Premium Only Content
Chapter-38, LEC-4 | Running Commands | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
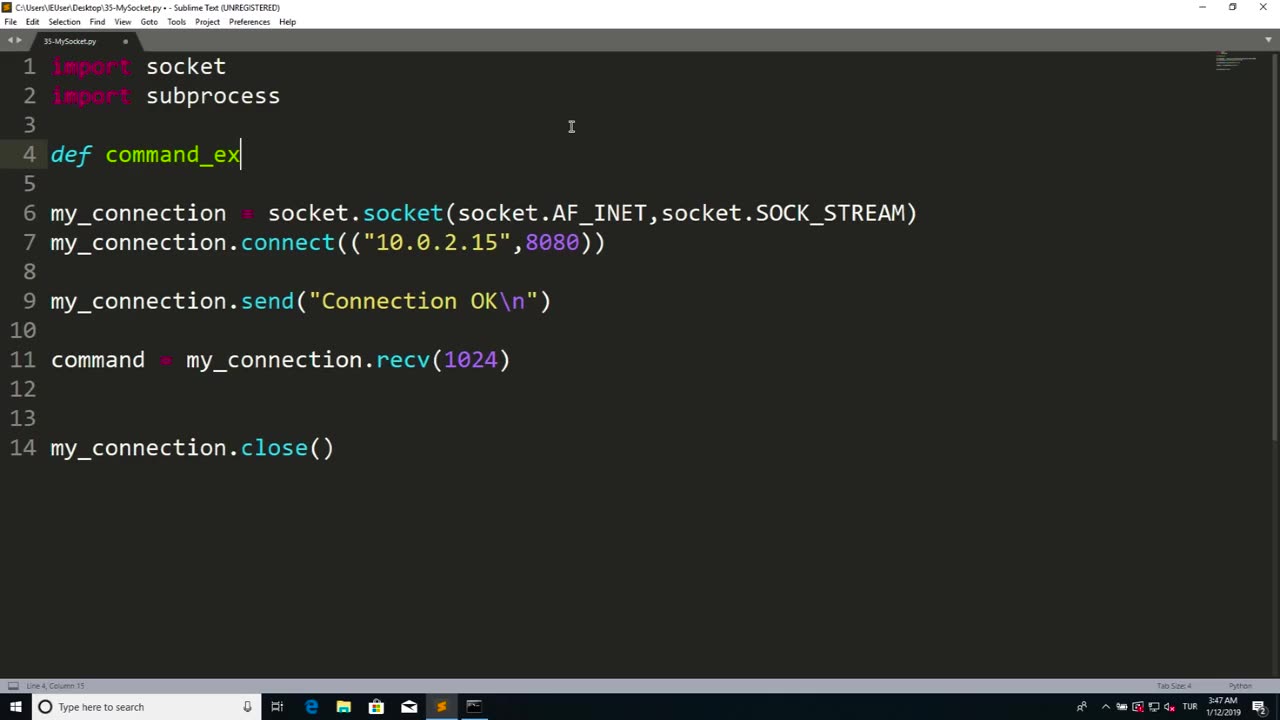
Running commands refers to the process of executing instructions or commands in a computer system or software to perform specific tasks or operations. Commands are typically entered into a command-line interface or terminal, which allows users to interact with a computer system directly through text-based commands.
Running commands can be used for a wide range of purposes, including system administration, software configuration, troubleshooting, automation, and more. Commands can be used to manipulate files and directories, configure settings, install or uninstall software, manage processes, retrieve information, and perform other operations depending on the specific software or system being used.
Running commands requires knowledge of the specific command syntax, options, and parameters for the software or system being used. It is important to understand the implications and potential consequences of the commands being executed, as they can impact the performance, stability, and security of the system or software.
Proper caution and authorization must be exercised when running commands, as some commands may have elevated privileges and can potentially cause harm or damage to the system or data if used improperly or without proper authorization. It is essential to follow best practices, such as using appropriate permissions, verifying the source and integrity of commands, and testing commands in a safe and controlled environment.
Running commands can be a powerful tool in managing computer systems and software efficiently and effectively. However, it requires knowledge, expertise, and responsible use to ensure that commands are executed safely and securely, and that the intended tasks or operations are performed accurately and without any unintended consequences. Always exercise caution, follow proper authorization procedures, and adhere to best practices when running commands in any computer system or software environment.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 2:11:41
2:11:41
Badlands Media
13 hours agoDEFCON ZERQ Ep. 016: Shadow Governments, Ancient Tech & the Spiritual War for Humanity
81.9K59 -
 2:09:24
2:09:24
Inverted World Live
7 hours agoRats Have Learned to Hunt Bats | Ep. 135
31.2K15 -
 2:48:01
2:48:01
TimcastIRL
8 hours agoLIVE Election Coverage: Polling Stations SWATTED, Bomb Threats Called In | Timcast IRL
254K177 -
 3:30:07
3:30:07
Barry Cunningham
8 hours agoBREAKING NEWS: COUNTDOWN TO COMMUNISM! ELECTION RESULTS SHOW!
59.5K47 -
 2:11:28
2:11:28
DeVory Darkins
8 hours agoLIVE NOW: 2025 Election results and Exit Polls AMA
70K46 -
 2:34:04
2:34:04
DLDAfterDark
6 hours ago $0.08 earnedJust Another Tuesday - In Virginia - The Governor's Race & Glock Talk
29.3K7 -
 3:21:38
3:21:38
The Charlie Kirk Show
9 hours agoJUDGMENT DAY 2025: The Election Results Stream
200K82 -
 3:51:07
3:51:07
MattMorseTV
10 hours ago $0.82 earned🔴Election Day LIVE COVERAGE.🔴
99.2K49 -
 1:16:51
1:16:51
Flyover Conservatives
1 day agoSHOCKING DATA REVEALS: Young Voters Are Done With the Old GOP - Mark Mitchell, Rasmussen Reports | FOC Show
42.8K17 -
 1:15:28
1:15:28
Sarah Westall
10 hours agoGrooming is Protected and Encouraged by the System – Michelle Peterson and Mike Adamovich
35.9K10