Premium Only Content
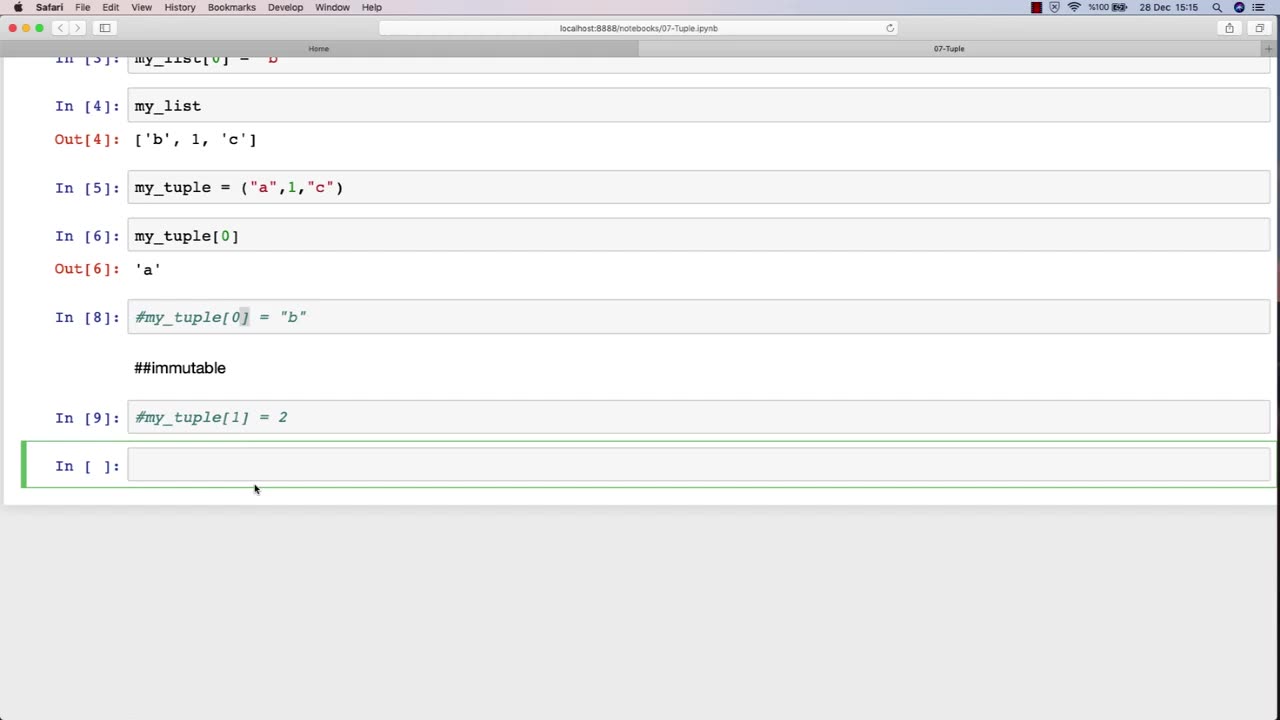
Chapter-27, LEC-12 | Tuples | #ethicalhacking #hacking #education #growthhacking #biohacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
Tuple: "Types of Attacks"
Description: The types of attacks used in ethical hacking refer to the various methods and techniques that attackers use to compromise computer systems and networks. The following is a tuple of some of the common types of attacks that may be covered in an ethical hacking course:
Phishing attacks - A type of social engineering attack that tricks users into revealing sensitive information or performing harmful actions, such as clicking on a malicious link or downloading malware.
SQL injection attacks - A type of web application attack that exploits vulnerabilities in SQL database queries to gain unauthorized access to data.
Cross-site scripting (XSS) attacks - A type of web application attack that injects malicious scripts into a web page to steal user information or hijack user sessions.
Brute force attacks - A type of password guessing attack that tries all possible password combinations to gain unauthorized access to a system or network.
Denial of Service (DoS) attacks - A type of attack that floods a network or system with traffic to make it unavailable to legitimate users.
Man-in-the-middle (MitM) attacks - A type of attack that intercepts and modifies communication between two parties to steal sensitive information or perform malicious actions.
Session hijacking attacks - A type of attack that steals user session tokens to gain unauthorized access to a web application or system.
Ransomware attacks - A type of malware attack that encrypts files on a system and demands payment in exchange for the decryption key.
Advanced persistent threats (APTs) - A type of sophisticated and targeted attack that uses multiple techniques and tactics to compromise a system or network over a long period of time.
Insider attacks - A type of attack that is carried out by someone who has authorized access to a system or network, such as an employee or contractor.
By understanding the various types of attacks, ethical hackers can better identify and address security vulnerabilities in computer systems and networks. In an ethical hacking course, students learn how to use different tools and techniques to simulate these attacks in a controlled environment and develop effective strategies for preventing and mitigating them.
-

ThisIsDeLaCruz
46 minutes agoBack Stage Pass with Avenged Sevenfold
762 -
 LIVE
LIVE
Tundra Tactical
3 hours agoProfessional Gun Nerd Plays Battlefield 6
71 watching -
 1:01:12
1:01:12
Donald Trump Jr.
5 hours agoThe China Matrix with Journalist Lee Smith | TRIGGERED Ep.288
105K71 -
 LIVE
LIVE
MattMorseTV
2 hours ago🔴Trump's '60 Minutes' INTERVIEW + MUCH MORE.🔴
1,329 watching -
 LIVE
LIVE
Dr Disrespect
10 hours ago🔴LIVE - DR DISRESPECT - ARC RAIDERS - FULL SEND INTO THE RED
1,130 watching -
 1:02:08
1:02:08
BonginoReport
4 hours agoNicki Minaj Speaks Out Against Christian Persecution - Nightly Scroll w/ Hayley Caronia (Ep.169)
37.7K23 -
 LIVE
LIVE
SpartakusLIVE
4 hours agoSNIPING in Battlefield 6 - REDSEC || Monday MOTIVATION to CONQUER the Week
143 watching -
 LIVE
LIVE
Nerdrotic
2 hours ago $2.05 earnedNerdrotic At Night 531
279 watching -
 LIVE
LIVE
The Jimmy Dore Show
3 hours agoTrump Threatens to INVADE Nigeria! Kash Patel CRASHES OUT Over Jet Use Criticism!
7,466 watching -
 LIVE
LIVE
Conductor_Jackson
22 hours agoLet's Play Unrailed 2 Solo! 🚂🚂🚂🚂🚂🚂
12 watching