Premium Only Content
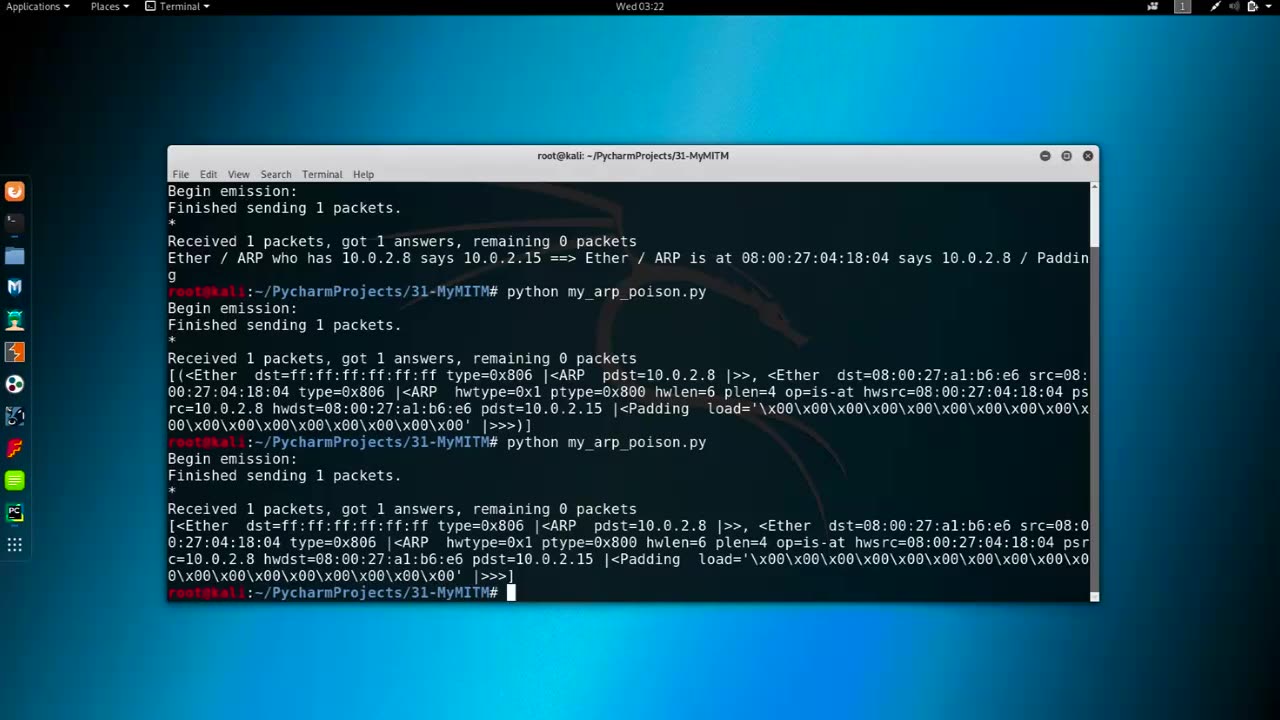
Chapter-35, LEC-5 | Getting MAC Address | #rumble #ethicalhacking #hacking #porthacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Getting MAC Address refers to the process of obtaining the Media Access Control (MAC) address of a network interface card (NIC) or a network-connected device. The MAC address, also known as the hardware address or physical address, is a unique identifier assigned to the NIC or network interface of a device at the factory, and it is used to uniquely identify a device within a network.
There are several methods to obtain the MAC address of a device:
Command-Line Interface (CLI): Many operating systems, such as Windows, macOS, Linux, and networking devices, provide command-line interfaces (CLI) that allow users to retrieve the MAC address using commands like "ipconfig" (Windows), "ifconfig" (macOS and Linux), or "show interfaces" (networking devices).
Graphical User Interface (GUI): Some operating systems, such as Windows and macOS, provide graphical user interfaces (GUI) that display the MAC address in the network settings or device properties.
Network Configuration or Management Tools: Network configuration or management tools, such as network monitoring software, network scanners, or network inventory tools, may have features to automatically detect and retrieve MAC addresses of devices within a network.
Physical Inspection: On some devices, the MAC address may be printed on a label or engraved on the NIC or device itself, making it possible to physically inspect the device to obtain its MAC address.
Network Protocol: Some network protocols, such as the Address Resolution Protocol (ARP) or the Dynamic Host Configuration Protocol (DHCP), may provide information about MAC addresses during network communication or device registration.
Obtaining MAC addresses can be useful for various networking tasks, such as troubleshooting, network monitoring, network access control, or device identification. However, it's important to note that MAC addresses can be easily spoofed or manipulated, and they should not be solely relied upon for device authentication or security purposes. Other security measures, such as encryption, authentication protocols, and access controls, should also be implemented to secure network communications and protect against unauthorized access.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
Pop Culture Crisis
2 hours agoCoca-Cola's WAR ON CHRISTMAS, Movie Press Tour CRINGE, Gen Z HATES Gen Z | Ep, 949
557 watching -
 16:30
16:30
Clintonjaws
17 hours ago $4.31 earned'The View's' Producer Stops Show & Forces Whoopie To Correct Lie
5.43K4 -
 1:10:24
1:10:24
Steve-O's Wild Ride! Podcast
5 days ago $0.38 earnedMatt McCusker Makes Steve-O Nervous | Wild Ride #272
2.84K1 -
 17:09
17:09
Bearing
9 hours agoHasan Goes NUCLEAR On Chat ☢️ ROASTED By JD Vance Over Dog Allegations 🚨
6.86K27 -
 LIVE
LIVE
The HotSeat With Todd Spears
1 hour agoEP 203: The Military "Whistleblower"
738 watching -
![[Ep 784] Election 2025: NYC is Screwed | Tatum Calls Out Kirk Conspiracists | Guest: Sam Anthony](https://1a-1791.com/video/fwe2/00/s8/1/U/Q/E/w/UQEwz.0kob-small-Ep-784-Election-2025-NYC-is.jpg) LIVE
LIVE
The Nunn Report - w/ Dan Nunn
1 hour ago[Ep 784] Election 2025: NYC is Screwed | Tatum Calls Out Kirk Conspiracists | Guest: Sam Anthony
175 watching -
 1:22:54
1:22:54
DeVory Darkins
4 hours agoTrump makes shocking announcement as Major ELECTION UPDATE drops after bomb threat
81.7K53 -
 10:11
10:11
Dr. Nick Zyrowski
8 days agoDoes Creatine CAUSE Hair Loss? (We All Got This Wrong)
6.85K2 -
 1:09:24
1:09:24
Timcast
4 hours agoZohran Mamdani BLAMES Trump Over Bomb Threats At Polling Locations
149K104 -
 3:09:52
3:09:52
Right Side Broadcasting Network
6 hours agoLIVE REPLAY: White House Press Secretary Karoline Leavitt Holds a Press Briefing - 11/4/25
69.8K14