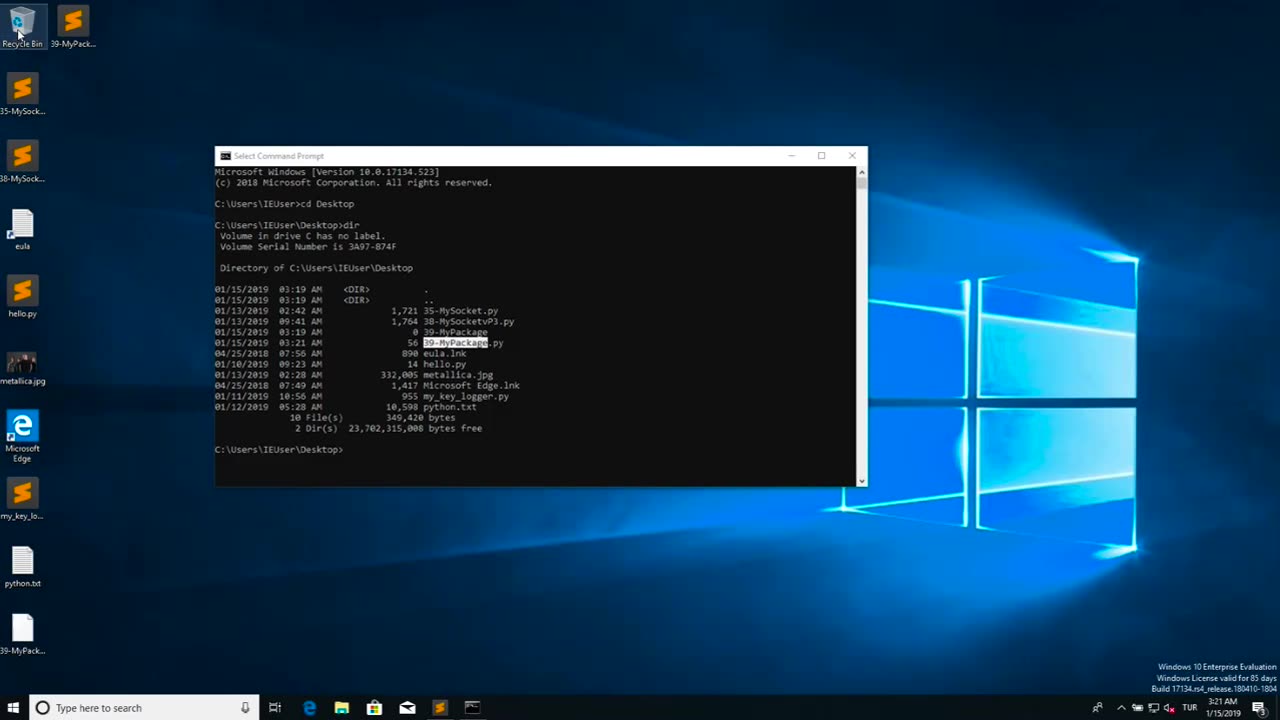
Chapter-39, LEC-2 | Malicious Files | #ethicalhacking #maliciousdiles #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Malicious files refer to digital files, such as software programs or documents, that are intentionally designed to harm or compromise the security of a computer, network, or device. These files may contain malicious code, also known as malware, which can be executed or triggered to perform malicious activities without the knowledge or consent of the user.
Malicious files can come in various forms, including viruses, worms, Trojans, ransomware, spyware, adware, and other types of malware. They are typically disguised as legitimate files or software to deceive users into downloading or executing them. Once the malicious file is executed or opened, it can spread throughout the system, exploit vulnerabilities, steal sensitive information, disrupt operations, or cause other types of damage.
Malicious files are often distributed through various means, such as infected email attachments, compromised websites, infected USB drives, social engineering tactics, and other methods. They can target any type of device or operating system, including computers, servers, smartphones, tablets, and IoT (Internet of Things) devices.
The consequences of encountering and executing malicious files can be severe, ranging from data breaches and financial loss to privacy violations, system downtime, and reputational damage. Therefore, it is crucial to implement robust cybersecurity measures, such as using antivirus software, keeping software and systems updated, being cautious while downloading or opening files, and practicing safe online behavior, to protect against malicious files and other cyber threats.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 3:40
3:40
DecoyVoice
1 year agoThailand doesn't have time for unemployed behavior
15.7K10 -
 11:09
11:09
Warren Smith - Secret Scholar Society
8 months agoThis Interview Changed How I See the World
32K11 -
 2:05:07
2:05:07
Inverted World Live
5 hours agoDemon Dolls and Doomsday Fish | Ep. 52
79.2K6 -
 1:31:12
1:31:12
"What Is Money?" Show
1 day agoBuy Bitcoin for Your Bloodline w/ Robert Breedlove (WiM589)
28.1K1 -
 6:50
6:50
Dr. Nick Zyrowski
22 days agoApple Cider Vinegar Fasting Drink - Fasting Accelerator
22.7K3 -
 1:07:48
1:07:48
Man in America
4 hours ago🚨 Plandemic 2.0: The July 4th Bioterror Plot & Palantir’s Master Plan w/ Dr. David Martin
48.5K29 -
 1:43:07
1:43:07
Tucker Carlson
1 day agoBishop Barron on the New Pope, the Foolishness of Atheism, and Why Young Men Are Turning to Christ
211K203 -
 3:24:07
3:24:07
Barry Cunningham
7 hours agoJD Vance And Marco Rubio Speak at American Compass Fifth Anniversary Gala | And More News!
72.2K31 -
 2:52:45
2:52:45
TimcastIRL
7 hours agoTrump Admin ARRESTS Boulder Terrorists ENTIRE FAMILY, Preps Deportations | Timcast IRL
193K104 -
 2:40:48
2:40:48
RiftTV/Slightly Offensive
9 hours agoBig, Beautiful SCAM? Elon FLIPS on Trump for WASTEFUL Bill | The Rift | Guests: Ed Szall + Matt Skow
61.8K17