Premium Only Content
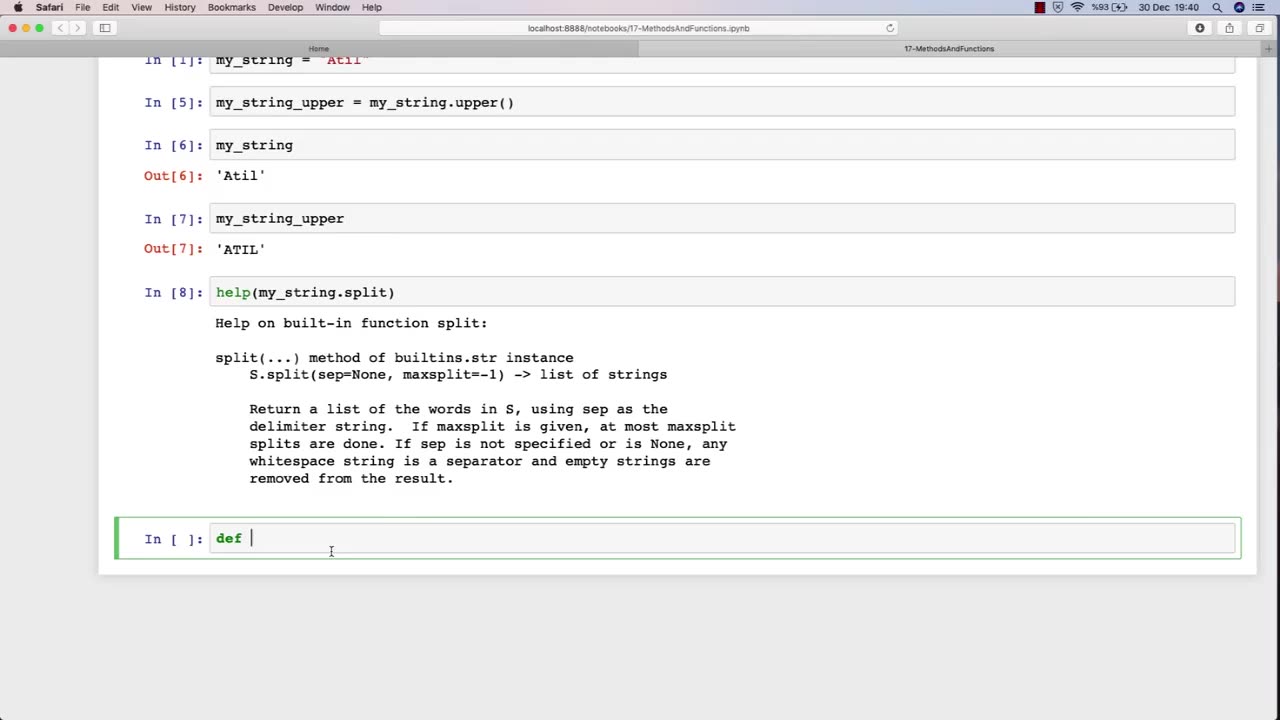
Chapter-30, LEC-2 | Functions Explained (lec-1) | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
The function of an ethical hacking course is to equip individuals with the knowledge, skills, and techniques necessary to become a professional ethical hacker. Ethical hacking is a critical component of cybersecurity, as it involves identifying and addressing potential vulnerabilities in computer systems, networks, and applications before malicious actors can exploit them.
An ethical hacking course typically covers a range of topics related to cybersecurity, including penetration testing, vulnerability assessment, network security, web application security, social engineering, cryptography, and incident response. The course provides students with an understanding of various security threats and how to mitigate them through the use of specialized tools and techniques.
During an ethical hacking course, students learn how to perform vulnerability assessments, conduct penetration testing, and analyze system and network logs to identify potential security threats. They also learn how to use various tools, such as vulnerability scanners and network analyzers, to assess the security posture of a system or network. Additionally, students learn about common attack vectors and techniques, such as SQL injection and cross-site scripting, and how to defend against them.
Overall, the goal of an ethical hacking course is to train individuals to become skilled and responsible cybersecurity professionals who can help organizations protect themselves from cyber attacks. By learning how to identify vulnerabilities and mitigate security threats, students can help ensure the security and privacy of sensitive information and safeguard against potential data breaches.
-
 2:47:28
2:47:28
Barry Cunningham
6 hours agoYOU'VE BEEN MISINFORMED! GREED IS ACTUALLY GOOD! ESPECIALLY NOW! (AND MORE NEWS)
30.5K18 -
 LIVE
LIVE
SpartakusLIVE
5 hours agoSNIPING in Battlefield 6 - REDSEC || Monday MOTIVATION to CONQUER the Week
218 watching -
 49:25
49:25
ThisIsDeLaCruz
2 hours ago $0.57 earnedBack Stage Pass with Avenged Sevenfold
5.6K5 -
 6:43:40
6:43:40
GritsGG
7 hours agoWorld Record Win Streak Attempt! #1 Most Wins 3880+!
208 -
 LIVE
LIVE
Tundra Tactical
4 hours ago $2.33 earnedProfessional Gun Nerd Plays Battlefield 6
274 watching -
 1:01:12
1:01:12
Donald Trump Jr.
7 hours agoThe China Matrix with Journalist Lee Smith | TRIGGERED Ep.288
117K80 -
 LIVE
LIVE
Dr Disrespect
12 hours ago🔴LIVE - DR DISRESPECT - ARC RAIDERS - FULL SEND INTO THE RED
1,183 watching -
 LIVE
LIVE
JdaDelete
3 hours agoFinally playing Eldin Ring | First Playthrough Episode 2
22 watching -
 1:02:08
1:02:08
BonginoReport
5 hours agoNicki Minaj Speaks Out Against Christian Persecution - Nightly Scroll w/ Hayley Caronia (Ep.169)
51.8K38 -
 LIVE
LIVE
HomieQuest
5 hours agoLive Streaming! Pokemon Legends Z-A
9 watching