Premium Only Content
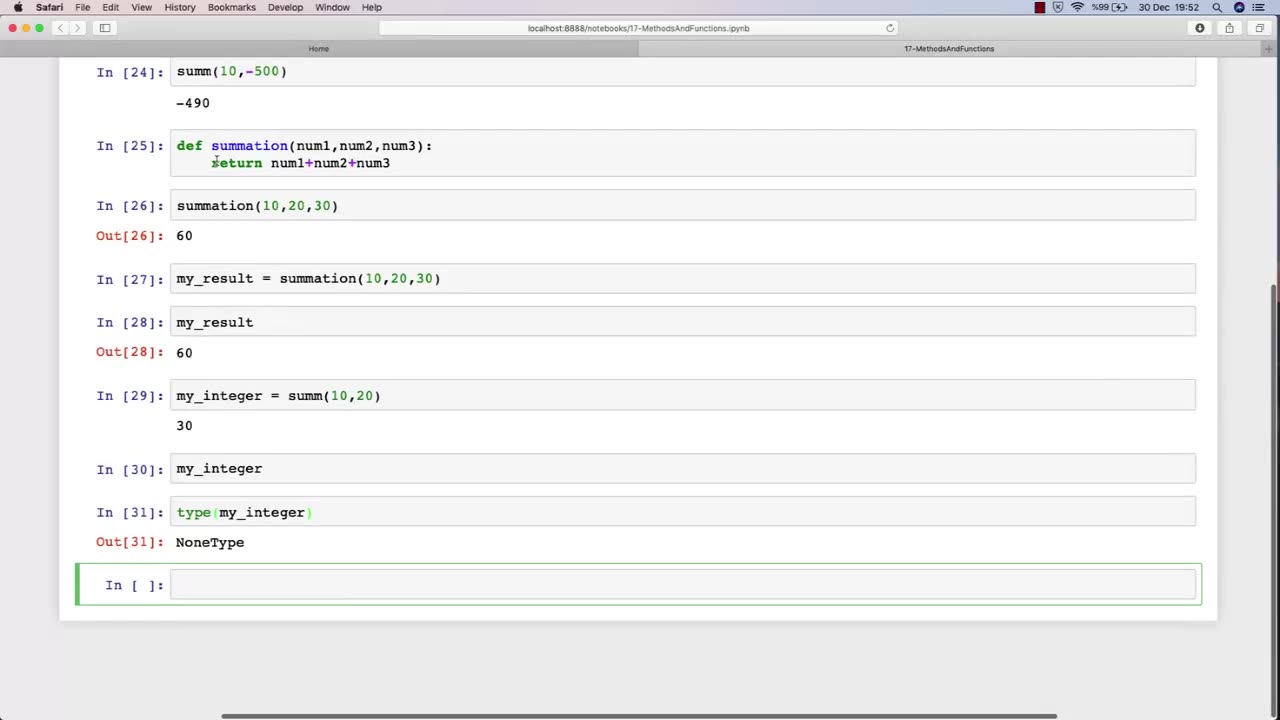
Chapter-30, LEC-3 | Functions Explained (lec-2) | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
In Lecture 2 of an ethical hacking course, the function is to introduce students to the basic principles and concepts of ethical hacking. This lecture typically covers topics such as the difference between ethical hacking and illegal hacking, the various types of hackers, and the ethical and legal issues associated with ethical hacking.
The main objective of this lecture is to establish a foundational understanding of what ethical hacking is, why it is important, and the ethical and legal considerations that must be taken into account when conducting ethical hacking activities.
Students in this lecture learn about the various types of hackers, including black hat hackers, white hat hackers, and grey hat hackers. They learn about the motivations and characteristics of each type of hacker and how they differ in terms of their intentions and activities.
The lecture also covers the ethical considerations associated with ethical hacking, such as the importance of obtaining permission before conducting any testing, respecting the privacy of individuals and organizations, and adhering to ethical and professional standards.
Finally, the lecture covers the legal issues associated with ethical hacking, including the various laws and regulations governing cybersecurity and data protection, and the potential consequences of violating these laws.
Overall, the function of Lecture 2 in an ethical hacking course is to provide students with a broad understanding of the ethical and legal principles that underpin ethical hacking, and to ensure that they are equipped with the knowledge and skills necessary to conduct ethical hacking activities in a responsible and professional manner.
-
 18:59
18:59
Nate The Lawyer
1 day ago $0.77 earnedDon Lemon Spreads Lie: Crossing Border Illegally Isn’t a Crime. FACT CHECK
51722 -
 2:04:30
2:04:30
Side Scrollers Podcast
18 hours agoGold’s Gym CONTROVERSY & BOYCOTT + Craig ADMITS DEFEAT + More | Side Scrollers
63.4K10 -
 1:26:06
1:26:06
MattMorseTV
17 hours ago $0.09 earned🔴Trump's Press Conference MASSIVE UPDATE.🔴
14.7K61 -
 21:39
21:39
Nikko Ortiz
3 days agoI Take A North Korean Shooting
48.8K8 -
 LIVE
LIVE
Lofi Girl
3 years agolofi hip hop radio 📚 - beats to relax/study to
194 watching -
 2:14:13
2:14:13
FreshandFit
15 hours agoShe Was Given Extravagant Gifts And STILL Friendzoned Him +EXPOSED
203K45 -
 1:16:07
1:16:07
Man in America
12 hours agoOperation Gladio: The CIA, Mossad & City of London’s Plan for a New World Order
35K34 -
 2:11:41
2:11:41
Badlands Media
14 hours agoDEFCON ZERQ Ep. 016: Shadow Governments, Ancient Tech & the Spiritual War for Humanity
87.6K66 -
 2:09:24
2:09:24
Inverted World Live
9 hours agoRats Have Learned to Hunt Bats | Ep. 135
40.1K17 -
 2:48:01
2:48:01
TimcastIRL
9 hours agoLIVE Election Coverage: Polling Stations SWATTED, Bomb Threats Called In | Timcast IRL
261K181