Premium Only Content
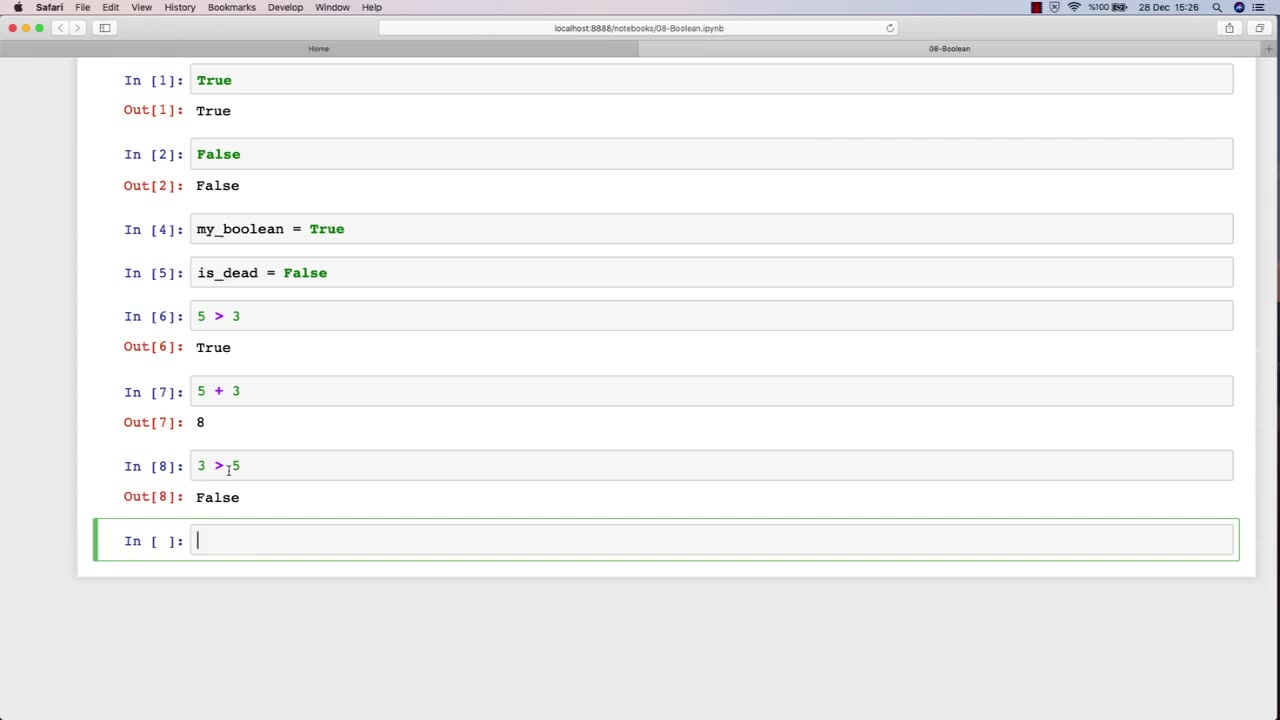
Chapter-27, LEC-13 | 13. Boolean | #ethicalhacking #hacking #education #growthhacking
ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Boolean: "Security Controls"
Description: In the field of ethical hacking, security controls refer to the various measures and technologies that organizations use to protect their computer systems and networks from unauthorized access, use, disclosure, disruption, modification, or destruction. The following are some examples of security controls that may be covered in an ethical hacking course:
Access controls - The use of passwords, biometrics, and other mechanisms to restrict access to systems and data to authorized users only.
Firewalls - Network security devices that filter traffic based on predefined rules to prevent unauthorized access to networks.
Intrusion detection and prevention systems (IDPS) - Security technologies that monitor network traffic and alert administrators to potential threats or attacks.
Encryption - The use of cryptographic techniques to protect sensitive information from unauthorized disclosure or modification.
Anti-virus and anti-malware software - Programs that detect, prevent, and remove malicious software from systems and networks.
Physical security measures - The use of locks, surveillance cameras, and access control systems to prevent unauthorized physical access to data centers and other critical infrastructure.
Network segmentation - The division of a network into smaller, more secure subnetworks to limit the impact of security breaches.
Incident response plans - Policies and procedures that organizations follow in the event of a security incident or data breach.
In an ethical hacking course, students learn how to identify and test the effectiveness of these security controls by simulating attacks and vulnerabilities. By understanding how these security controls work and their limitations, ethical hackers can help organizations strengthen their security posture and protect against cyber threats.
-
 1:08:55
1:08:55
vivafrei
21 hours agoExposing the Trans MADNESS in Maine School Boards! Live with Activist and Truth Teller "Corn Pop"!
35.9K11 -
 LIVE
LIVE
The Rabble Wrangler
1 hour agoThe Best in the West | Live From Rumble Studios
297 watching -
 LIVE
LIVE
Tundra Tactical
2 hours agoThe Great Tundra Nation Gaming Stream!!! Featuring ThePiggNation LAST DAY!!!!
80 watching -
 1:50:18
1:50:18
The Quartering
2 hours agoWhat The Heck Is Even Happening?
83.8K12 -
 DVR
DVR
iCkEdMeL
1 hour ago $2.09 earnedICE SHOOTS Popular TikToker ‘Richard’ During Raid in South L.A.?! 😳 What Really Happened LIVE
5.31K3 -
 16:57
16:57
Clownfish TV
9 hours agoLord of the Rings is RACIST Again According to UK College Course... | Clownfish TV
89010 -
![[Ep 774] Trump’s Ballroom Blitz | 9th Circuit OK’s Guard in Portland | Guest: Sam Anthony](https://1a-1791.com/video/fww1/00/s8/1/2/Z/E/s/2ZEsz.0kob-small-Ep-774-Trumps-Ballroom-Blit.jpg) LIVE
LIVE
The Nunn Report - w/ Dan Nunn
1 hour ago[Ep 774] Trump’s Ballroom Blitz | 9th Circuit OK’s Guard in Portland | Guest: Sam Anthony
118 watching -
 1:05:27
1:05:27
DeVory Darkins
3 hours ago $31.77 earnedTrump scores HISTORIC IMMIGRATION WIN as Democrats STUNNED by ballroom renovations
107K49 -
 43:40
43:40
The Rubin Report
2 hours agoDark Future Predictions & Exposing the Truth About Australia’s Past | Tony Abbott
23.3K13 -
 1:57:45
1:57:45
The Charlie Kirk Show
4 hours agoThis is What Democracy Looks Like + Oxford Union Election Fraud? | Dr. Orr, Ogoloma, Harmon | 10.21
75.5K25