Premium Only Content
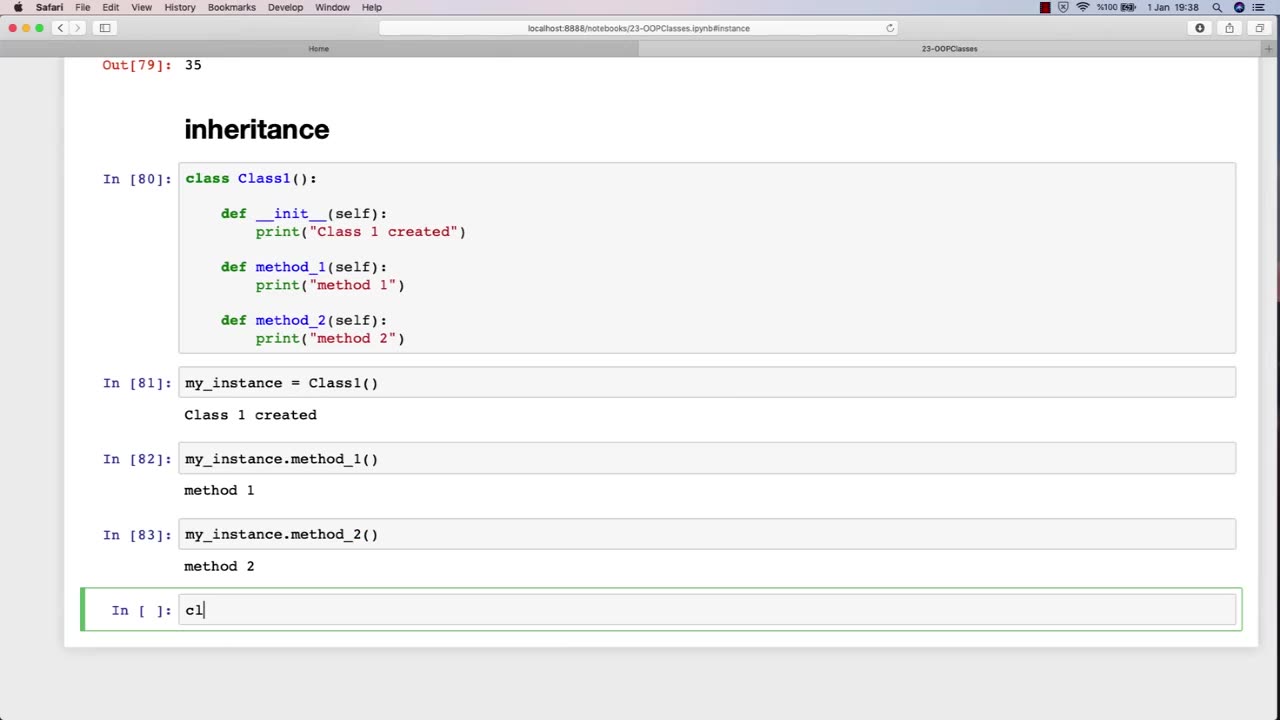
Chapter-31, LEC-5 | Inheritance | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
Inheritance is an important concept in object-oriented programming, and it can also be relevant to an ethical hacking course. In the context of ethical hacking, inheritance can refer to the use of pre-existing code or tools to aid in the hacking process.
For example, ethical hackers may inherit code or tools from previous projects, open-source software, or online resources. This code or tools may help them automate tasks, test for vulnerabilities, or exploit known weaknesses. By inheriting code or tools, ethical hackers can save time and effort, while also benefiting from the knowledge and expertise of other developers.
However, it is important for ethical hackers to be aware of the potential risks and limitations of inheriting code or tools. Inherited code may contain bugs or vulnerabilities that could introduce new security risks, and inherited tools may not be well-suited to the specific context of the hacking project. Therefore, ethical hackers must exercise caution when using inherited code or tools, and should always verify their functionality and security before incorporating them into their own work.
Furthermore, ethical hackers must also consider the ethical implications of inheriting code or tools. They must ensure that the code or tools they use are legally obtained and do not infringe on intellectual property rights or other legal obligations. They must also be mindful of the potential impact of their actions, and ensure that they are using their skills and tools for ethical purposes.
In summary, inheritance is an important concept in ethical hacking, as it allows hackers to leverage pre-existing code or tools to aid in their work. However, ethical hackers must be aware of the potential risks and limitations of inherited code or tools, and must also consider the ethical implications of their actions.
-
 LIVE
LIVE
SpartakusLIVE
2 hours agoNEW Update - BROKEN Attachment || Viewers REJOICE at the long-awaited Return of Their KING
368 watching -
 6:02
6:02
Blackstone Griddles
2 hours agoPrime Rib Brisket Burgers on the Blackstone Griddle
140 -
 1:14:07
1:14:07
Glenn Greenwald
7 hours agoGlenn Takes Your Questions: Billionaires, Bari Weiss and Journalism | SYSTEM UPDATE #509
53.4K24 -
 LIVE
LIVE
StevieTLIVE
1 hour agoFriday Night HYPE Warzone Games with Stevie
84 watching -
 LIVE
LIVE
SavageJayGatsby
22 hours agoLet's Play: Sea of Thieves | Friend Friday
118 watching -
 LIVE
LIVE
GritsGG
2 hours agoTop 250 Ranked Grind! Dubulars!🫡
54 watching -
 19:51
19:51
Robbi On The Record
23 hours agoElectronic Tattoos Measuring Thoughts? From iPhone to iSkin
22.3K15 -
 8:12
8:12
Hollywood Exposed
1 day agoJoy Behar Tried To Shame Tulsi Gabbard And Instantly FAILED
2.94K3 -
 17:03
17:03
IsaacButterfield
16 hours ago $1.80 earnedBritish Man ARRESTED for Saying ‘I Love Bacon’ to a Muslim!!
3.52K6 -
 LIVE
LIVE
The Sufari Hub
2 hours ago🔴SUFARI & JAMES TAKE ON THE UNDEAD - DYING LIGHT THEN THE FOLLOWING
6 watching