Premium Only Content
Chapter-34, LEC-7 | Adding Features | #rumble #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
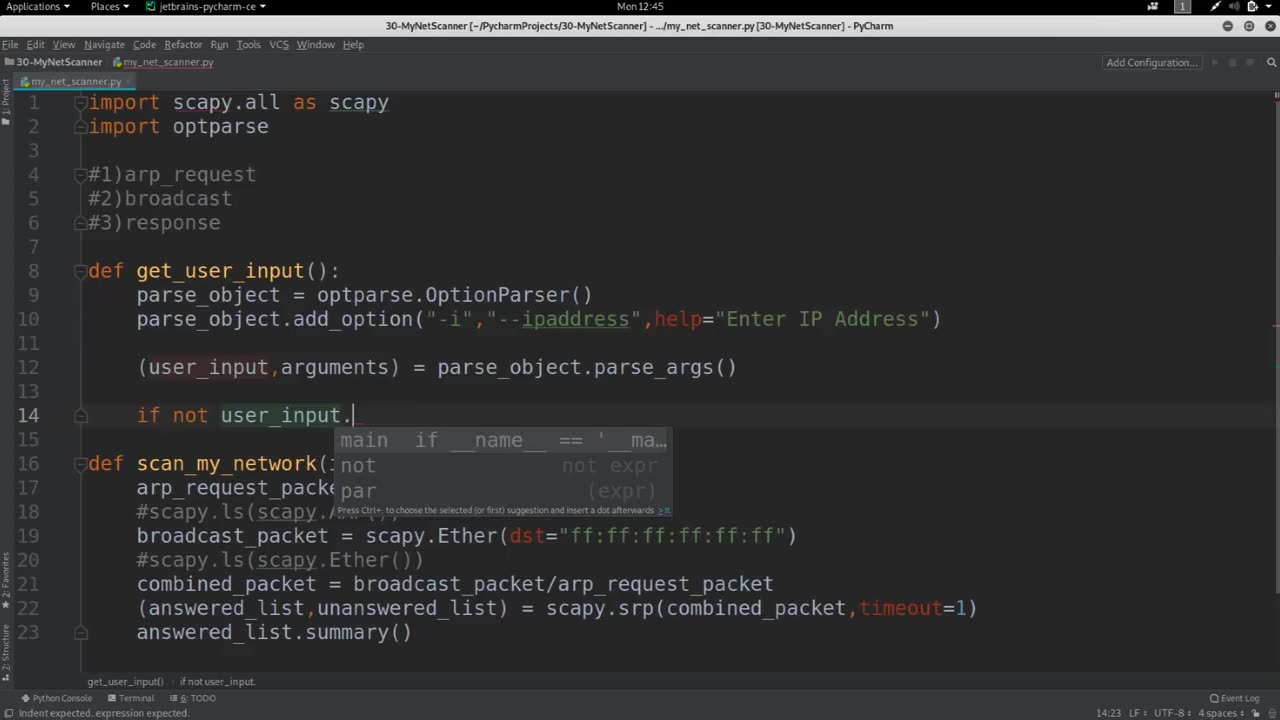
A network scanner is a powerful tool used by ethical hackers to identify vulnerabilities and weaknesses in computer networks. In this lecture, students learn how to enhance the capabilities of a network scanner by adding additional features to it.
The lecture begins with an overview of the importance of network scanning in the ethical hacking process. The instructor emphasizes the need for a comprehensive and reliable network scanner to effectively identify potential vulnerabilities in a target network. Students learn about the different types of network scans, such as port scanning, OS fingerprinting, and vulnerability scanning, and their significance in identifying weaknesses in a network.
Next, the lecture delves into the process of adding features to a network scanner. Students are introduced to various techniques and tools used in the development of network scanners, such as Python scripting, socket programming, and API integration. The instructor provides step-by-step instructions on how to modify and extend the functionalities of a network scanner, including customizing scan options, implementing new scanning techniques, and integrating with external databases for vulnerability data.
Furthermore, the lecture covers advanced topics in network scanning, such as evasion techniques to bypass network security measures, spoofing techniques to disguise the scanner's identity, and stealthy scanning techniques to avoid detection. Students learn about the ethical implications of using such techniques and the importance of obtaining proper authorization before conducting any network scanning activities.
Throughout the lecture, practical demonstrations and examples are provided to illustrate the concepts and techniques being taught. Students are encouraged to actively participate in hands-on exercises to gain practical experience in developing and customizing a network scanner with added features.
In summary, Lecture 7 of Chapter 34 in the Ethical Hacking Course focuses on enhancing the capabilities of a network scanner by adding features, including customization, integration with external databases, and advanced scanning techniques. The lecture emphasizes the ethical considerations and legal implications of network scanning and provides practical guidance on developing a powerful and reliable network scanner for ethical hacking purposes.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
The Quartering
1 hour agoEscape From New York, Harvard Bombers Caught, Trump DEFIES Court On SNAP, Bomb Threat On Plane!
18,973 watching -
 1:10:24
1:10:24
Steve-O's Wild Ride! Podcast
5 days ago $0.05 earnedMatt McCusker Makes Steve-O Nervous | Wild Ride #272
7501 -
 16:30
16:30
Clintonjaws
16 hours ago $0.18 earned'The View's' Producer Stops Show & Forces Whoopie To Correct Lie
93 -
 1:22:54
1:22:54
DeVory Darkins
2 hours agoTrump makes shocking announcement as Major ELECTION UPDATE drops after bomb threat
71.5K25 -
 17:09
17:09
Bearing
8 hours agoHasan Goes NUCLEAR On Chat ☢️ ROASTED By JD Vance Over Dog Allegations 🚨
2K24 -
 10:11
10:11
Dr. Nick Zyrowski
8 days agoDoes Creatine CAUSE Hair Loss? (We All Got This Wrong)
9121 -
 1:09:24
1:09:24
Timcast
3 hours agoZohran Mamdani BLAMES Trump Over Bomb Threats At Polling Locations
125K70 -
 3:09:52
3:09:52
Right Side Broadcasting Network
5 hours agoLIVE REPLAY: White House Press Secretary Karoline Leavitt Holds a Press Briefing - 11/4/25
53.6K10 -
 1:58:04
1:58:04
The Charlie Kirk Show
3 hours agoGo Vote! + Healthcare and the Shutdown | Dr. Oz, Baris | 11.4.2025
57.8K8 -
 58:49
58:49
The White House
4 hours agoPress Secretary Karoline Leavitt Briefs Members of the Media, Nov. 4, 2025
20.1K14