Premium Only Content
Chapter-28, LEC-3 | If Statements | #hacking #ethicalhacking #education #growthhacking
ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking
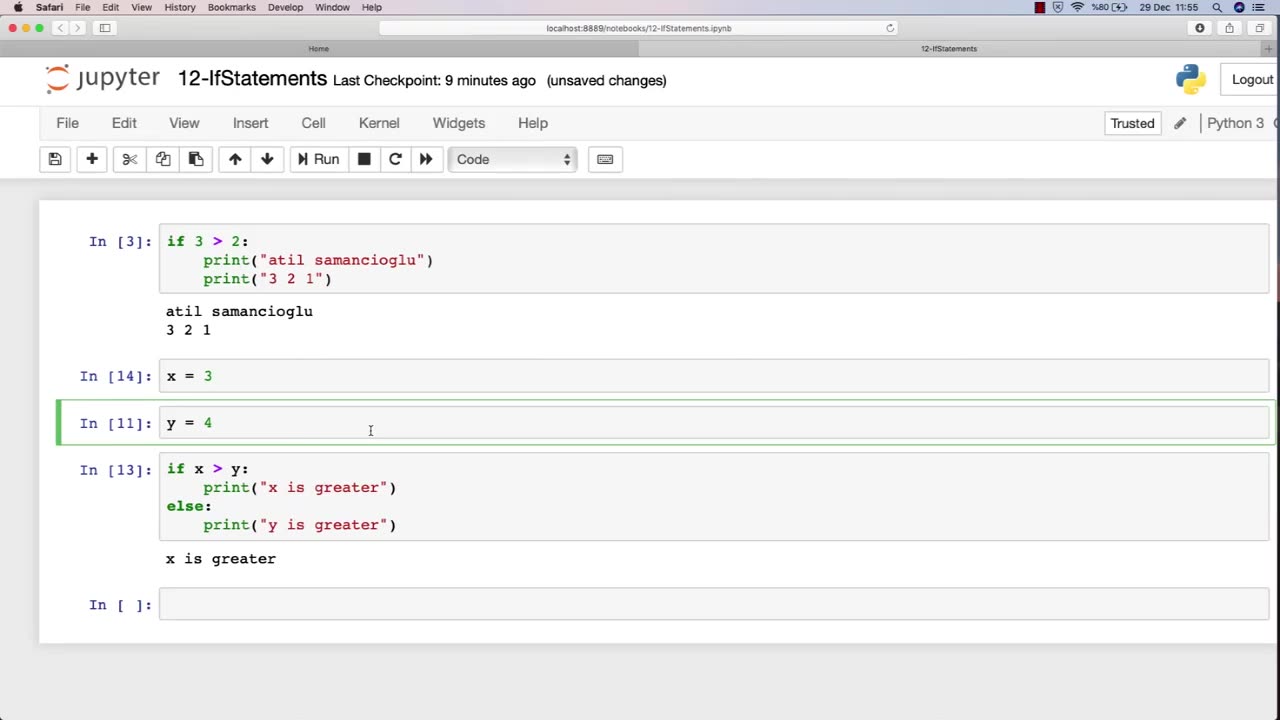
If statements are a fundamental concept in programming that are used extensively in the field of ethical hacking. In ethical hacking, if statements are used to control the flow of a program based on certain conditions.
For instance, an ethical hacker may use if statements to check if a user is authorized to access a certain system or network. If the user is authorized, the program may allow them access, but if they are not authorized, the program may terminate or deny access.
Additionally, if statements can be used to test for certain conditions in a program that may be vulnerable to attack. For example, an ethical hacker may use an if statement to check if a program has any buffer overflow vulnerabilities. If the program does have buffer overflow vulnerabilities, the ethical hacker may use that vulnerability to gain unauthorized access to the system or network.
Furthermore, if statements can be used to test for other security-related conditions, such as weak passwords or unencrypted data. By using if statements to test for these conditions, ethical hackers can identify potential vulnerabilities and take steps to strengthen the security of the system or network.
In summary, if statements are a critical concept in programming that are used extensively in ethical hacking. They allow ethical hackers to control the flow of a program based on certain conditions, test for potential vulnerabilities, and strengthen the security of systems and networks.
-
 LIVE
LIVE
Redacted News
53 minutes agoElection Day Disaster for Trump? Europe preps for WAR against Russia, Israel's PR failure | Redacted
13,372 watching -
 16:44
16:44
Russell Brand
1 hour agoAmerica’s Hidden Royalty
1.3K4 -
 2:05:29
2:05:29
The Quartering
3 hours agoEscape From New York, Harvard Bombers Caught, Trump DEFIES Court On SNAP, Bomb Threat On Plane!
95.9K56 -
 LIVE
LIVE
StoneMountain64
2 hours agoBattlefield REDSEC leveling guns for attachments
241 watching -
 LIVE
LIVE
Pop Culture Crisis
2 hours agoCoca-Cola's WAR ON CHRISTMAS, Movie Press Tour CRINGE, Gen Z HATES Gen Z | Ep, 949
523 watching -
 16:30
16:30
Clintonjaws
17 hours ago $4.31 earned'The View's' Producer Stops Show & Forces Whoopie To Correct Lie
5.43K6 -
 1:10:24
1:10:24
Steve-O's Wild Ride! Podcast
5 days ago $0.38 earnedMatt McCusker Makes Steve-O Nervous | Wild Ride #272
2.84K1 -
 17:09
17:09
Bearing
9 hours agoHasan Goes NUCLEAR On Chat ☢️ ROASTED By JD Vance Over Dog Allegations 🚨
18.8K28 -
 LIVE
LIVE
The HotSeat With Todd Spears
1 hour agoEP 203: The Military "Whistleblower"
773 watching -
![[Ep 784] Election 2025: NYC is Screwed | Tatum Calls Out Kirk Conspiracists | Guest: Sam Anthony](https://1a-1791.com/video/fwe2/00/s8/1/U/Q/E/w/UQEwz.0kob-small-Ep-784-Election-2025-NYC-is.jpg) LIVE
LIVE
The Nunn Report - w/ Dan Nunn
1 hour ago[Ep 784] Election 2025: NYC is Screwed | Tatum Calls Out Kirk Conspiracists | Guest: Sam Anthony
156 watching