Premium Only Content
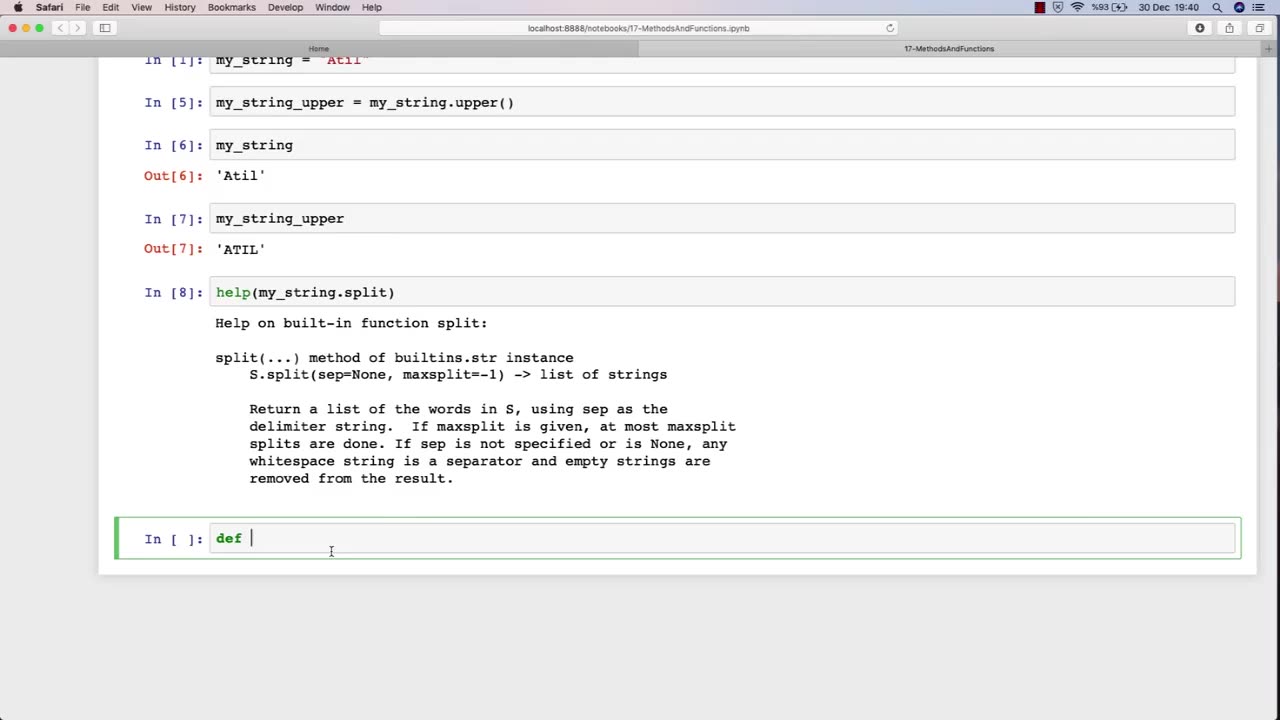
Chapter-30, LEC-2 | Functions Explained (lec-1) | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
The function of an ethical hacking course is to equip individuals with the knowledge, skills, and techniques necessary to become a professional ethical hacker. Ethical hacking is a critical component of cybersecurity, as it involves identifying and addressing potential vulnerabilities in computer systems, networks, and applications before malicious actors can exploit them.
An ethical hacking course typically covers a range of topics related to cybersecurity, including penetration testing, vulnerability assessment, network security, web application security, social engineering, cryptography, and incident response. The course provides students with an understanding of various security threats and how to mitigate them through the use of specialized tools and techniques.
During an ethical hacking course, students learn how to perform vulnerability assessments, conduct penetration testing, and analyze system and network logs to identify potential security threats. They also learn how to use various tools, such as vulnerability scanners and network analyzers, to assess the security posture of a system or network. Additionally, students learn about common attack vectors and techniques, such as SQL injection and cross-site scripting, and how to defend against them.
Overall, the goal of an ethical hacking course is to train individuals to become skilled and responsible cybersecurity professionals who can help organizations protect themselves from cyber attacks. By learning how to identify vulnerabilities and mitigate security threats, students can help ensure the security and privacy of sensitive information and safeguard against potential data breaches.
-
 LIVE
LIVE
Geeks + Gamers
3 hours agoTuesday Night's Main Event
514 watching -
 DVR
DVR
RiftTV
1 hour agoHow We Got 400 Leftists FIRED for MOCKING Charlie Kirk | The Rift | Guest: Olivia Krolczyk
2.87K6 -
 LIVE
LIVE
LFA TV
13 hours agoLFA TV ALL DAY STREAM - TUESDAY 9/16/25
832 watching -
 LIVE
LIVE
StevieTLIVE
1 hour agoWarzone Community Games to Start into Quads w/ The Fellas
94 watching -
 1:00:14
1:00:14
BonginoReport
3 hours agoSpeech Police Bondi Under Fire - Nightly Scroll w/ Hayley Caronia (Ep.135)
128K55 -
 LIVE
LIVE
Heart & Mind with Dr. Dina McMillan
7 hours ago"Heart & Mind with Dr. Dina McMillan: Episode 57 - Honoring Charlie Kirk - Where to from Here?"
40 watching -
 1:01:26
1:01:26
The Nick DiPaolo Show Channel
4 hours agoTrans Network Being Investigated | The Nick Di Paolo Show #1794
25.6K27 -
 22:53
22:53
The Rubin Report
2 hours agoMegyn Kelly Visibly Shocks Dave Rubin with Her Dark Prediction for What Happens Next
31K50 -
 LIVE
LIVE
Edge of Wonder
2 hours agoAlien Creature With Tentacles Growing on Meteorite Claims Panama Man
206 watching -
 1:04:35
1:04:35
TheCrucible
3 hours agoThe Extravaganza! EP: 37 (9/16/25)
135K30