Premium Only Content
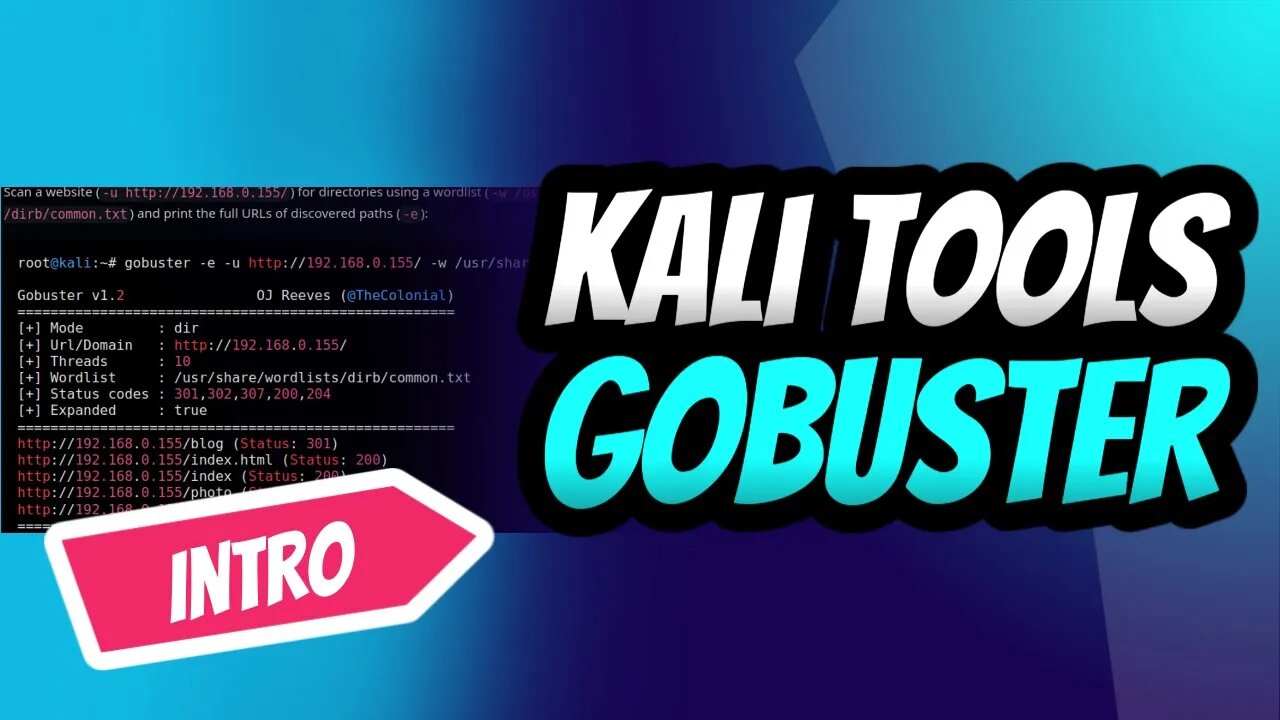
GoBuster for Ultimate Kali Linux Reconnaissance
Introduction into the power of GoBuster, the ultimate directory brute-forcing tool on Kali Linux! 🚀🔥 Learn how to reveal hidden directories and files, crack passwords, and uncover vulnerabilities with ease. Follow our step-by-step guide to mastering GoBuster and supercharge your ethical hacking skills.👩💻👨💻
Don't miss out on this essential intro for every aspiring hacker and penetration tester. Subscribe now, and let's get our hands dirty with GoBuster! 💪🔓
#KaliLinux #GoBuster #EthicalHacking #PenTesting #CyberSecurity #Reconnaissance #InfoSec #HiddenDirectories #BruteForce 💻🌐🔧🔒🕵️♀️🕵️♂️
Stay tuned for an upcoming detailed tutorial that will transform you into a GoBuster pro in no time! 🌟🔧
Subscribe and hit the bell icon to make sure you don't miss this comprehensive guide, and unlock your full potential as an ethical hacker and penetration tester. Let's explore the world of GoBuster together! 🌍🔓💡
If you look at the help command, we can see that Gobuster has a few modes.
dir — Directory enumeration mode.
dns — Subdomain enumeration mode.
fuzz — Fuzzing mode.
s3 — S3 enumeration mode.
v host — V host enumeration mode.
Gobuster is a fast brute-force tool to discover hidden URLs, files, and directories within websites. This will help us to remove/secure hidden files and sensitive data.
Gobuster also helps in securing sub-domains and virtual hosts from being exposed to the internet. Overall, Gobuster is a fantastic tool to help you reduce your application’s attack surface.
You can use the following steps to prevent and stop brute-force attacks on your web application.
Audit yourself: Use Gobuster on your own applications and perform an audit. This will help you find the information that will be visible to the attackers.
Apply security policies: To prevent resources like S3 from being exposed on the internet, use AWS bucket policies to prevent unauthorized access.
Use bot protection solutions: Bot protection services like Cloudflare will stop any brute-force attacks making it incredibly difficult to attack your web application.
-
 1:43
1:43
Dev Null - | Hacking| CyberSecurity| Cybersecurity education
2 years agoSelecting a Laptop for Ethical Hacking Success
2931 -
 2:05:03
2:05:03
Badlands Media
14 hours agoDevolution Power Hour Ep. 396: The Machine Cracks – CIA Networks, Color Revolutions & Trump’s Playbook
147K23 -
 2:08:24
2:08:24
Inverted World Live
10 hours agoAliens On The Campaign Trail | Ep. 120
110K26 -
 1:38:50
1:38:50
FreshandFit
11 hours agoHow Do Women WANT To Be Approached? w/ Dom Lucre & Prince
39.6K44 -
 2:58:08
2:58:08
TimcastIRL
9 hours agoTrump Announces Israel Hamas PEACE PLAN SIGNED Israel To WITHDRAW Troops | Timcast IRL
228K180 -
 3:33:15
3:33:15
Alex Zedra
7 hours agoLIVE! New Game!
49.7K6 -
 38:05
38:05
Man in America
15 hours agoEric Trump on Prosecuting TREASON, Civil War & the Battle of Good vs. Evil
56.5K33 -
 3:04:23
3:04:23
Barry Cunningham
8 hours agoBREAKING NEWS: PRESIDENT TRUMP BROKERS HISTORIC PEACE DEAL IN THE MIDDLE EAST! AND MORE NEWS!
77K46 -
 6:28:59
6:28:59
SpartakusLIVE
11 hours agoThe Boys are BACK || The Duke of NUKE and his Valiant Knights of the Tower of POWER
58.6K2 -
 1:15:32
1:15:32
Tucker Carlson
8 hours agoICE Protests and Antifa Riots: Tucker Carlson Warns of Total Destruction if America Doesn’t Act Fast
83.1K316
