Premium Only Content
Chapter-38, LEC-4 | Running Commands | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
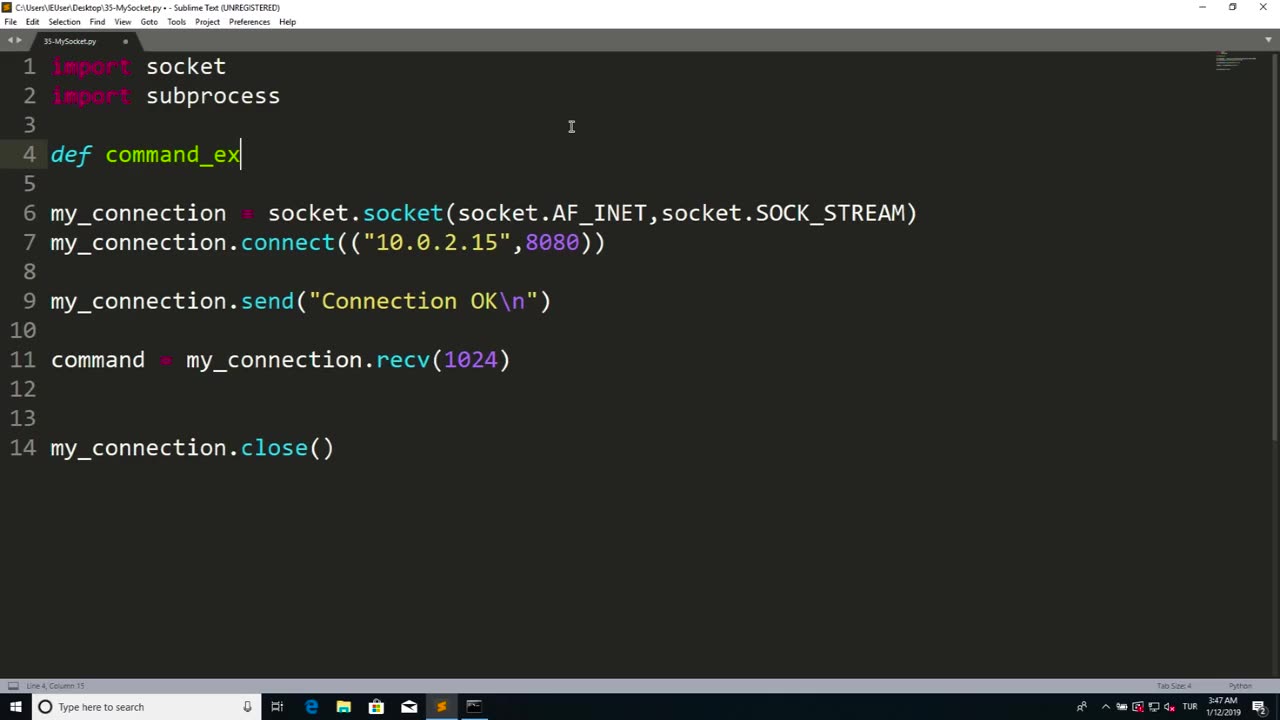
Running commands refers to the process of executing instructions or commands in a computer system or software to perform specific tasks or operations. Commands are typically entered into a command-line interface or terminal, which allows users to interact with a computer system directly through text-based commands.
Running commands can be used for a wide range of purposes, including system administration, software configuration, troubleshooting, automation, and more. Commands can be used to manipulate files and directories, configure settings, install or uninstall software, manage processes, retrieve information, and perform other operations depending on the specific software or system being used.
Running commands requires knowledge of the specific command syntax, options, and parameters for the software or system being used. It is important to understand the implications and potential consequences of the commands being executed, as they can impact the performance, stability, and security of the system or software.
Proper caution and authorization must be exercised when running commands, as some commands may have elevated privileges and can potentially cause harm or damage to the system or data if used improperly or without proper authorization. It is essential to follow best practices, such as using appropriate permissions, verifying the source and integrity of commands, and testing commands in a safe and controlled environment.
Running commands can be a powerful tool in managing computer systems and software efficiently and effectively. However, it requires knowledge, expertise, and responsible use to ensure that commands are executed safely and securely, and that the intended tasks or operations are performed accurately and without any unintended consequences. Always exercise caution, follow proper authorization procedures, and adhere to best practices when running commands in any computer system or software environment.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 6:29
6:29
Clickbait Wasteland
16 hours agoCUOMO vs ZOHRAN: Who do New Yorkers Want as the Next Mayor?
113 -
 22:10
22:10
IsaacButterfield
9 hours ago $0.18 earnedUnhinged White Woman Hates White People
89612 -
 1:04:05
1:04:05
Timcast
2 hours agoThe TAMURA Conspiracy, Theory Says Blackstone WAS The Target Over Israel, NOT NFL
125K63 -
 2:15:27
2:15:27
Steven Crowder
5 hours ago🔴 NYC Shooting Exposes Massive Hypocrisy From Mamdani & the Left
285K290 -
 1:36:20
1:36:20
The Mel K Show
3 hours agoMORNINGS WITH MEL K - An Engaged Fed Up Citizenry is Finally Moving the Needle Towards Accountability 7-29-25
24.6K15 -
 1:17:30
1:17:30
Rebel News
1 hour agoByelection ballot drama, Ford flips on jobs for asylum seekers, Pipeline problems | Rebel Roundup
4.1K1 -
 DVR
DVR
The Tom Renz Show
1 hour agoThe Manhattan Shooting, Vax Accountability, & Trump's Trade Deals In Crypto World
4.73K1 -
 DVR
DVR
TheAlecLaceShow
2 hours agoGuest: George Papadopoulos | NYC Shooting In A Gun Free Zone | The Alec Lace Show
2.9K1 -
 LIVE
LIVE
LFA TV
16 hours agoLFA TV ALL DAY STREAM - TUESDAY 7/29/25
3,027 watching -
 1:10:32
1:10:32
The Rubin Report
3 hours agoMidtown Tower Shooting Causes Resurfaced Bill Maher Clip to Go Viral
60K76