Premium Only Content
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
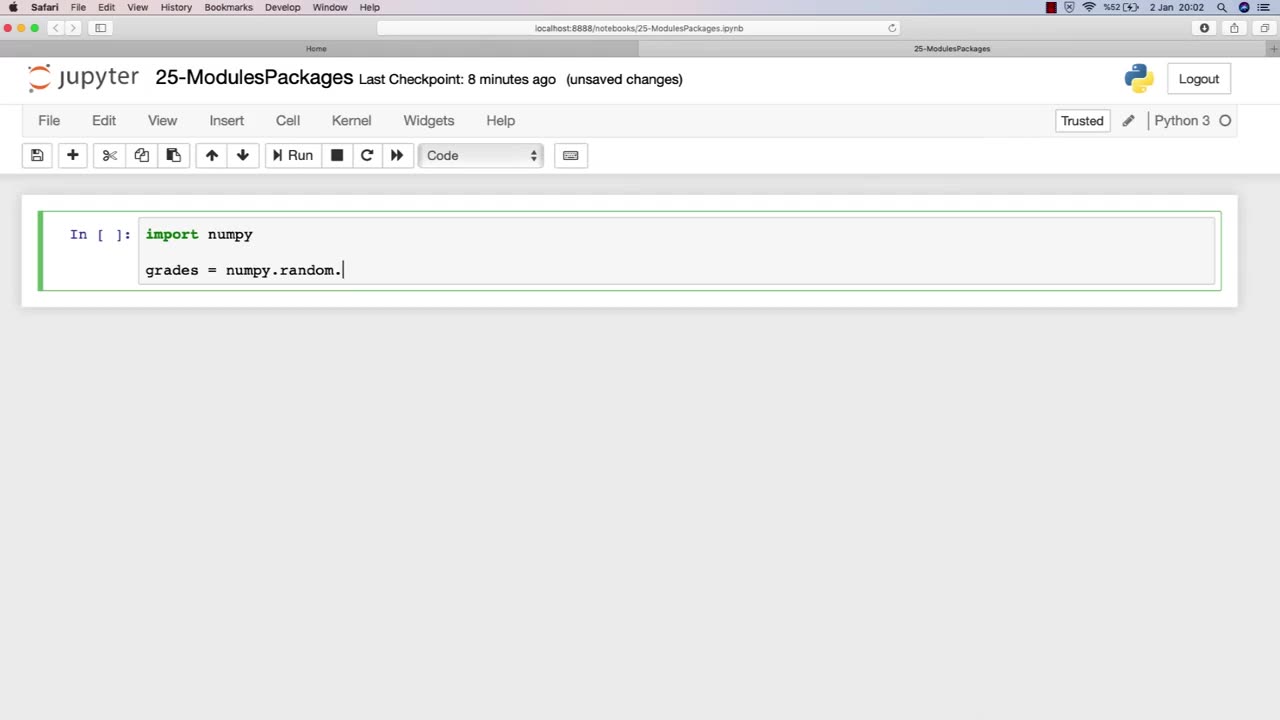
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 1:00:32
1:00:32
Man in America
11 hours ago🔴 LIVE: Terror Attacks or False Flags? IT DOESN'T ADD UP!!!
59K20 -
 1:02:38
1:02:38
Donald Trump Jr.
13 hours agoNew Year’s Terror, Latest Breaking News with Sebastian Gorka | TRIGGERED Ep.204
194K398 -
 59:59
59:59
The StoneZONE with Roger Stone
8 hours agoAfter Years of Targeting Trump, FBI and DOJ are Unprepared to Stop Terror Attacks | The StoneZONE
60.7K19 -
 1:26:42
1:26:42
Leonardaisfunny
6 hours ago $4.26 earnedH-1b Visas: Infinity Indians
39.1K18 -
 1:08:33
1:08:33
Josh Pate's College Football Show
11 hours ago $2.57 earnedPlayoff Reaction Special: Ohio State Owns Oregon | Texas Survives | UGA vs Notre Dame Takeaways
36.5K6 -
 58:04
58:04
Kimberly Guilfoyle
11 hours agoFBI's Terror Response Failures, Live with Steve Friend & Kyle Seraphin | Ep. 185
110K43 -
 2:15:01
2:15:01
WeAreChange
12 hours agoMassive Developments In Vegas Investigation! UNREAL DETONATION, Shocking Details Emerge!
115K62 -
 54:02
54:02
LFA TV
18 hours ago2025 Is Off to a Violent Start | TRUMPET DAILY 1.2.25 7pm
50.3K9 -
 59:27
59:27
theDaily302
17 hours agoThe Daily 302- JJ Carrell
43.1K5 -
 2:57
2:57
EvenOut
2 days ago $1.90 earnedTHE TELEPORTING PORTA POTTY TWIN RPANK!
40.4K3