Premium Only Content
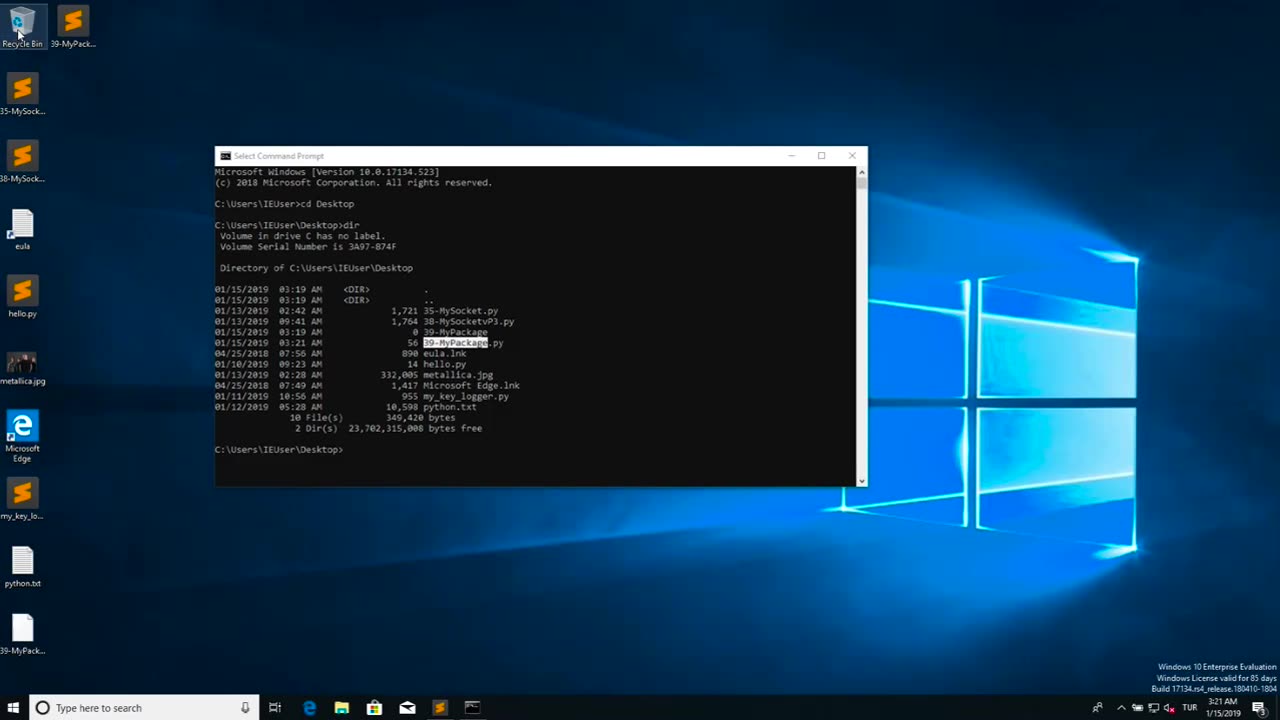
Chapter-39, LEC-2 | Malicious Files | #ethicalhacking #maliciousdiles #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Malicious files refer to digital files, such as software programs or documents, that are intentionally designed to harm or compromise the security of a computer, network, or device. These files may contain malicious code, also known as malware, which can be executed or triggered to perform malicious activities without the knowledge or consent of the user.
Malicious files can come in various forms, including viruses, worms, Trojans, ransomware, spyware, adware, and other types of malware. They are typically disguised as legitimate files or software to deceive users into downloading or executing them. Once the malicious file is executed or opened, it can spread throughout the system, exploit vulnerabilities, steal sensitive information, disrupt operations, or cause other types of damage.
Malicious files are often distributed through various means, such as infected email attachments, compromised websites, infected USB drives, social engineering tactics, and other methods. They can target any type of device or operating system, including computers, servers, smartphones, tablets, and IoT (Internet of Things) devices.
The consequences of encountering and executing malicious files can be severe, ranging from data breaches and financial loss to privacy violations, system downtime, and reputational damage. Therefore, it is crucial to implement robust cybersecurity measures, such as using antivirus software, keeping software and systems updated, being cautious while downloading or opening files, and practicing safe online behavior, to protect against malicious files and other cyber threats.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
Benny Johnson
1 hour agoHow To Fix The Biggest Crisis In America: Housing | Saving The American Dream for Young People 🇺🇸
2,461 watching -
 LIVE
LIVE
Graham Allen
2 hours agoTrump: “SEDITIOUS BEHAVIOR, punishable by DEATH!” Dems LOSING It! + Candace Owens PRANKED Live!!
2,034 watching -
 LIVE
LIVE
Matt Kohrs
10 hours agoMarkets Tilted, OPEX Chaos & Payday Friday || Live Trading
648 watching -
 LIVE
LIVE
Badlands Media
9 hours agoBadlands Daily Nov. 21, 2025
2,977 watching -
 LIVE
LIVE
Wendy Bell Radio
5 hours agoOh HELL NO
7,351 watching -
 LIVE
LIVE
Major League Fishing
8 days agoLIVE! - Fishing Clash Team Series: Summit Cup - Day 6
171 watching -
 30:49
30:49
MetatronHistory
16 hours agoThe Truth about Women Warriors Based on Facts, Evidence and Sources
1333 -
 15:17
15:17
IsaacButterfield
6 hours ago $0.22 earnedAustralia’s Most Hated Politician
4922 -
 4:28
4:28
MudandMunitions
12 hours agoSHOT Show 2026 Is Locked In and I’m a Gundie Nominee!
31 -
 1:19:44
1:19:44
Chad Prather
19 hours agoWhen God Shakes the Room: Bold Faith in a Fearful World
52.7K41