Premium Only Content
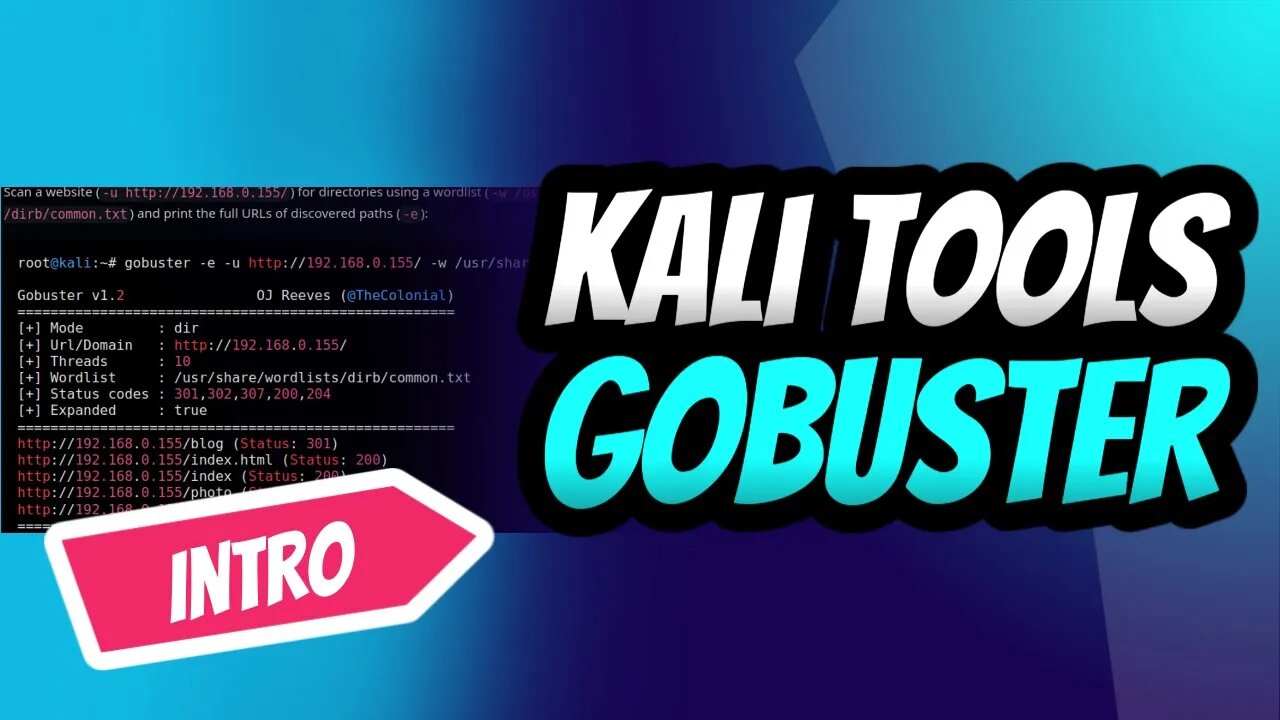
GoBuster for Ultimate Kali Linux Reconnaissance
Introduction into the power of GoBuster, the ultimate directory brute-forcing tool on Kali Linux! 🚀🔥 Learn how to reveal hidden directories and files, crack passwords, and uncover vulnerabilities with ease. Follow our step-by-step guide to mastering GoBuster and supercharge your ethical hacking skills.👩💻👨💻
Don't miss out on this essential intro for every aspiring hacker and penetration tester. Subscribe now, and let's get our hands dirty with GoBuster! 💪🔓
#KaliLinux #GoBuster #EthicalHacking #PenTesting #CyberSecurity #Reconnaissance #InfoSec #HiddenDirectories #BruteForce 💻🌐🔧🔒🕵️♀️🕵️♂️
Stay tuned for an upcoming detailed tutorial that will transform you into a GoBuster pro in no time! 🌟🔧
Subscribe and hit the bell icon to make sure you don't miss this comprehensive guide, and unlock your full potential as an ethical hacker and penetration tester. Let's explore the world of GoBuster together! 🌍🔓💡
If you look at the help command, we can see that Gobuster has a few modes.
dir — Directory enumeration mode.
dns — Subdomain enumeration mode.
fuzz — Fuzzing mode.
s3 — S3 enumeration mode.
v host — V host enumeration mode.
Gobuster is a fast brute-force tool to discover hidden URLs, files, and directories within websites. This will help us to remove/secure hidden files and sensitive data.
Gobuster also helps in securing sub-domains and virtual hosts from being exposed to the internet. Overall, Gobuster is a fantastic tool to help you reduce your application’s attack surface.
You can use the following steps to prevent and stop brute-force attacks on your web application.
Audit yourself: Use Gobuster on your own applications and perform an audit. This will help you find the information that will be visible to the attackers.
Apply security policies: To prevent resources like S3 from being exposed on the internet, use AWS bucket policies to prevent unauthorized access.
Use bot protection solutions: Bot protection services like Cloudflare will stop any brute-force attacks making it incredibly difficult to attack your web application.
-
 1:43
1:43
Dev Null - | Hacking| CyberSecurity| Cybersecurity education
1 year agoSelecting a Laptop for Ethical Hacking Success
1721 -
 1:40:52
1:40:52
Russell Brand
4 hours agoCalifornia Burns! Who’s Really to Blame? – SF519
117K52 -
 1:27:57
1:27:57
The Officer Tatum
3 hours agoLIVE: Pete Hegseth DESTROYS Leftist at Confirmation Hearing! + MORE Officer Tatum Show EP 41
41.4K63 -
 1:58:28
1:58:28
The Charlie Kirk Show
4 hours agoThe Hegseth Confirmation Hearing | Larsen, Dr. Marshall, Halperin | 1.14.2025
150K97 -
 12:15
12:15
Reforge Gaming
5 hours agoPlayStation has a First Party Problem
37.5K2 -
 7:12
7:12
Rethinking the Dollar
5 hours agoIs the Catalyst For the Next Financial Crisis...Homeowners Insurance?
30K3 -
 2:02:13
2:02:13
LFA TV
21 hours agoHEGSETH HEARING LIVE! | LIVE FROM AMERICA 1.14.25 11am
92.1K33 -
 46:04
46:04
Grant Stinchfield
4 hours ago $5.61 earnedDevious Jack Smith Vindicates President Trump with One Line the Media Won't Repeat
44.9K5 -
 18:12
18:12
ROSE UNPLUGGED
1 day agoTom Homan: They Can't Cancel Me- I'm Not Going Away
25.3K -
 1:02:03
1:02:03
TheAlecLaceShow
6 hours agoNavy SEALs March on Washington for Pete Hegseth | The Alec Lace Show
21.2K8