Premium Only Content
Chapter-29, LEC-2 | Useful Methods #hacking #growthhacking #ethicalhacking #rumble #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
It is a crucial part of cybersecurity and helps organizations in protecting their sensitive information from malicious attackers.
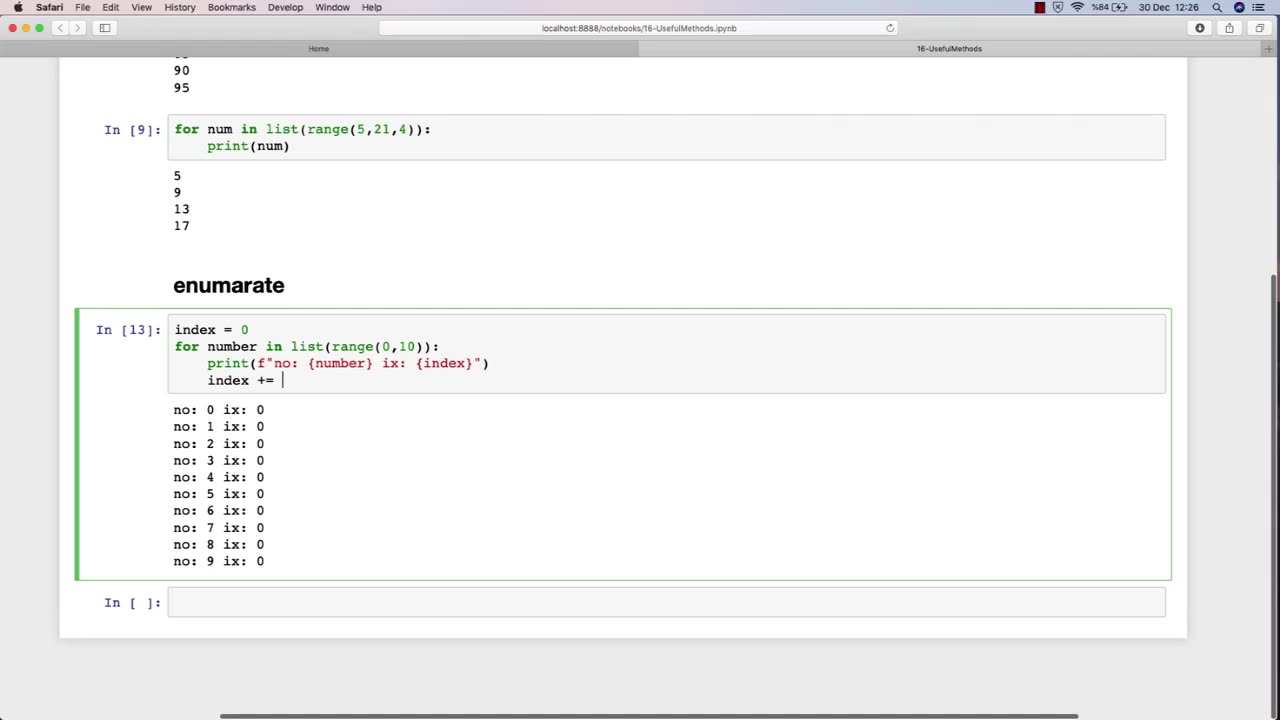
One of the most essential topics in an ethical hacking course is the use of various methods and tools for conducting effective security assessments. One such useful method is the use of penetration testing.
Penetration testing is a simulated attack on a computer system or network to identify vulnerabilities that a malicious attacker could exploit. This method involves using various hacking techniques and tools to try to gain access to the system or network. Penetration testing is a comprehensive approach to testing a system's security and can help identify potential weaknesses that can be addressed before they can be exploited by malicious attackers.
Another important topic in an ethical hacking course is the use of vulnerability scanners. Vulnerability scanners are automated tools that scan a computer system or network to identify vulnerabilities that can be exploited by attackers. These tools can help identify issues such as outdated software, weak passwords, and misconfigured settings.
Social engineering is another useful method that ethical hackers use to identify vulnerabilities in a system or network. Social engineering involves manipulating individuals into divulging sensitive information or performing actions that can compromise the security of a system. This technique can help identify weaknesses in an organization's security policies and training programs.
Overall, ethical hacking courses teach various methods and techniques that can be used to identify vulnerabilities in computer systems and networks. By using these methods, ethical hackers can help organizations strengthen their security measures and protect their sensitive information from malicious attackers.
-
 LIVE
LIVE
Nerdrotic
59 minutes agoNerdrotic At Night 531
495 watching -
 LIVE
LIVE
TheCrucible
33 minutes agoWATCH PARTY! Coach Greg Adams vs Andrew Wilson: Marriage in the West is Good For Men (11/03/25)
1,208 watching -
 LIVE
LIVE
The Jimmy Dore Show
1 hour agoTrump Threatens to INVADE Nigeria! Kash Patel CRASHES OUT Over Jet Use Criticism!
5,135 watching -
 1:25:38
1:25:38
Kim Iversen
3 hours agoTrump’s Nigeria Threat Isn’t About Christians — It’s About China
63.3K53 -
 59:10
59:10
Sean Unpaved
2 hours agoDodgers Dynasty Rolls On, NFL Chaos Reigns, & MNF Showdown Countdown
3.03K1 -
 1:35:56
1:35:56
Redacted News
3 hours agoA MAGA Civil War has just begun, Christians slaughtered in Nigeria, Charlie Kirk's audiit | Redacted
101K133 -
 LIVE
LIVE
Dr Disrespect
8 hours ago🔴LIVE - DR DISRESPECT - ARC RAIDERS - FULL SEND INTO THE RED
1,524 watching -
 26:34
26:34
Stephen Gardner
3 hours ago🔥Elon EXPOSES The Exact Blueprint Dems use to CHEAT on Joe Rogan!!
30.1K89 -
 51:10
51:10
Dad Saves America
7 hours ago $1.36 earnedMask Off Mamdani: NYC’s Socialist “Savior” Is Another Spoiled Aristocrat
14.8K5 -
 6:14
6:14
Buddy Brown
8 hours ago $2.56 earnedLaw Enforcement Caught SNOOPING on PRIVATE LAND! | Buddy Brown
15.2K24