Premium Only Content
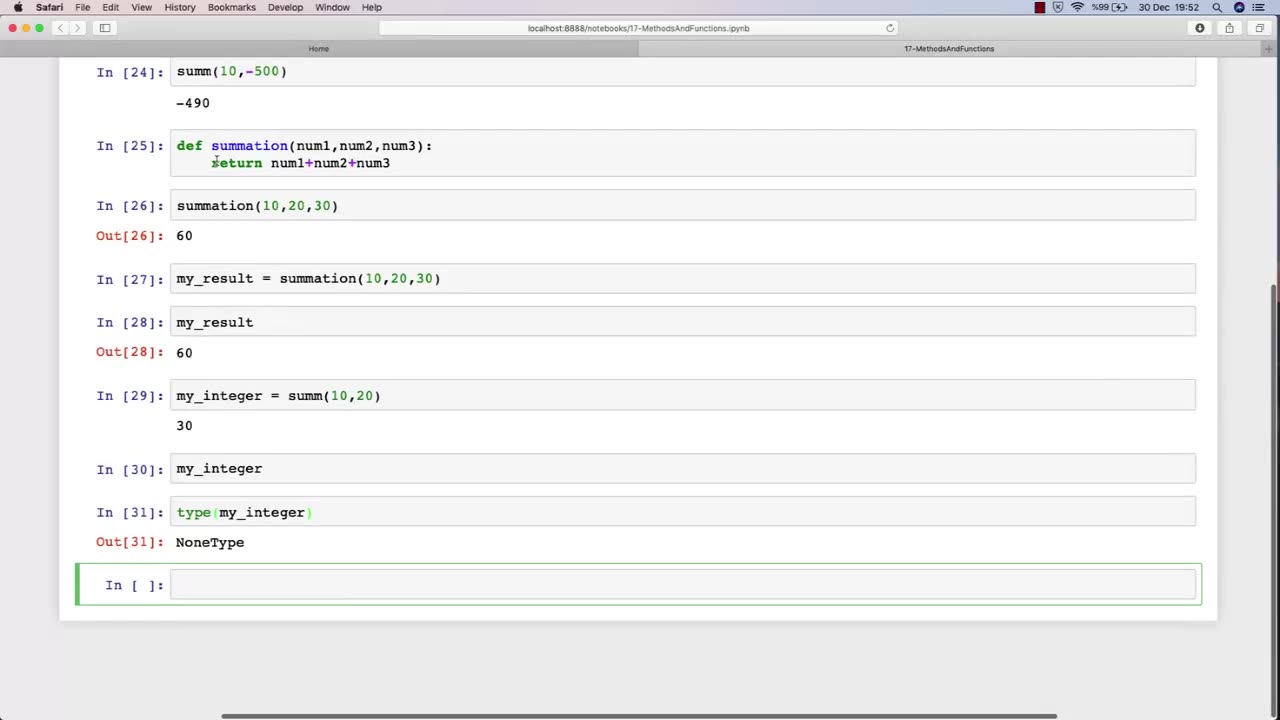
Chapter-30, LEC-3 | Functions Explained (lec-2) | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
In Lecture 2 of an ethical hacking course, the function is to introduce students to the basic principles and concepts of ethical hacking. This lecture typically covers topics such as the difference between ethical hacking and illegal hacking, the various types of hackers, and the ethical and legal issues associated with ethical hacking.
The main objective of this lecture is to establish a foundational understanding of what ethical hacking is, why it is important, and the ethical and legal considerations that must be taken into account when conducting ethical hacking activities.
Students in this lecture learn about the various types of hackers, including black hat hackers, white hat hackers, and grey hat hackers. They learn about the motivations and characteristics of each type of hacker and how they differ in terms of their intentions and activities.
The lecture also covers the ethical considerations associated with ethical hacking, such as the importance of obtaining permission before conducting any testing, respecting the privacy of individuals and organizations, and adhering to ethical and professional standards.
Finally, the lecture covers the legal issues associated with ethical hacking, including the various laws and regulations governing cybersecurity and data protection, and the potential consequences of violating these laws.
Overall, the function of Lecture 2 in an ethical hacking course is to provide students with a broad understanding of the ethical and legal principles that underpin ethical hacking, and to ensure that they are equipped with the knowledge and skills necessary to conduct ethical hacking activities in a responsible and professional manner.
-
 1:54:34
1:54:34
FreshandFit
8 hours agoBrandon Carter Returns
19.6K3 -
 LIVE
LIVE
MissesMaam
9 hours agoResident Evil 4 *FIRST EVER PLAYTHROUGH*💚✨
292 watching -
 LIVE
LIVE
SlingerGames
1 hour agoSlinger Slays Elden Ring - Pt. 8 - Enduring the Pain
23 watching -
 LIVE
LIVE
VapinGamers
2 hours ago $0.07 earnedOff The Grid - Co-Stream with BSparksGaming! Come Join the Mayhem! - !rumbot !music
26 watching -
 1:36:53
1:36:53
Glenn Greenwald
5 hours agoTrump Tries to End War in Ukraine; U.S. is Dangerously Low on Weapons and Munitions Former Trump DoD Official Warns | SYSTEM UPDATE #502
77.6K33 -
 3:00:53
3:00:53
Barry Cunningham
5 hours agoPRESIDENT TRUMP HAS ENTERED THE END GAME AND DEMOCRATS ARE NOW IRRELEVANT!
47.2K39 -
Jorba4
3 hours ago🔴Live-Jorba4- The Finals
17.6K1 -
 2:27:06
2:27:06
Blabs Games
13 hours agoApex Legends With Josiah & Mozz
14.9K -
 1:01:56
1:01:56
BonginoReport
7 hours agoDems Scramble To Rebrand and it’s a BIG FAIL - Nightly Scroll w/ Hayley Caronia (Ep.114)
107K109 -
 LIVE
LIVE
Eternal_Spartan
21 hours agoEternal Spartan Plays Final Fantasy 7 Remake Pt. 5 | USMC Vet | Join the Best Chat on Rumble!
72 watching