Premium Only Content
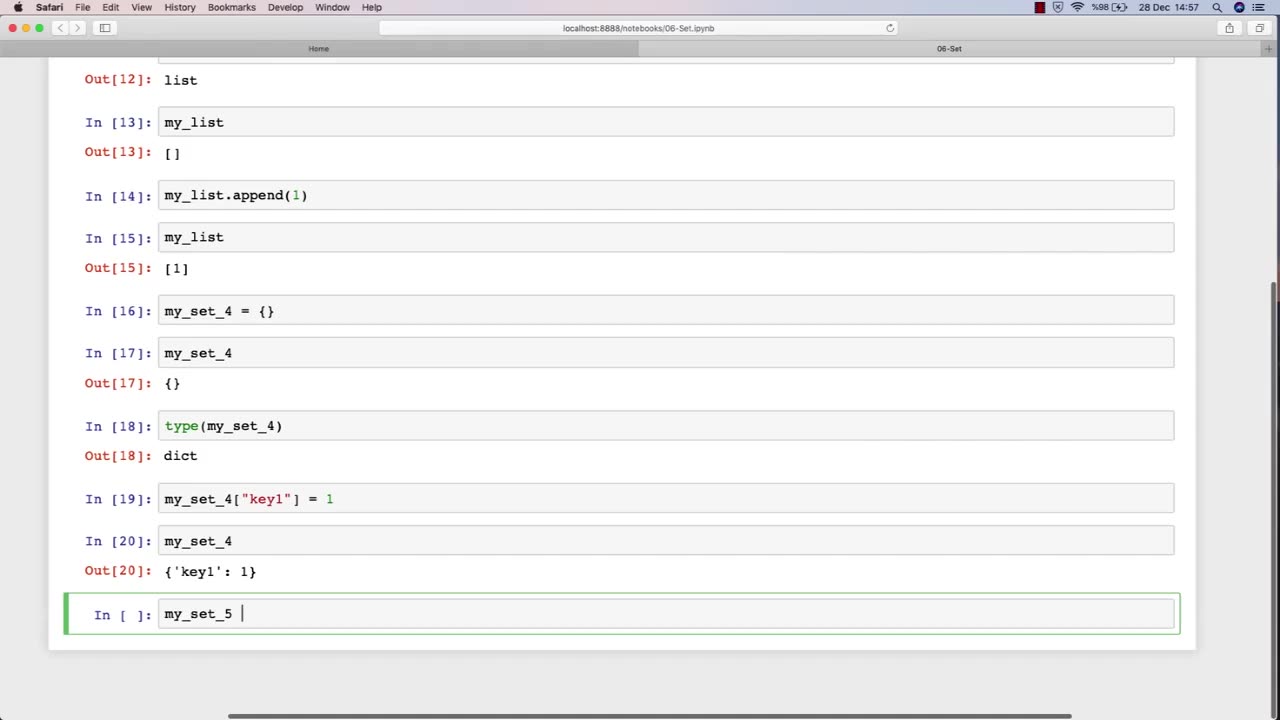
Chapter-27, LEC-11 | Sets | #ethicalhacking #hacking #education #growthhacking #biohacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking
Set: "Tools and Techniques"
Description: The tools and techniques used in ethical hacking refer to the software and hardware tools, as well as the methodologies and approaches, used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a set of some of the common tools and techniques that may be covered in an ethical hacking course:
Network scanners and vulnerability scanners, such as Nmap and Nessus, to identify weaknesses and vulnerabilities in networks and systems.
Password cracking tools, such as John the Ripper and Hashcat, to identify weak passwords and brute-force passwords.
Social engineering techniques, such as phishing and pretexting, to manipulate people into revealing sensitive information or performing actions that are harmful to their organization.
Exploit frameworks, such as Metasploit, to automate the process of identifying and exploiting vulnerabilities in systems and networks.
Packet sniffers and network analysis tools, such as Wireshark and Tcpdump, to capture and analyze network traffic for security purposes.
Forensic tools, such as EnCase and FTK, to gather and analyze digital evidence of security incidents and data breaches.
Malware analysis tools, such as IDA Pro and OllyDbg, to analyze and reverse-engineer malware to understand its functionality and behavior.
Virtualization and sandboxing tools, such as VirtualBox and Cuckoo Sandbox, to create isolated environments for testing and experimenting with potentially harmful software.
The tools and techniques used in ethical hacking are constantly evolving and changing, so it is important for students to stay up-to-date with the latest trends and developments in the field. By mastering these tools and techniques, students can become proficient in ethical hacking and develop the skills necessary to identify and address security vulnerabilities in computer systems and networks.
-
 LIVE
LIVE
Jerry After Dark
14 hours agoHole In One Challenge | Presented by TGL
4,980 watching -
 3:56:39
3:56:39
Alex Zedra
6 hours agoLIVE! New Game | The Escape: Together
47.5K7 -
 5:01:11
5:01:11
FreshandFit
7 hours agoJoe Budden Arrested For Being A Perv! Tesla Cybertruck Explosion
80.1K12 -
 2:08:45
2:08:45
Kim Iversen
9 hours agoNew Year, New PSYOP?: The Fort Bragg Connection In The New Years Terror Attacks
67.3K118 -
 1:41:18
1:41:18
Glenn Greenwald
9 hours agoTerror Attacks Exploited To Push Unrelated Narratives; Facing Imminent Firing Squad, Liz Cheney Awarded Presidential Medal | SYSTEM UPDATE #381
97K175 -
 1:00:32
1:00:32
Man in America
11 hours ago🔴 LIVE: Terror Attacks or False Flags? IT DOESN'T ADD UP!!!
59K18 -
 1:02:38
1:02:38
Donald Trump Jr.
13 hours agoNew Year’s Terror, Latest Breaking News with Sebastian Gorka | TRIGGERED Ep.204
194K398 -
 59:59
59:59
The StoneZONE with Roger Stone
8 hours agoAfter Years of Targeting Trump, FBI and DOJ are Unprepared to Stop Terror Attacks | The StoneZONE
60.7K19 -
 1:26:42
1:26:42
Leonardaisfunny
6 hours ago $4.26 earnedH-1b Visas: Infinity Indians
39.1K18 -
 1:08:33
1:08:33
Josh Pate's College Football Show
11 hours ago $2.57 earnedPlayoff Reaction Special: Ohio State Owns Oregon | Texas Survives | UGA vs Notre Dame Takeaways
36.5K6