Premium Only Content
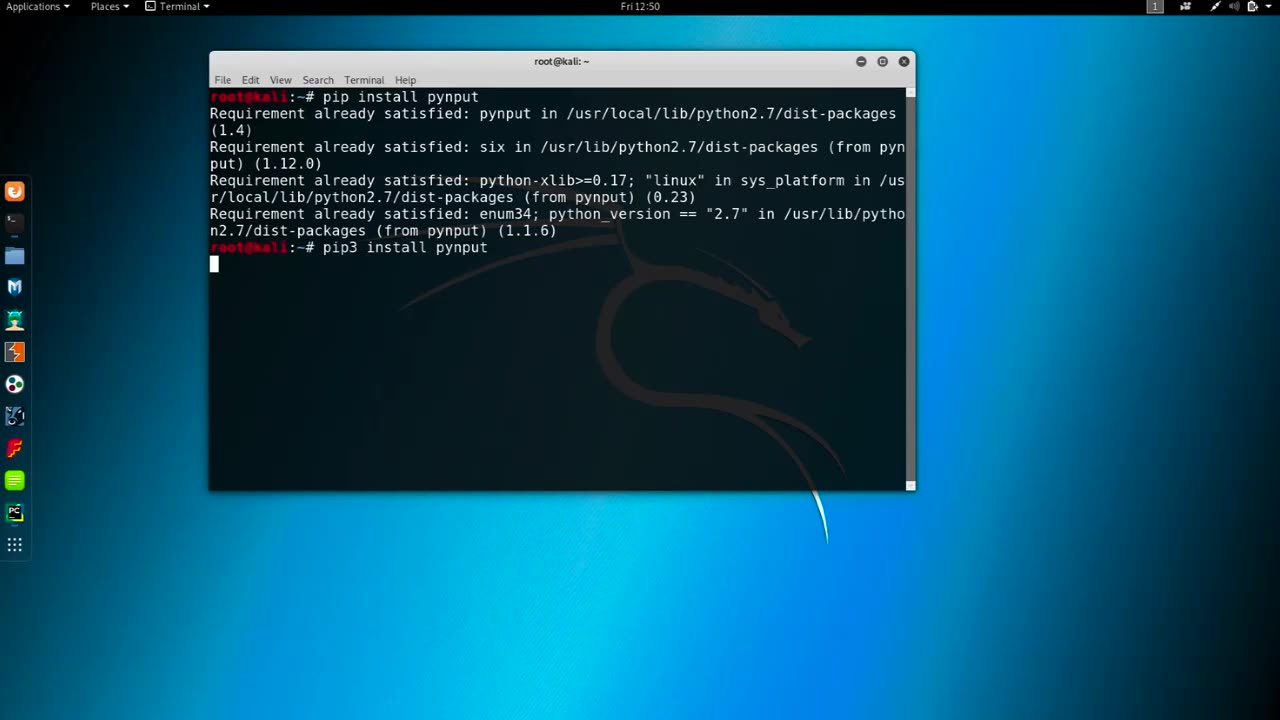
Chapter-37, LEC-4 | Logging Keyboards | #education #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Logging keyboards, also known as keyboard loggers or keystroke loggers, are software or hardware devices that capture and record all keystrokes made on a computer or mobile device's keyboard. They are used for monitoring or surveillance purposes and can capture every key pressed, including letters, numbers, special characters, and function keys, as well as other activities such as mouse movements, screenshots, and websites visited.
Keyboard loggers can operate in stealth mode, meaning they can run in the background without the user's knowledge or consent, and log all keystrokes made on the device. They can capture a wide range of information, including passwords, usernames, credit card numbers, chat messages, and other sensitive data that is entered using the keyboard.
Keyboard loggers may be used for both legitimate and malicious purposes. Legitimate uses include monitoring employee activity in the workplace, parental control to monitor children's online activities, and data recovery. However, keyboard loggers can also be used maliciously for stealing personal information, committing identity theft, financial fraud, and other cybercrimes.
It is essential to note that using keyboard loggers without proper authorization is illegal in many jurisdictions, and ethical considerations should always be taken into account when using them for any purpose. Users should always be informed and give explicit consent before their activities are monitored, and appropriate security measures should be in place to protect the data collected by keyboard loggers.
It is important to use keyboard loggers responsibly and within the legal and ethical boundaries, ensuring that privacy rights are respected, and data security is maintained at all times. Proper consent, transparency, and compliance with applicable laws and regulations are crucial when using keyboard loggers for any purpose.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
MattMorseTV
3 hours ago $13.82 earned🔴Election Day LIVE COVERAGE.🔴
2,171 watching -
 UPCOMING
UPCOMING
Sarah Westall
2 hours agoGrooming is Protected and Encouraged by the System – Michelle Peterson and Mike Adamovich
634 -
 LIVE
LIVE
Akademiks
26 minutes agoKendrick tries to Flip the Bots on DRAKE? WHo Beats Jay z in a verzuz. Blueface finally free!
928 watching -
 LIVE
LIVE
Professor Nez
5 hours ago🚨ELECTION NIGHT 2025 LIVE! Massive Upsets Brewing in New York, New Jersey & Virginia!
202 watching -
 LIVE
LIVE
Due Dissidence
8 hours agoLIVE: ELECTION RESULTS From NYC, NJ, and VA - Trump Approval CRATERS, Kash's Private Jet CRASH OUT
1,244 watching -
 12:50
12:50
Demons Row
1 hour agoBikers of New Jersey 💀🏍️ Pagans, Thunder Guards, and Thug Riders
3.88K1 -
 42:31
42:31
Stephen Gardner
5 hours ago🔥Old Obama Video RESURFACES - His Own Words CONDEMNED Him! Trump Gains MASSIVE Momentum!!
11.3K14 -
 LIVE
LIVE
LFA TV
23 hours agoLIVE & BREAKING NEWS! | TUESDAY 11/4/25
512 watching -
 1:03:37
1:03:37
BonginoReport
3 hours agoElection Night Showdown Spotlight - Nightly Scroll w/ Hayley Caronia (Ep.170)
99.6K25 -
 DVR
DVR
Edge of Wonder
3 hours agoSupernatural Forces & Giants Built Great Pyramid of Egypt
12.1K