Premium Only Content
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
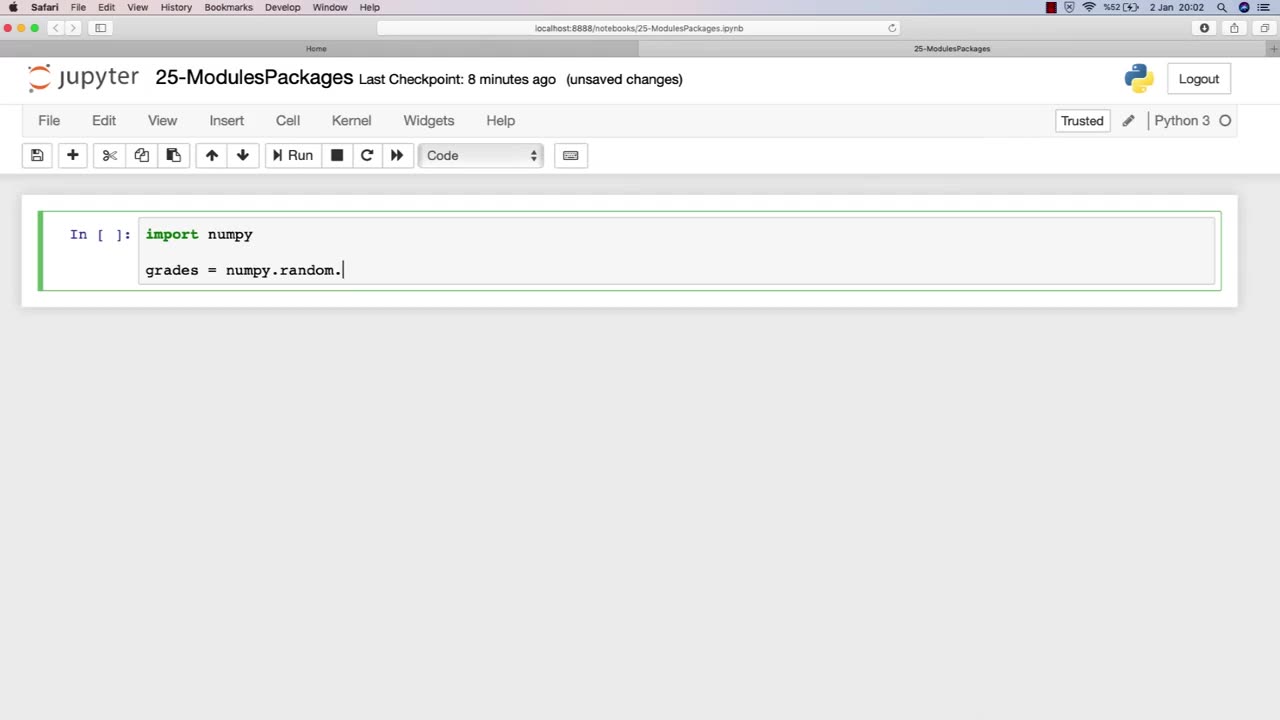
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 21:38
21:38
Professor Nez
21 hours agoTrump JUST BROKE the INTERNET with SAVAGE Line on Ilhan Omar!
42.3K58 -
 1:17:52
1:17:52
Dialogue works
3 days ago $10.17 earnedMartin Armstrong: This Is How World War III Starts… And It Already Has
36.4K18 -
 38:16
38:16
daniellesmithab
3 days agoAlberta Update: Getting Kids Back to the Classroom
28.4K11 -
 20:48
20:48
BlaireWhite
5 days agoTrans TikTokers Are Crashing Out (Over Nothing)
32.6K11 -
 2:07:06
2:07:06
Side Scrollers Podcast
22 hours agoHasan Piker CAUGHT LYING AGAIN + Twitch URGES LEFTIST IDEOLOGY + More | Side Scrollers
74.8K11 -
 8:40
8:40
MattMorseTV
18 hours ago $14.34 earnedSchumer just KICKED OFF the Left-Wing CIVIL WAR.
35.8K34 -
 21:39
21:39
Nikko Ortiz
2 days agoI Take A North Korean Shooting
33.5K6 -
 1:46:26
1:46:26
The Michelle Moore Show
21 hours ago'The Religion Invasion In the U.S. and the Deep State Agenda' Guest, Mark Taylor: The Michelle Moore Show (Nov 3, 2025)
41.9K42 -
 LIVE
LIVE
TruthStream with Joe and Scott
5 days agoSovereign Codes & Cosmic Infrastructure,Ufo's, UAP's, Monads, Matrix Satellites, Interstellar Visitors, SYRONA #505
302 watching -
 LIVE
LIVE
Lofi Girl
2 years agoSynthwave Radio 🌌 - beats to chill/game to
149 watching