Premium Only Content
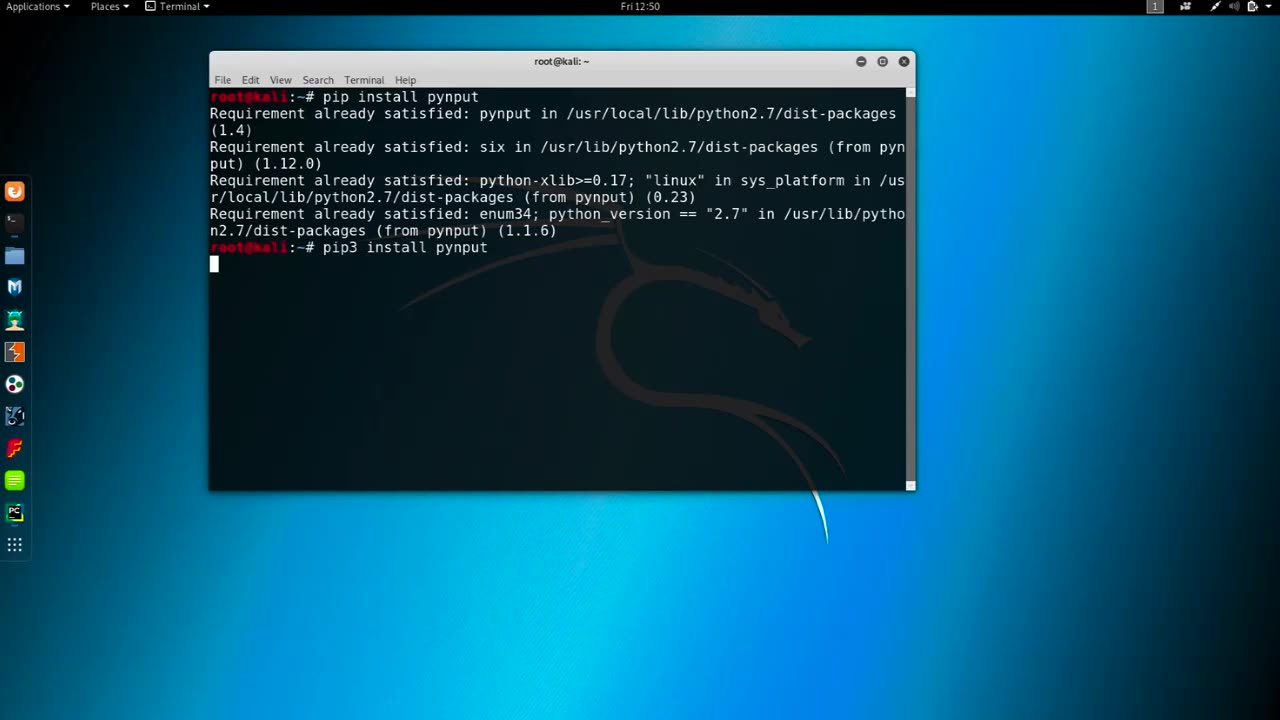
Chapter-37, LEC-4 | Logging Keyboards | #education #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Logging keyboards, also known as keyboard loggers or keystroke loggers, are software or hardware devices that capture and record all keystrokes made on a computer or mobile device's keyboard. They are used for monitoring or surveillance purposes and can capture every key pressed, including letters, numbers, special characters, and function keys, as well as other activities such as mouse movements, screenshots, and websites visited.
Keyboard loggers can operate in stealth mode, meaning they can run in the background without the user's knowledge or consent, and log all keystrokes made on the device. They can capture a wide range of information, including passwords, usernames, credit card numbers, chat messages, and other sensitive data that is entered using the keyboard.
Keyboard loggers may be used for both legitimate and malicious purposes. Legitimate uses include monitoring employee activity in the workplace, parental control to monitor children's online activities, and data recovery. However, keyboard loggers can also be used maliciously for stealing personal information, committing identity theft, financial fraud, and other cybercrimes.
It is essential to note that using keyboard loggers without proper authorization is illegal in many jurisdictions, and ethical considerations should always be taken into account when using them for any purpose. Users should always be informed and give explicit consent before their activities are monitored, and appropriate security measures should be in place to protect the data collected by keyboard loggers.
It is important to use keyboard loggers responsibly and within the legal and ethical boundaries, ensuring that privacy rights are respected, and data security is maintained at all times. Proper consent, transparency, and compliance with applicable laws and regulations are crucial when using keyboard loggers for any purpose.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 1:55:31
1:55:31
Steven Crowder
4 hours agoTucker Carlson & MAGA: Everyone is Missing the Point
316K232 -
 1:11:22
1:11:22
The Rubin Report
3 hours agoWatch Joe Rogan’s Face as Elon Musk Exposes How Dems Are Cheating in Plain Sight
46.6K58 -
 1:01:07
1:01:07
VINCE
4 hours agoThe Walls Are Closing In On The Deep State | Episode 160 - 11/03/25
218K140 -
 LIVE
LIVE
LFA TV
19 hours agoLIVE & BREAKING NEWS! | MONDAY 11/3/25
2,674 watching -
 1:31:18
1:31:18
Graham Allen
5 hours agoErika Fights Back: Vows To EXPOSE TRUTH & DEMANDS Trial Goes Public!! Left Says Her Grief Is FAKE!
146K81 -
 2:08:47
2:08:47
Badlands Media
9 hours agoBadlands Daily: November 3, 2025 – Tariff Wars, SNAP Panic & Brennan Gets Confronted
66.8K17 -
 2:59:32
2:59:32
Wendy Bell Radio
8 hours agoThings Will Get Worse Before They Get Better
92.4K112 -
 1:18:28
1:18:28
The Big Mig™
5 hours agoICE Will Use Private Bounty Hunters, LFG
37.6K13 -
 1:08:17
1:08:17
Chad Prather
12 hours agoHow to Get Along With People You Don’t Even Like (Most of the Time)
126K34 -
 1:45:29
1:45:29
MTNTOUGH Podcast w/ Dustin Diefenderfer
11 hours agoTaya + Colton Kyle: Can American Marriages Survive 2025? | MTNPOD #140
32.1K