Premium Only Content
Chapter-33, LEC-6 | Introducing Variables. | #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
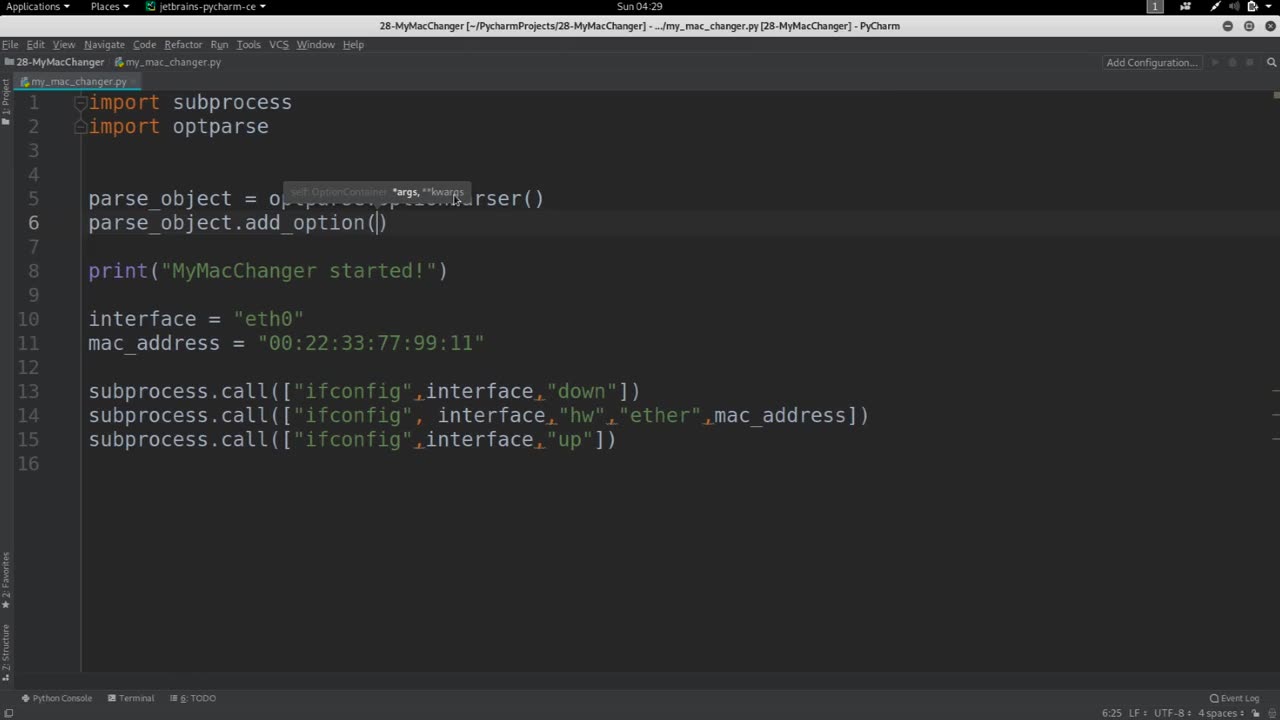
In the context of MAC changer, introducing variables means creating placeholders for values that will be used in the program. These variables can store different types of data such as numbers, strings, and Boolean values, and can be assigned values at runtime.
For example, in a MAC changer program, you could create variables to store the current MAC address of the network interface, the new MAC address that you want to set, and a boolean flag to indicate whether the operation was successful or not.
By using variables, you can make your code more flexible and reusable, as you can change the values of these variables based on different inputs or conditions. This can be useful in situations where you want to automate the process of changing MAC addresses on multiple network interfaces, or if you want to perform the operation repeatedly with different MAC addresses.
Overall, introducing variables in a MAC changer program allows you to manipulate MAC addresses more efficiently and with greater control over the program's behavior.
-
 3:21:38
3:21:38
The Charlie Kirk Show
6 hours agoJUDGMENT DAY 2025: The Election Results Stream
175K75 -
 3:51:07
3:51:07
MattMorseTV
7 hours ago $0.77 earned🔴Election Day LIVE COVERAGE.🔴
85.6K47 -
 1:16:51
1:16:51
Flyover Conservatives
1 day agoSHOCKING DATA REVEALS: Young Voters Are Done With the Old GOP - Mark Mitchell, Rasmussen Reports | FOC Show
32.7K16 -
 1:15:28
1:15:28
Sarah Westall
7 hours agoGrooming is Protected and Encouraged by the System – Michelle Peterson and Mike Adamovich
29.2K10 -
 4:00:13
4:00:13
Akademiks
4 hours agoKendrick tries to Flip the Bots on DRAKE? WHo Beats Jay z in a verzuz. Blueface finally free!
33.5K7 -
 1:38:16
1:38:16
Professor Nez
10 hours ago🚨ELECTION NIGHT 2025 LIVE! Massive Upsets Brewing in New York, New Jersey & Virginia!
30K10 -
 4:48:50
4:48:50
Due Dissidence
13 hours agoLIVE: ELECTION RESULTS From NYC, NJ, and VA - Trump Approval CRATERS, Kash's Private Jet CRASH OUT
49.4K21 -
 12:50
12:50
Demons Row
6 hours ago $0.05 earnedBikers of New Jersey 💀🏍️ Pagans, Thunder Guards, and Thug Riders
24.1K6 -
 42:31
42:31
Stephen Gardner
9 hours ago🔥Old Obama Video RESURFACES - His Own Words CONDEMNED Him! Trump Gains MASSIVE Momentum!!
31.5K32 -
 13:09:35
13:09:35
LFA TV
1 day agoLIVE & BREAKING NEWS! | TUESDAY 11/4/25
175K38