Premium Only Content
Chapter-34, LEC-3 | How Network Scanner Works | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
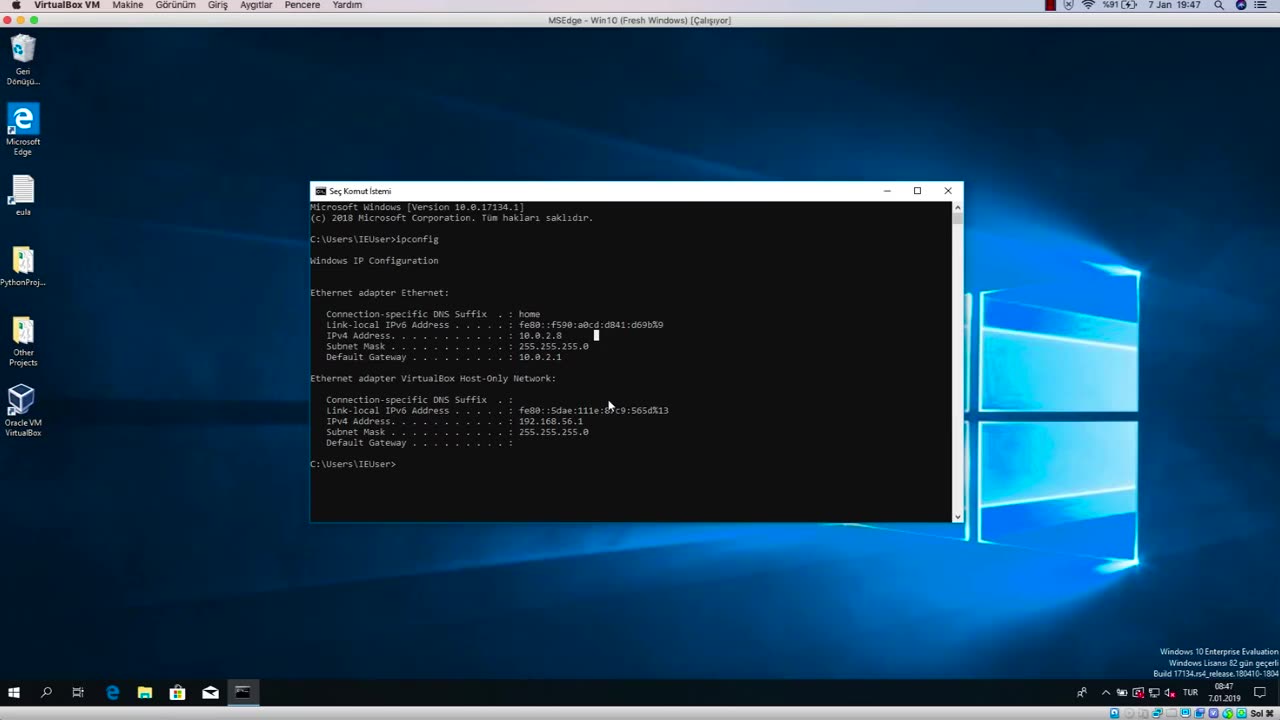
A network scanner is a tool used to examine and analyze computer networks to identify devices, systems, and potential vulnerabilities. Network scanners work by sending packets of data to specific IP addresses or network ranges and analyzing the responses received. Here is a general overview of how network scanners work:
Device Discovery: Network scanners start by scanning the network to discover devices that are connected to it. This is typically done by sending out broadcast messages or using various scanning techniques such as ping sweeps, ARP scans, or DNS queries to identify devices with active IP addresses.
Port Scanning: Once devices are discovered, network scanners perform port scanning to identify open ports on the devices. Ports are used for communication between devices, and open ports indicate services or applications that are running and accessible on a device. Port scanning helps identify potential entry points or vulnerabilities that can be exploited by malicious actors.
Service Detection: After identifying open ports, network scanners perform service detection to determine the type of service or application running on each open port. This is done by sending specific packets or queries to the open ports and analyzing the responses to identify the software or application running on that port. This information helps assess the security of the services and applications running on the devices.
Operating System Detection: Network scanners also attempt to detect the operating system (OS) running on each discovered device. This is done by sending packets or queries that can elicit responses with OS-specific information, such as TCP/IP fingerprinting or protocol analysis. Knowing the OS running on a device can help identify potential vulnerabilities or security weaknesses associated with that OS.
Vulnerability Scanning: Once devices, open ports, services, and operating systems are identified, network scanners may also perform vulnerability scanning. This involves comparing the information gathered against known vulnerabilities and weaknesses in software or configurations to identify potential vulnerabilities that could be exploited by attackers.
Reporting and Analysis: Finally, network scanners generate reports and provide analysis on the findings, which can include information on discovered devices, open ports, services, operating systems, and potential vulnerabilities. This information can be used by IT professionals and cybersecurity experts to assess the security posture of the network, identify potential weaknesses, and implement appropriate security measures.
It's important to note that network scanning should be performed responsibly and legally, with proper authorization and consent from network owners. Unauthorized or malicious network scanning can result in legal consequences and ethical concerns.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
Barry Cunningham
1 hour agoBREAKING NEWS: COUNTDOWN TO COMMUNISM! ELECTION RESULTS SHOW!
1,346 watching -
 UPCOMING
UPCOMING
DeVory Darkins
44 minutes agoLIVE NOW: 2025 Election results and Exit Polls AMA
55 -
 LIVE
LIVE
The Charlie Kirk Show
2 hours agoJUDGMENT DAY 2025: The Election Results Stream
8,323 watching -
 LIVE
LIVE
MattMorseTV
3 hours ago $13.82 earned🔴Election Day LIVE COVERAGE.🔴
2,166 watching -
 UPCOMING
UPCOMING
Sarah Westall
2 hours agoGrooming is Protected and Encouraged by the System – Michelle Peterson and Mike Adamovich
634 -
 LIVE
LIVE
Akademiks
26 minutes agoKendrick tries to Flip the Bots on DRAKE? WHo Beats Jay z in a verzuz. Blueface finally free!
931 watching -
 LIVE
LIVE
Professor Nez
5 hours ago🚨ELECTION NIGHT 2025 LIVE! Massive Upsets Brewing in New York, New Jersey & Virginia!
199 watching -
 LIVE
LIVE
Due Dissidence
8 hours agoLIVE: ELECTION RESULTS From NYC, NJ, and VA - Trump Approval CRATERS, Kash's Private Jet CRASH OUT
1,236 watching -
 12:50
12:50
Demons Row
1 hour agoBikers of New Jersey 💀🏍️ Pagans, Thunder Guards, and Thug Riders
3.88K1 -
 42:31
42:31
Stephen Gardner
5 hours ago🔥Old Obama Video RESURFACES - His Own Words CONDEMNED Him! Trump Gains MASSIVE Momentum!!
11.3K14