Premium Only Content
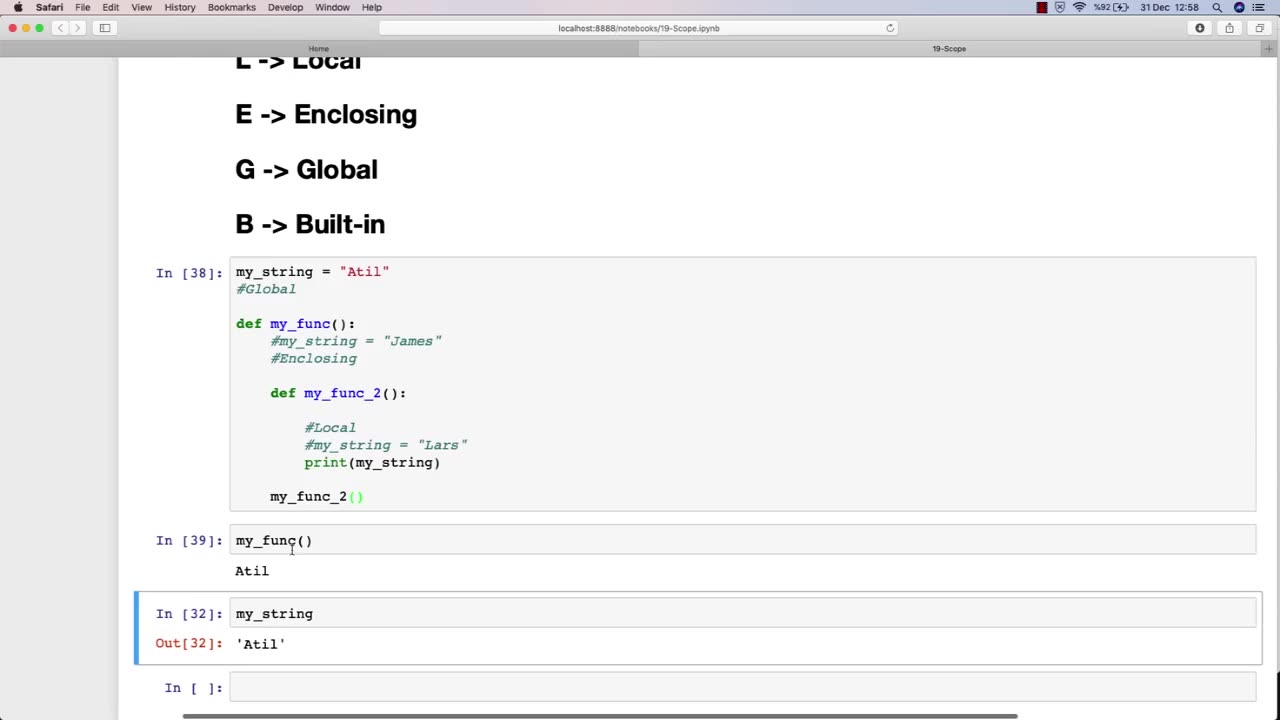
Chapter-30, LEC-6 | SCOPE | #ethicalhacking #education #hacking #rumble
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
The scope of an ethical hacking course is vast and covers a wide range of topics related to cybersecurity and information security. At a high level, the scope of an ethical hacking course typically includes:
Understanding the fundamentals of cybersecurity: This includes understanding the various types of cybersecurity threats, such as viruses, malware, and phishing attacks, and the principles of risk management and threat modeling.
Network security: This includes understanding the fundamentals of network architecture and protocols, as well as how to secure networks against attacks such as denial-of-service (DoS) attacks and man-in-the-middle (MITM) attacks.
Web application security: This includes understanding the principles of web application architecture and how to secure web applications against common attacks such as cross-site scripting (XSS) and SQL injection.
Wireless security: This includes understanding the fundamentals of wireless networks and how to secure them against attacks such as rogue access points and eavesdropping.
Penetration testing: This includes understanding the principles of penetration testing and how to conduct effective ethical hacking activities, including reconnaissance, vulnerability assessment, and exploitation.
Ethical and legal considerations: This includes understanding the ethical and legal considerations associated with ethical hacking, such as obtaining permission and respecting privacy.
The scope of an ethical hacking course is constantly evolving to keep pace with the ever-changing cybersecurity landscape. As new threats emerge and new technologies are developed, the scope of an ethical hacking course must adapt to provide students with the latest knowledge and techniques in the field of cybersecurity.
-
 49:45
49:45
Liberty Hangout
1 day agoThe Left HATES America and Can't Change My Mind!
63.8K84 -
 23:42
23:42
The Kevin Trudeau Show Limitless
2 days agoThe Brotherhood’s Ancient Mirror Code Revealed
24.1K12 -
 10:18
10:18
Colion Noir
5 hours agoViral TikTok Proves Gun Owners Wrong?
31.3K35 -
![MAHA News [11.28] Team MAHA Dropping Bombs, Pesticide Fight, Campbell's Soup Outed, Save Ranchers](https://1a-1791.com/video/fwe2/11/s8/1/O/6/L/D/O6LDz.0kob-small-MAHA-News-11.28.jpg) DVR
DVR
Badlands Media
15 hours agoMAHA News [11.28] Team MAHA Dropping Bombs, Pesticide Fight, Campbell's Soup Outed, Save Ranchers
10.7K1 -
 1:01:18
1:01:18
DeVory Darkins
4 hours agoBREAKING: Trump issues fatal update to National Guard shooting
114K80 -
 49:57
49:57
The Quartering
4 hours agoTrump UNLOADS, Walmart Black Friday Madness & Trans Taco Bell Attack
24.6K35 -
 39:51
39:51
Tucker Carlson
4 hours agoGeorge Galloway Speaks Out on Being Forced Into Exile After Criticizing Ukraine War
39.7K106 -
 21:23
21:23
Neil McCoy-Ward
3 hours ago🔥 While You're Working Hard... They're Planning To Take EVERYTHING From You!!!
12.1K11 -
 2:13:37
2:13:37
Side Scrollers Podcast
6 hours agoTwitch CONTROVERSY Hit New Low + Reddit Mods QUIT + FireMAN is Now Sexist + More | Side Scrollers
72.8K7 -
 5:31
5:31
John Rich Official
13 days agoThe Righteous Hunter by John Rich
29.2K15