Premium Only Content
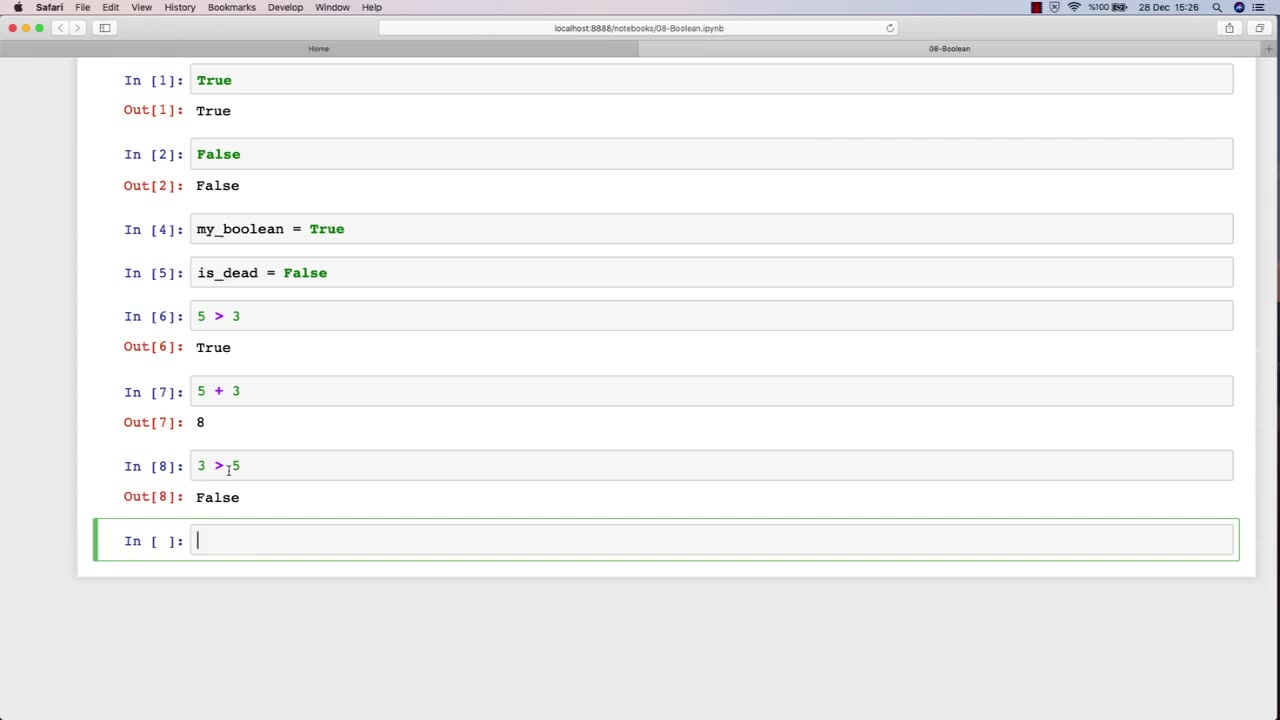
Chapter-27, LEC-13 | 13. Boolean | #ethicalhacking #hacking #education #growthhacking
ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Boolean: "Security Controls"
Description: In the field of ethical hacking, security controls refer to the various measures and technologies that organizations use to protect their computer systems and networks from unauthorized access, use, disclosure, disruption, modification, or destruction. The following are some examples of security controls that may be covered in an ethical hacking course:
Access controls - The use of passwords, biometrics, and other mechanisms to restrict access to systems and data to authorized users only.
Firewalls - Network security devices that filter traffic based on predefined rules to prevent unauthorized access to networks.
Intrusion detection and prevention systems (IDPS) - Security technologies that monitor network traffic and alert administrators to potential threats or attacks.
Encryption - The use of cryptographic techniques to protect sensitive information from unauthorized disclosure or modification.
Anti-virus and anti-malware software - Programs that detect, prevent, and remove malicious software from systems and networks.
Physical security measures - The use of locks, surveillance cameras, and access control systems to prevent unauthorized physical access to data centers and other critical infrastructure.
Network segmentation - The division of a network into smaller, more secure subnetworks to limit the impact of security breaches.
Incident response plans - Policies and procedures that organizations follow in the event of a security incident or data breach.
In an ethical hacking course, students learn how to identify and test the effectiveness of these security controls by simulating attacks and vulnerabilities. By understanding how these security controls work and their limitations, ethical hackers can help organizations strengthen their security posture and protect against cyber threats.
-
 12:12
12:12
GritsGG
11 hours ago23 Warzone Wins in a Row! (Cypher AR)
46.3K -
 2:12:07
2:12:07
Side Scrollers Podcast
18 hours agoCULTURE SHIFT CAUSES MELTDOWNS + MASSIVE CENSORSHIP EFFORTS RAMP UP | SIDE SCROLLERS LIVE
9.08K5 -
 11:25
11:25
Nikko Ortiz
1 day agoMost Painful Fails
42.5K26 -
 43:55
43:55
pewculture
6 days ago $2.05 earnedIf the Purge was real, this is what we'd do... - EP#24
7.29K4 -
 8:14
8:14
MattMorseTV
1 day ago $9.52 earnedTrump just DROPPED the HAMMER.
53.5K62 -
 LIVE
LIVE
Lofi Girl
2 years agoSynthwave Radio 🌌 - beats to chill/game to
258 watching -
 22:39
22:39
BlabberingCollector
9 hours agoThe Alphabet Mafia Is Mad At JK Rowling AGAIN
16K3 -
 5:30:52
5:30:52
SpartakusLIVE
10 hours agoDuos w/ @GloryJean || #1 Masculine Muscle MASS sears YOUR retinas with MIND BENDING content
223K3 -
 3:05:49
3:05:49
TimcastIRL
9 hours agoNew DOCS PROVE Obama Hillary CONSPIRACY To SABOTAGE Trump Admin | Timcast IRL
225K137 -
 2:29:36
2:29:36
Laura Loomer
10 hours agoEP136: YOU'RE FIRED! White House Vetting Crisis Continues
63K39