Premium Only Content
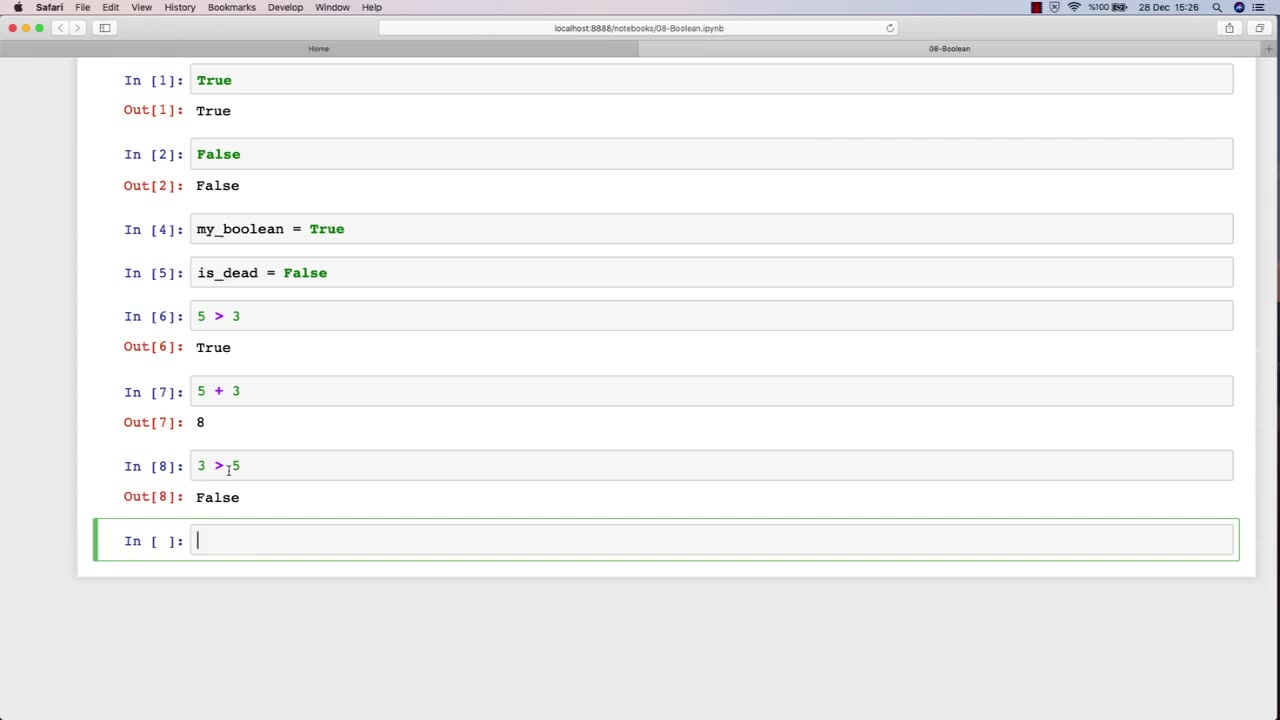
Chapter-27, LEC-13 | 13. Boolean | #ethicalhacking #hacking #education #growthhacking
ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Boolean: "Security Controls"
Description: In the field of ethical hacking, security controls refer to the various measures and technologies that organizations use to protect their computer systems and networks from unauthorized access, use, disclosure, disruption, modification, or destruction. The following are some examples of security controls that may be covered in an ethical hacking course:
Access controls - The use of passwords, biometrics, and other mechanisms to restrict access to systems and data to authorized users only.
Firewalls - Network security devices that filter traffic based on predefined rules to prevent unauthorized access to networks.
Intrusion detection and prevention systems (IDPS) - Security technologies that monitor network traffic and alert administrators to potential threats or attacks.
Encryption - The use of cryptographic techniques to protect sensitive information from unauthorized disclosure or modification.
Anti-virus and anti-malware software - Programs that detect, prevent, and remove malicious software from systems and networks.
Physical security measures - The use of locks, surveillance cameras, and access control systems to prevent unauthorized physical access to data centers and other critical infrastructure.
Network segmentation - The division of a network into smaller, more secure subnetworks to limit the impact of security breaches.
Incident response plans - Policies and procedures that organizations follow in the event of a security incident or data breach.
In an ethical hacking course, students learn how to identify and test the effectiveness of these security controls by simulating attacks and vulnerabilities. By understanding how these security controls work and their limitations, ethical hackers can help organizations strengthen their security posture and protect against cyber threats.
-
 38:21
38:21
Uncommon Sense In Current Times
14 hours agoWho You Really Are | Dr. Neil Anderson on Identity, Freedom & the Power of Truth in Christ
7.53K -
 8:05
8:05
Millionaire Mentor
17 hours agoMegyn Kelly SHOCKED As Hunter Biden Spills Kamala’s Dirty Secret
1091 -
 9:26
9:26
TheSaltyCracker
14 hours agoHero Cop Puts Down Lunatic Holding a Kid Hostage at Knife Point
20.2K174 -
 1:27:58
1:27:58
Coin Stories with Natalie Brunell
14 hours agoQuantum Threat to Bitcoin? Pysh & Lepard Break Down Quantum, A.I. Displacement and Growing Socialism
116 -
 3:53
3:53
WildCreatures
3 days ago $0.15 earnedSwimming With the Giants, Whale Sharks of Darwin Island
1.09K1 -
 12:09
12:09
Actual Justice Warrior
16 hours agoTEEN Mob ATTACKS Domino's Pizza
2.08K13 -
 18:59
18:59
Nate The Lawyer
1 day ago $0.77 earnedDon Lemon Spreads Lie: Crossing Border Illegally Isn’t a Crime. FACT CHECK
51722 -
 2:04:30
2:04:30
Side Scrollers Podcast
18 hours agoGold’s Gym CONTROVERSY & BOYCOTT + Craig ADMITS DEFEAT + More | Side Scrollers
63.4K10 -
 1:26:06
1:26:06
MattMorseTV
17 hours ago $0.09 earned🔴Trump's Press Conference MASSIVE UPDATE.🔴
14.7K61 -
 21:39
21:39
Nikko Ortiz
3 days agoI Take A North Korean Shooting
48.8K8