Premium Only Content
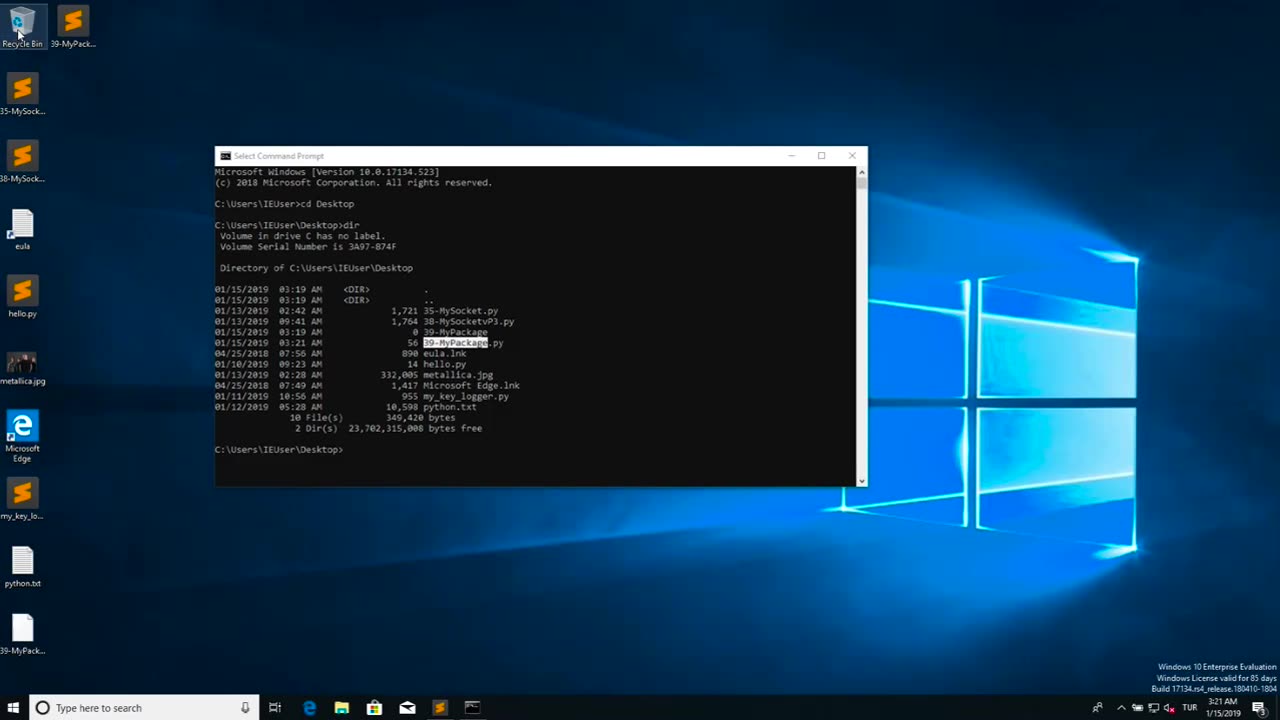
Chapter-39, LEC-2 | Malicious Files | #ethicalhacking #maliciousdiles #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Malicious files refer to digital files, such as software programs or documents, that are intentionally designed to harm or compromise the security of a computer, network, or device. These files may contain malicious code, also known as malware, which can be executed or triggered to perform malicious activities without the knowledge or consent of the user.
Malicious files can come in various forms, including viruses, worms, Trojans, ransomware, spyware, adware, and other types of malware. They are typically disguised as legitimate files or software to deceive users into downloading or executing them. Once the malicious file is executed or opened, it can spread throughout the system, exploit vulnerabilities, steal sensitive information, disrupt operations, or cause other types of damage.
Malicious files are often distributed through various means, such as infected email attachments, compromised websites, infected USB drives, social engineering tactics, and other methods. They can target any type of device or operating system, including computers, servers, smartphones, tablets, and IoT (Internet of Things) devices.
The consequences of encountering and executing malicious files can be severe, ranging from data breaches and financial loss to privacy violations, system downtime, and reputational damage. Therefore, it is crucial to implement robust cybersecurity measures, such as using antivirus software, keeping software and systems updated, being cautious while downloading or opening files, and practicing safe online behavior, to protect against malicious files and other cyber threats.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 55:35
55:35
Dialogue works
22 hours ago $0.25 earnedJohn Helmer: The Moves Russia Is Making to OUTMANEUVER NATO
3.11K7 -
 36:25
36:25
Actual Justice Warrior
1 day agoAna RAGES At Destiny
24.3K20 -
 28:35
28:35
itsSeanDaniel
2 days ago"BBC is Lying" - British Patriot REVEALS THE TRUTH about Historic London Rally
13K16 -
 26:13
26:13
The Brett Cooper Show
2 days ago $4.45 earnedThe Dark Truth Behind Child Acting | Episode 65
74.7K21 -
 27:09
27:09
Liberty Hangout
9 days agoFooling Libs to AGREE Biden's Cages Were Worse
182K35 -
 1:42:04
1:42:04
RoxomTV
1 day agoBitcoin Airbnb, BlackRock Stacks, Trump Smashes Fed | Blockchain Report
15.5K2 -
 1:27:18
1:27:18
Mike Rowe
2 days agoTheo Von Is Another Troubled White Boy | #449 | The Way I Heard It
104K34 -
 3:50:41
3:50:41
FreshandFit
13 hours agoFresh&Fit Taking These Girls To Therapy
182K78 -
 2:13:26
2:13:26
Badlands Media
14 hours agoDevolution Power Hour Ep. 390 - Political Warfare, Jimmy Kimmel & ANTIFA
107K31 -
 2:43:56
2:43:56
TimcastIRL
10 hours agoJimmy Kimmel FIRED, ABC Pulls Show Over Charlie Kirk Assassination Comments | Timcast IRL
397K227