Premium Only Content
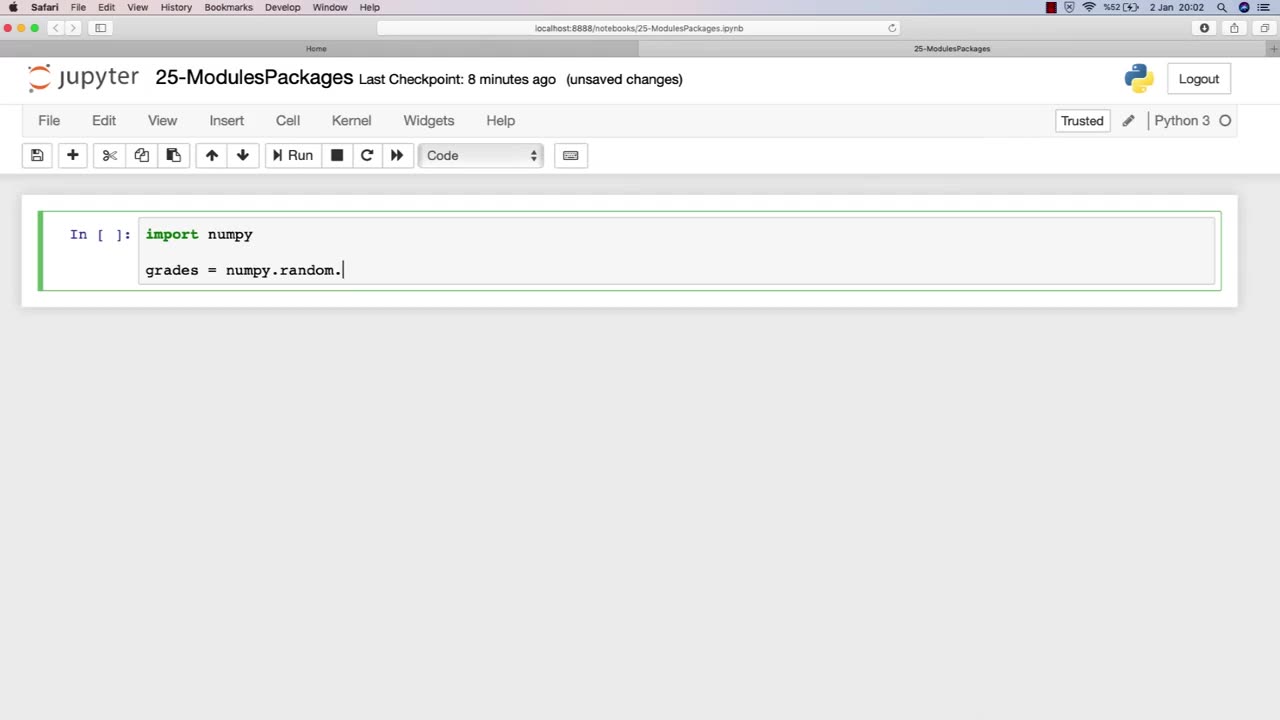
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 LIVE
LIVE
MattMorseTV
2 hours ago $10.95 earned🔴Trump's '60 Minutes' INTERVIEW + MUCH MORE.🔴
1,330 watching -
 LIVE
LIVE
Dr Disrespect
10 hours ago🔴LIVE - DR DISRESPECT - ARC RAIDERS - FULL SEND INTO THE RED
1,123 watching -
 1:02:08
1:02:08
BonginoReport
4 hours agoNicki Minaj Speaks Out Against Christian Persecution - Nightly Scroll w/ Hayley Caronia (Ep.169)
37.7K23 -
 LIVE
LIVE
SpartakusLIVE
4 hours agoSNIPING in Battlefield 6 - REDSEC || Monday MOTIVATION to CONQUER the Week
148 watching -
 LIVE
LIVE
Nerdrotic
2 hours ago $2.05 earnedNerdrotic At Night 531
285 watching -
 LIVE
LIVE
The Jimmy Dore Show
3 hours agoTrump Threatens to INVADE Nigeria! Kash Patel CRASHES OUT Over Jet Use Criticism!
7,490 watching -
 LIVE
LIVE
Conductor_Jackson
22 hours agoLet's Play Unrailed 2 Solo! 🚂🚂🚂🚂🚂🚂
13 watching -
 1:25:38
1:25:38
Kim Iversen
4 hours agoTrump’s Nigeria Threat Isn’t About Christians — It’s About China
81.7K84 -
 6:15:23
6:15:23
VikingNilsen
7 hours ago🔴LIVE - ARC RAIDERS - QUEST GRINDING
2.45K -
 59:10
59:10
Sean Unpaved
3 hours agoDodgers Dynasty Rolls On, NFL Chaos Reigns, & MNF Showdown Countdown
16.8K1