Premium Only Content
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
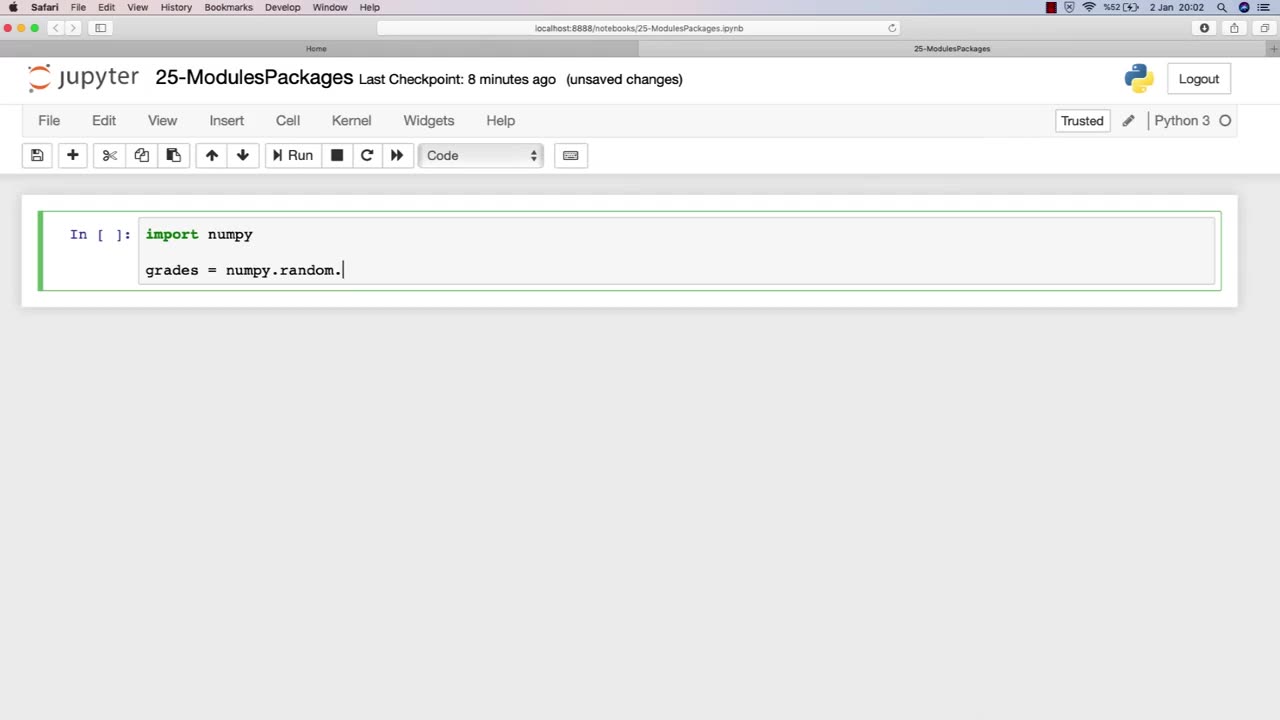
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 19:12
19:12
Robbi On The Record
10 hours ago $16.92 earnedThe Loneliness Epidemic: AN INVESTIGATION
41.3K74 -
 14:45
14:45
Mrgunsngear
1 day ago $98.73 earnedFletcher Rifle Works Texas Flood 30 Caliber 3D Printed Titanium Suppressor Test & Review
81.6K20 -
 17:17
17:17
Lady Decade
1 day ago $6.12 earnedMortal Kombat Legacy Kollection is Causing Outrage
47K8 -
 35:51
35:51
Athlete & Artist Show
1 day ago $11.13 earnedIs Ryan Smith The Best Owner In The NHL?
65.3K4 -
 22:56
22:56
American Thought Leaders
2 days agoCharles Murray: I Thought Religion Was Irrelevant to Me. I Was Wrong.
57.6K29 -
 36:22
36:22
Brad Owen Poker
11 hours agoGIGANTIC $17,000+ Pot In BOBBY’S ROOM! TRAPPING Top Pro w/FULL HOUSE!! Big Win! Poker Vlog Ep 326
66K3 -
 3:53
3:53
GreenMan Studio
1 day agoRUMBLE RUNDOWN: DREAM HACK SPECIAL W/Greenman Reports
54.8K10 -
 1:28
1:28
Damon Imani
2 days agoThey Laughed at Trump’s Cognitive Test — Damon Made Them REGRET It!
54.2K35 -
 9:14
9:14
Freedom Frontline
1 day agoAdam Schiff PANICS As Eric Schmitt Exposes His Dirty Lies LIVE
36.2K80 -
 10:32
10:32
GBGunsRumble
1 day agoGBGuns Armory Ep 153 Adler Arms AD-9`
24.2K2