Premium Only Content
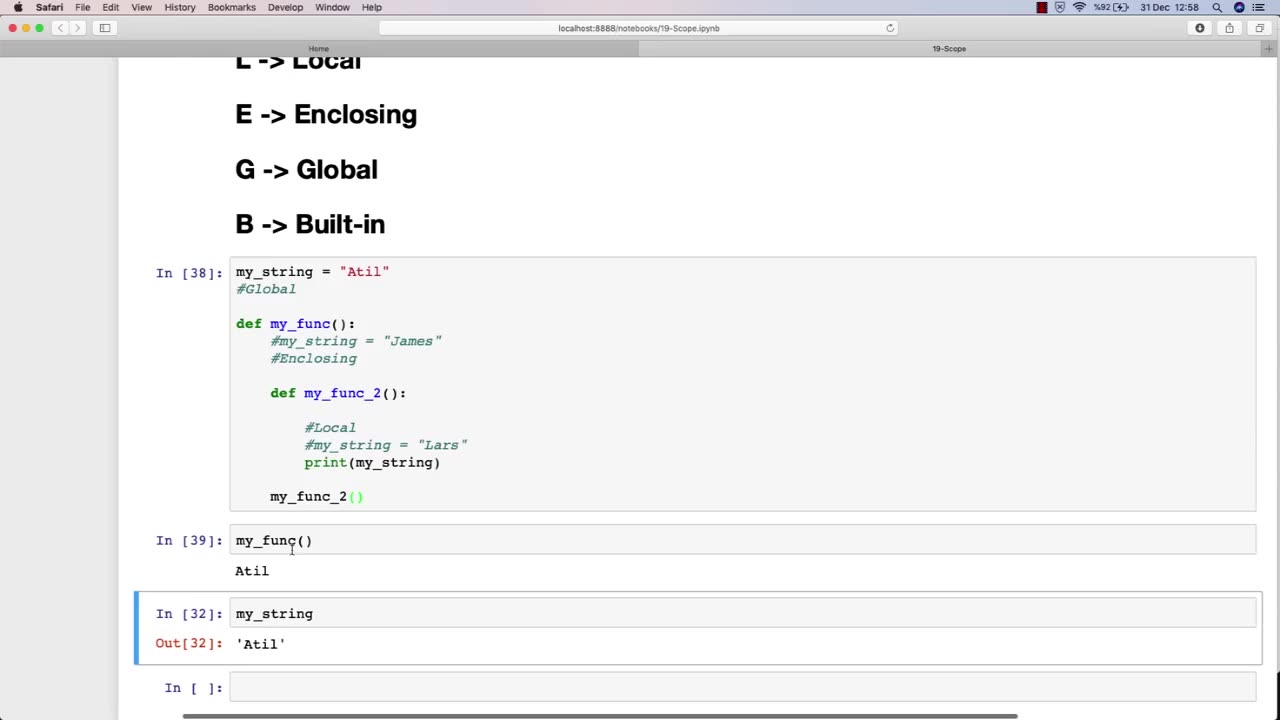
Chapter-30, LEC-6 | SCOPE | #ethicalhacking #education #hacking #rumble
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
The scope of an ethical hacking course is vast and covers a wide range of topics related to cybersecurity and information security. At a high level, the scope of an ethical hacking course typically includes:
Understanding the fundamentals of cybersecurity: This includes understanding the various types of cybersecurity threats, such as viruses, malware, and phishing attacks, and the principles of risk management and threat modeling.
Network security: This includes understanding the fundamentals of network architecture and protocols, as well as how to secure networks against attacks such as denial-of-service (DoS) attacks and man-in-the-middle (MITM) attacks.
Web application security: This includes understanding the principles of web application architecture and how to secure web applications against common attacks such as cross-site scripting (XSS) and SQL injection.
Wireless security: This includes understanding the fundamentals of wireless networks and how to secure them against attacks such as rogue access points and eavesdropping.
Penetration testing: This includes understanding the principles of penetration testing and how to conduct effective ethical hacking activities, including reconnaissance, vulnerability assessment, and exploitation.
Ethical and legal considerations: This includes understanding the ethical and legal considerations associated with ethical hacking, such as obtaining permission and respecting privacy.
The scope of an ethical hacking course is constantly evolving to keep pace with the ever-changing cybersecurity landscape. As new threats emerge and new technologies are developed, the scope of an ethical hacking course must adapt to provide students with the latest knowledge and techniques in the field of cybersecurity.
-
 LIVE
LIVE
RealAmericasVoice
3 days agoHOME OF REAL NEWS
12,952 watching -
 54:06
54:06
Ben Shapiro
1 hour agoEp. 2278 - UNTHINKABLE: Charlie Kirk, 31, Assassinated
79921 -
 DVR
DVR
Robert Gouveia
3 hours agoCharlie Kirk Latest News; FBI Briefing; Shooter Photo Captured; 9/11 Honors
18.2K7 -
 48:51
48:51
Liz Wheeler
1 hour agoFor Charlie Kirk
3.28K5 -
 2:52:05
2:52:05
Steven Crowder
5 hours agoFOR CHARLIE KIRK: Breaking Exclusive On Assassin
1.28M1.88K -
 1:19:03
1:19:03
Timcast
3 hours ago🚨CONFIRMED: Charlie Kirk Killer Was Trans Antifa Leftist | Tim Pool
240K475 -
 2:28:45
2:28:45
Benny Johnson
5 hours agoAmerican Martyr: Remembering Charlie Kirk | FBI Reveals New Footage of Assassin, Trump's Eulogy LIVE
217K228 -
 25:38
25:38
The Rubin Report
4 hours agoRemembering Charlie Kirk & 9/11
251K58 -
 1:00:32
1:00:32
VINCE
6 hours agoRest In Peace Charlie Kirk | Episode 123 - 09/11/25
424K377 -
 LIVE
LIVE
LFA TV
9 hours agoLFA TV ALL DAY STREAM - THURSDAY 9/11/25
3,379 watching