Premium Only Content
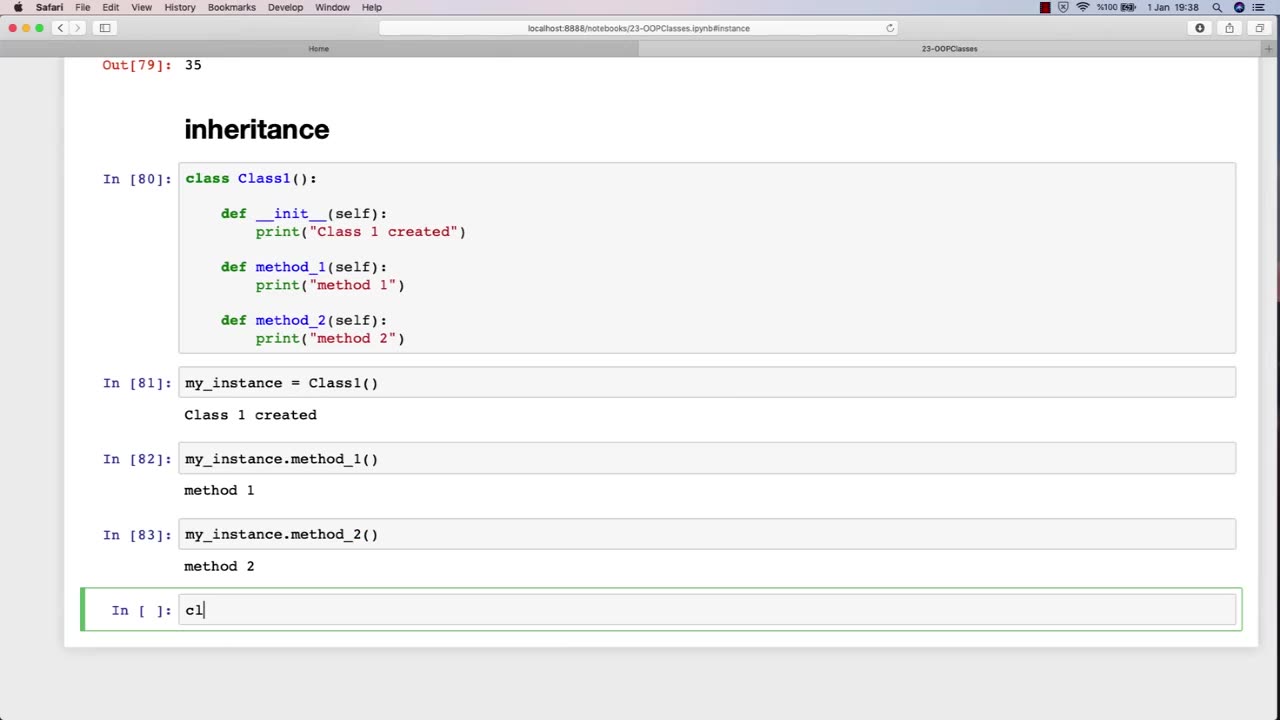
Chapter-31, LEC-5 | Inheritance | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
Inheritance is an important concept in object-oriented programming, and it can also be relevant to an ethical hacking course. In the context of ethical hacking, inheritance can refer to the use of pre-existing code or tools to aid in the hacking process.
For example, ethical hackers may inherit code or tools from previous projects, open-source software, or online resources. This code or tools may help them automate tasks, test for vulnerabilities, or exploit known weaknesses. By inheriting code or tools, ethical hackers can save time and effort, while also benefiting from the knowledge and expertise of other developers.
However, it is important for ethical hackers to be aware of the potential risks and limitations of inheriting code or tools. Inherited code may contain bugs or vulnerabilities that could introduce new security risks, and inherited tools may not be well-suited to the specific context of the hacking project. Therefore, ethical hackers must exercise caution when using inherited code or tools, and should always verify their functionality and security before incorporating them into their own work.
Furthermore, ethical hackers must also consider the ethical implications of inheriting code or tools. They must ensure that the code or tools they use are legally obtained and do not infringe on intellectual property rights or other legal obligations. They must also be mindful of the potential impact of their actions, and ensure that they are using their skills and tools for ethical purposes.
In summary, inheritance is an important concept in ethical hacking, as it allows hackers to leverage pre-existing code or tools to aid in their work. However, ethical hackers must be aware of the potential risks and limitations of inherited code or tools, and must also consider the ethical implications of their actions.
-
 LIVE
LIVE
Pop Culture Crisis
2 hours agoCoca-Cola's WAR ON CHRISTMAS, Movie Press Tour CRINGE, Gen Z HATES Gen Z | Ep, 949
513 watching -
 16:30
16:30
Clintonjaws
17 hours ago $4.31 earned'The View's' Producer Stops Show & Forces Whoopie To Correct Lie
5.43K6 -
 1:10:24
1:10:24
Steve-O's Wild Ride! Podcast
5 days ago $0.38 earnedMatt McCusker Makes Steve-O Nervous | Wild Ride #272
2.84K1 -
 17:09
17:09
Bearing
9 hours agoHasan Goes NUCLEAR On Chat ☢️ ROASTED By JD Vance Over Dog Allegations 🚨
18.8K28 -
 LIVE
LIVE
The HotSeat With Todd Spears
1 hour agoEP 203: The Military "Whistleblower"
777 watching -
![[Ep 784] Election 2025: NYC is Screwed | Tatum Calls Out Kirk Conspiracists | Guest: Sam Anthony](https://1a-1791.com/video/fwe2/00/s8/1/U/Q/E/w/UQEwz.0kob-small-Ep-784-Election-2025-NYC-is.jpg) LIVE
LIVE
The Nunn Report - w/ Dan Nunn
1 hour ago[Ep 784] Election 2025: NYC is Screwed | Tatum Calls Out Kirk Conspiracists | Guest: Sam Anthony
156 watching -
 1:22:54
1:22:54
DeVory Darkins
4 hours agoTrump makes shocking announcement as Major ELECTION UPDATE drops after bomb threat
91.8K53 -
 10:11
10:11
Dr. Nick Zyrowski
8 days agoDoes Creatine CAUSE Hair Loss? (We All Got This Wrong)
6.85K2 -
 1:09:24
1:09:24
Timcast
4 hours agoZohran Mamdani BLAMES Trump Over Bomb Threats At Polling Locations
169K106 -
 3:09:52
3:09:52
Right Side Broadcasting Network
6 hours agoLIVE REPLAY: White House Press Secretary Karoline Leavitt Holds a Press Briefing - 11/4/25
69.8K16