Premium Only Content
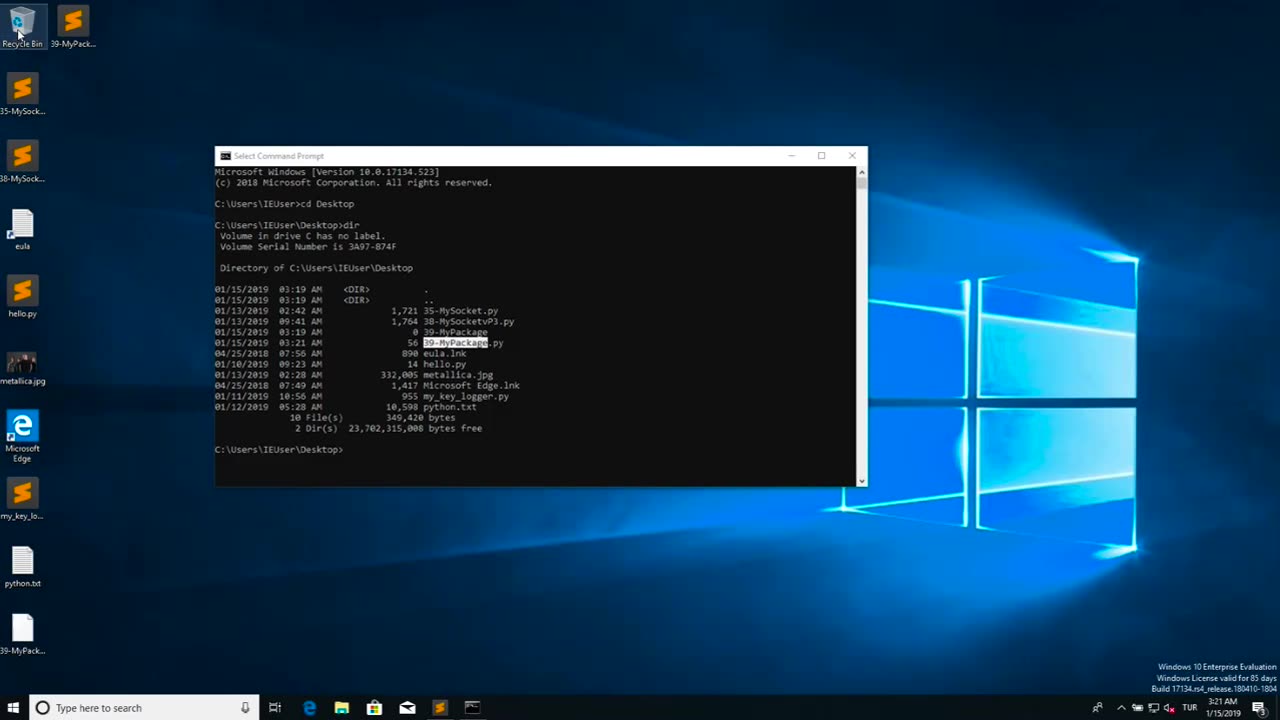
Chapter-39, LEC-2 | Malicious Files | #ethicalhacking #maliciousdiles #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Malicious files refer to digital files, such as software programs or documents, that are intentionally designed to harm or compromise the security of a computer, network, or device. These files may contain malicious code, also known as malware, which can be executed or triggered to perform malicious activities without the knowledge or consent of the user.
Malicious files can come in various forms, including viruses, worms, Trojans, ransomware, spyware, adware, and other types of malware. They are typically disguised as legitimate files or software to deceive users into downloading or executing them. Once the malicious file is executed or opened, it can spread throughout the system, exploit vulnerabilities, steal sensitive information, disrupt operations, or cause other types of damage.
Malicious files are often distributed through various means, such as infected email attachments, compromised websites, infected USB drives, social engineering tactics, and other methods. They can target any type of device or operating system, including computers, servers, smartphones, tablets, and IoT (Internet of Things) devices.
The consequences of encountering and executing malicious files can be severe, ranging from data breaches and financial loss to privacy violations, system downtime, and reputational damage. Therefore, it is crucial to implement robust cybersecurity measures, such as using antivirus software, keeping software and systems updated, being cautious while downloading or opening files, and practicing safe online behavior, to protect against malicious files and other cyber threats.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 15:03
15:03
Dad Saves America
11 hours ago $0.81 earnedHow the Department of Education Hijacked Our Schools - Poisoning of the American Mind: Pt 3
22K3 -
 14:06
14:06
Silver Dragons
14 hours agoBullion Dealer Reacts to Silver Price TRIPLING in 5 Years
3.96K4 -
 28:31
28:31
Anthony Rogers
13 hours agoBOWLING FOR SOUP interview
3.92K1 -
 17:12
17:12
Nate The Lawyer
2 days ago $1.65 earnedTrans Swimmer Lia Thomas Stripped of Titles for Being a Man in Women’s Sports
22.4K19 -
 12:17
12:17
Zoufry
18 hours agoThe Hunt For The Real Life James Bond
29.3K6 -
 24:05
24:05
DeVory Darkins
8 hours ago $10.93 earnedTrump HUMILIATES Jerome Powell in TENSE moment... Columbia University surrenders
105K71 -
 14:17
14:17
Doc Rich
5 days agoLefties Losing It Once Again
31K35 -
 25:31
25:31
Liberty Hangout
1 day agoMAGA Crashes Pathetic Anti-ICE Rally
103K56 -
 2:02:26
2:02:26
Inverted World Live
10 hours agoUS Soldiers Saw Non-Humans in Suffolk, The Rendlesham Forest Incident | Ep. 80
153K24 -
 6:42:47
6:42:47
Akademiks
11 hours agoICE MAN EPISODE 2 tonight. NEW NBA YOUNGBOY 'MASA' TONIGHT. BIG AKADEMIKS #2 MEDIA PERSONALITY 2025.
98.3K5