Premium Only Content
Chapter-33, LEC-9 | Saving SubProcess | #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
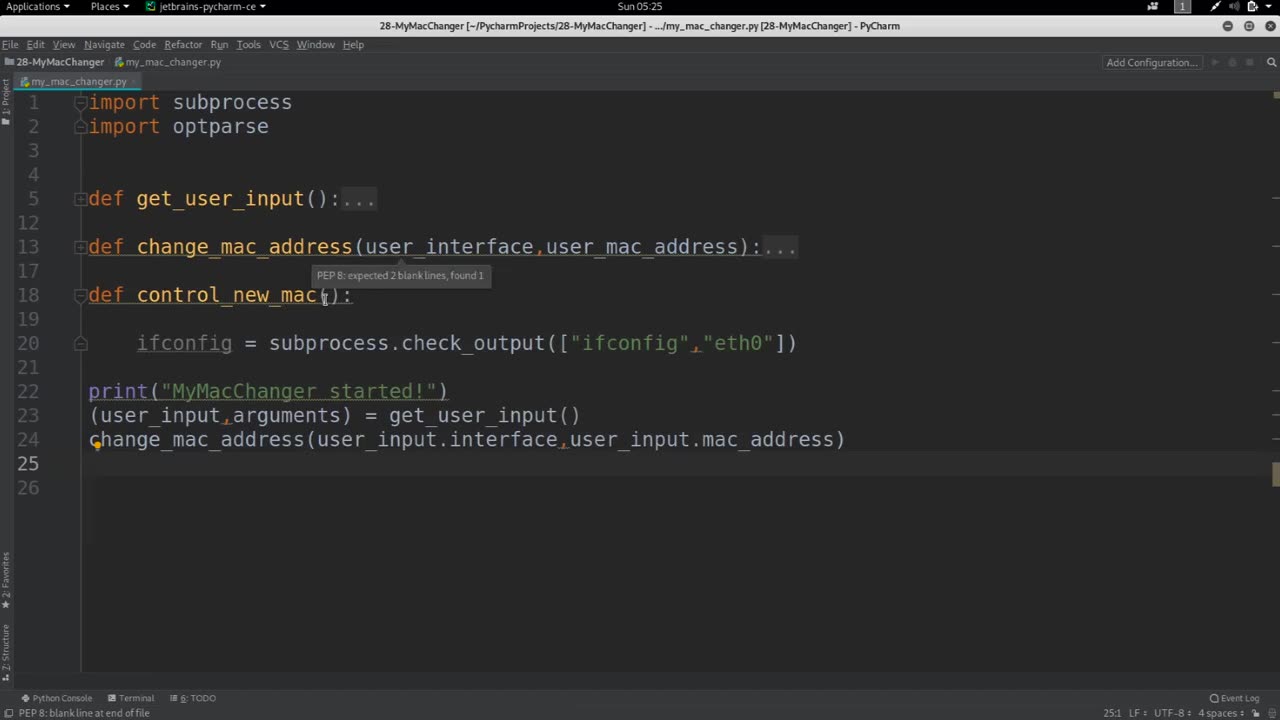
In Python, you can use the subprocess module to run external processes or commands from your Python code. When you run a subprocess, you may want to capture its output and save it to a file for later use.
Here's an example of how to save the output of a subprocess to a file:
python Copy code
import subprocess # Run the command and capture its output output = subprocess.check_output(['ls', '-l']) # Open a file for writing with open('output.txt', 'w') as f: # Write the output to the file f.write(output.decode())
In this example, we use the check_output() function from the subprocess module to run the ls -l command and capture its output as a bytes object. We then decode the bytes object to a string using the decode() method.
Next, we open a file named output.txt for writing using a with statement. The with statement ensures that the file is properly closed when we are done with it.
Finally, we write the output to the file using the write() method.
This code will save the output of the ls -l command to a file named output.txt. You can modify the code to save the output of any subprocess to a file by changing the command and the filename.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 3:30:07
3:30:07
Barry Cunningham
6 hours agoBREAKING NEWS: COUNTDOWN TO COMMUNISM! ELECTION RESULTS SHOW!
48.1K36 -
 2:11:28
2:11:28
DeVory Darkins
5 hours agoLIVE NOW: 2025 Election results and Exit Polls AMA
57.9K41 -
 DVR
DVR
DLDAfterDark
4 hours ago $0.03 earnedJust Another Tuesday - In Virginia - The Governor's Race & Glock Talk
21.6K1 -
 3:21:38
3:21:38
The Charlie Kirk Show
7 hours agoJUDGMENT DAY 2025: The Election Results Stream
186K77 -
 3:51:07
3:51:07
MattMorseTV
8 hours ago $0.77 earned🔴Election Day LIVE COVERAGE.🔴
91.2K47 -
 1:16:51
1:16:51
Flyover Conservatives
1 day agoSHOCKING DATA REVEALS: Young Voters Are Done With the Old GOP - Mark Mitchell, Rasmussen Reports | FOC Show
32.7K16 -
 1:15:28
1:15:28
Sarah Westall
7 hours agoGrooming is Protected and Encouraged by the System – Michelle Peterson and Mike Adamovich
32K10 -
 4:00:13
4:00:13
Akademiks
5 hours agoKendrick tries to Flip the Bots on DRAKE? WHo Beats Jay z in a verzuz. Blueface finally free!
36.5K7 -
 1:38:16
1:38:16
Professor Nez
10 hours ago🚨ELECTION NIGHT 2025 LIVE! Massive Upsets Brewing in New York, New Jersey & Virginia!
31.3K10 -
 4:48:50
4:48:50
Due Dissidence
13 hours agoLIVE: ELECTION RESULTS From NYC, NJ, and VA - Trump Approval CRATERS, Kash's Private Jet CRASH OUT
50.4K22