Premium Only Content
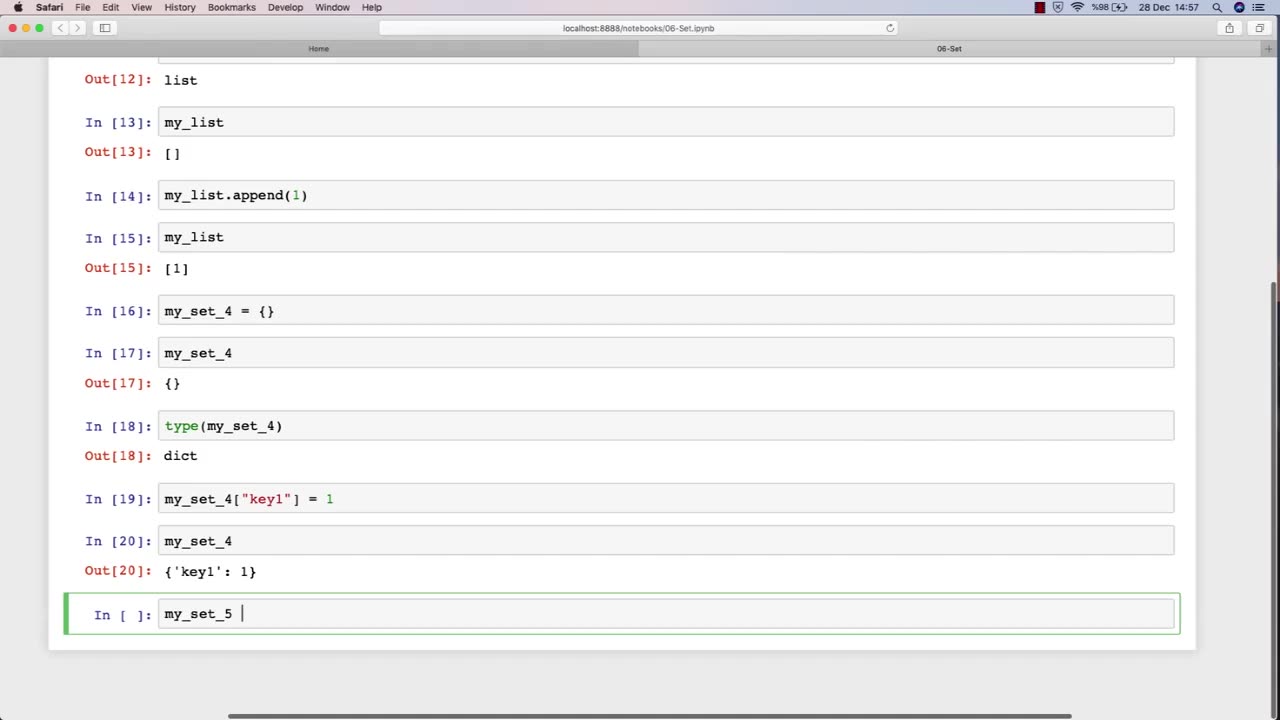
Chapter-27, LEC-11 | Sets | #ethicalhacking #hacking #education #growthhacking #biohacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking
Set: "Tools and Techniques"
Description: The tools and techniques used in ethical hacking refer to the software and hardware tools, as well as the methodologies and approaches, used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a set of some of the common tools and techniques that may be covered in an ethical hacking course:
Network scanners and vulnerability scanners, such as Nmap and Nessus, to identify weaknesses and vulnerabilities in networks and systems.
Password cracking tools, such as John the Ripper and Hashcat, to identify weak passwords and brute-force passwords.
Social engineering techniques, such as phishing and pretexting, to manipulate people into revealing sensitive information or performing actions that are harmful to their organization.
Exploit frameworks, such as Metasploit, to automate the process of identifying and exploiting vulnerabilities in systems and networks.
Packet sniffers and network analysis tools, such as Wireshark and Tcpdump, to capture and analyze network traffic for security purposes.
Forensic tools, such as EnCase and FTK, to gather and analyze digital evidence of security incidents and data breaches.
Malware analysis tools, such as IDA Pro and OllyDbg, to analyze and reverse-engineer malware to understand its functionality and behavior.
Virtualization and sandboxing tools, such as VirtualBox and Cuckoo Sandbox, to create isolated environments for testing and experimenting with potentially harmful software.
The tools and techniques used in ethical hacking are constantly evolving and changing, so it is important for students to stay up-to-date with the latest trends and developments in the field. By mastering these tools and techniques, students can become proficient in ethical hacking and develop the skills necessary to identify and address security vulnerabilities in computer systems and networks.
-
 16:44
16:44
Russell Brand
1 hour agoAmerica’s Hidden Royalty
1.3K4 -
 2:05:29
2:05:29
The Quartering
3 hours agoEscape From New York, Harvard Bombers Caught, Trump DEFIES Court On SNAP, Bomb Threat On Plane!
95.9K53 -
 LIVE
LIVE
StoneMountain64
2 hours agoBattlefield REDSEC leveling guns for attachments
245 watching -
 LIVE
LIVE
Pop Culture Crisis
2 hours agoCoca-Cola's WAR ON CHRISTMAS, Movie Press Tour CRINGE, Gen Z HATES Gen Z | Ep, 949
527 watching -
 16:30
16:30
Clintonjaws
17 hours ago $4.31 earned'The View's' Producer Stops Show & Forces Whoopie To Correct Lie
5.43K4 -
 1:10:24
1:10:24
Steve-O's Wild Ride! Podcast
5 days ago $0.38 earnedMatt McCusker Makes Steve-O Nervous | Wild Ride #272
2.84K1 -
 17:09
17:09
Bearing
9 hours agoHasan Goes NUCLEAR On Chat ☢️ ROASTED By JD Vance Over Dog Allegations 🚨
6.86K27 -
 LIVE
LIVE
The HotSeat With Todd Spears
1 hour agoEP 203: The Military "Whistleblower"
768 watching -
![[Ep 784] Election 2025: NYC is Screwed | Tatum Calls Out Kirk Conspiracists | Guest: Sam Anthony](https://1a-1791.com/video/fwe2/00/s8/1/U/Q/E/w/UQEwz.0kob-small-Ep-784-Election-2025-NYC-is.jpg) LIVE
LIVE
The Nunn Report - w/ Dan Nunn
1 hour ago[Ep 784] Election 2025: NYC is Screwed | Tatum Calls Out Kirk Conspiracists | Guest: Sam Anthony
166 watching -
 1:22:54
1:22:54
DeVory Darkins
4 hours agoTrump makes shocking announcement as Major ELECTION UPDATE drops after bomb threat
91.8K53