Premium Only Content
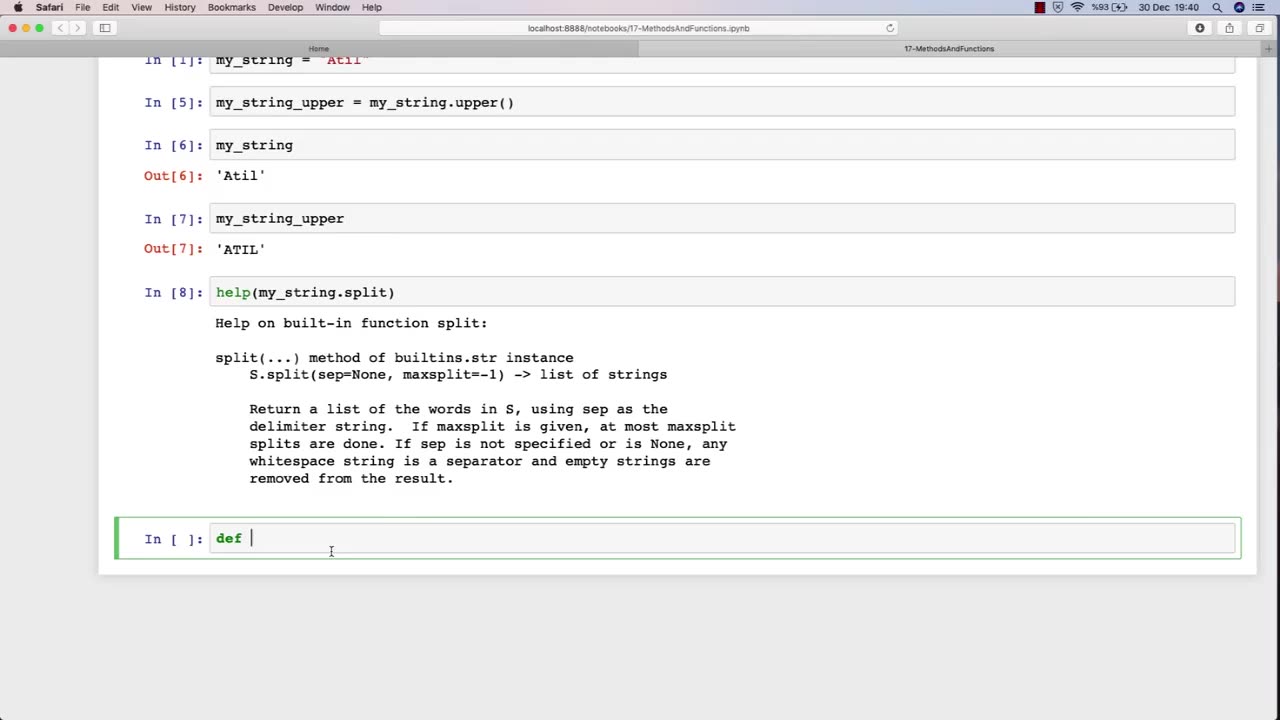
Chapter-30, LEC-2 | Functions Explained (lec-1) | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
The function of an ethical hacking course is to equip individuals with the knowledge, skills, and techniques necessary to become a professional ethical hacker. Ethical hacking is a critical component of cybersecurity, as it involves identifying and addressing potential vulnerabilities in computer systems, networks, and applications before malicious actors can exploit them.
An ethical hacking course typically covers a range of topics related to cybersecurity, including penetration testing, vulnerability assessment, network security, web application security, social engineering, cryptography, and incident response. The course provides students with an understanding of various security threats and how to mitigate them through the use of specialized tools and techniques.
During an ethical hacking course, students learn how to perform vulnerability assessments, conduct penetration testing, and analyze system and network logs to identify potential security threats. They also learn how to use various tools, such as vulnerability scanners and network analyzers, to assess the security posture of a system or network. Additionally, students learn about common attack vectors and techniques, such as SQL injection and cross-site scripting, and how to defend against them.
Overall, the goal of an ethical hacking course is to train individuals to become skilled and responsible cybersecurity professionals who can help organizations protect themselves from cyber attacks. By learning how to identify vulnerabilities and mitigate security threats, students can help ensure the security and privacy of sensitive information and safeguard against potential data breaches.
-
 8:05
8:05
Millionaire Mentor
17 hours agoMegyn Kelly SHOCKED As Hunter Biden Spills Kamala’s Dirty Secret
1091 -
 9:26
9:26
TheSaltyCracker
14 hours agoHero Cop Puts Down Lunatic Holding a Kid Hostage at Knife Point
20.2K174 -
 1:27:58
1:27:58
Coin Stories with Natalie Brunell
14 hours agoQuantum Threat to Bitcoin? Pysh & Lepard Break Down Quantum, A.I. Displacement and Growing Socialism
116 -
 3:53
3:53
WildCreatures
3 days ago $0.15 earnedSwimming With the Giants, Whale Sharks of Darwin Island
1.09K1 -
 12:09
12:09
Actual Justice Warrior
16 hours agoTEEN Mob ATTACKS Domino's Pizza
2.08K13 -
 18:59
18:59
Nate The Lawyer
1 day ago $0.77 earnedDon Lemon Spreads Lie: Crossing Border Illegally Isn’t a Crime. FACT CHECK
51722 -
 2:04:30
2:04:30
Side Scrollers Podcast
18 hours agoGold’s Gym CONTROVERSY & BOYCOTT + Craig ADMITS DEFEAT + More | Side Scrollers
63.4K10 -
 1:26:06
1:26:06
MattMorseTV
17 hours ago $0.09 earned🔴Trump's Press Conference MASSIVE UPDATE.🔴
14.7K61 -
 21:39
21:39
Nikko Ortiz
3 days agoI Take A North Korean Shooting
48.8K8 -
 LIVE
LIVE
Lofi Girl
3 years agolofi hip hop radio 📚 - beats to relax/study to
194 watching