Premium Only Content
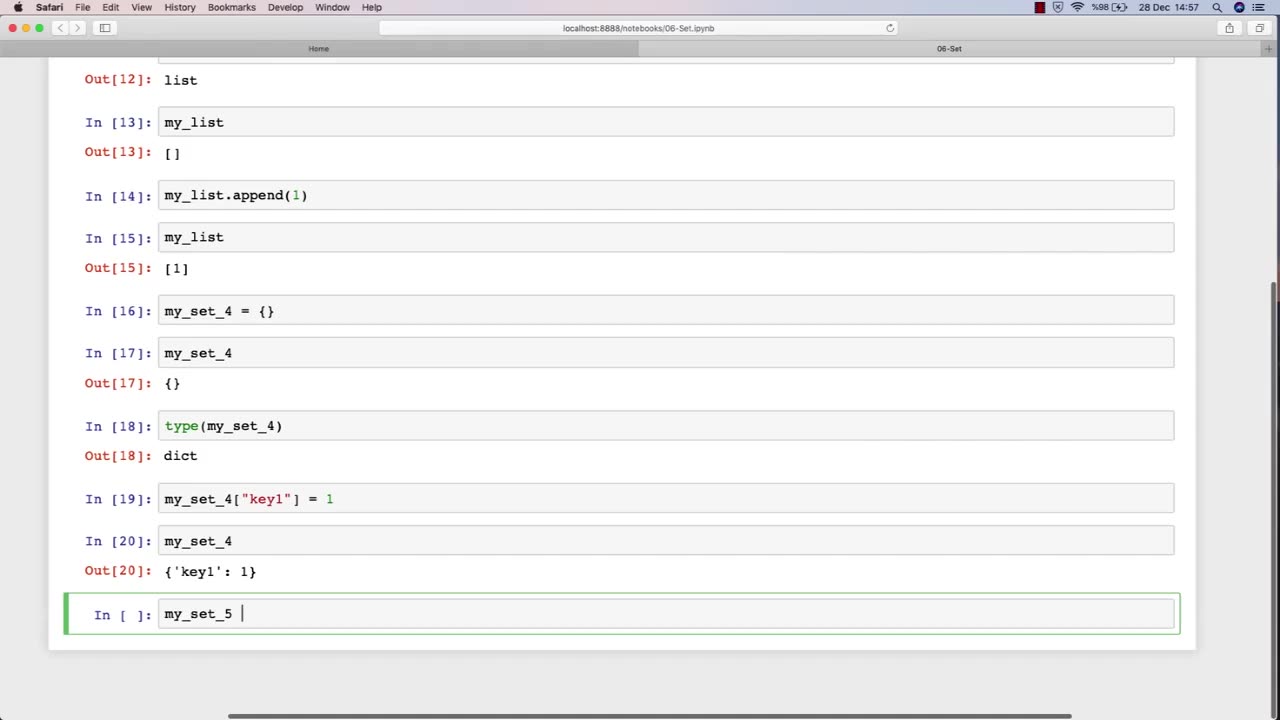
Chapter-27, LEC-11 | Sets | #ethicalhacking #hacking #education #growthhacking #biohacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking
Set: "Tools and Techniques"
Description: The tools and techniques used in ethical hacking refer to the software and hardware tools, as well as the methodologies and approaches, used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a set of some of the common tools and techniques that may be covered in an ethical hacking course:
Network scanners and vulnerability scanners, such as Nmap and Nessus, to identify weaknesses and vulnerabilities in networks and systems.
Password cracking tools, such as John the Ripper and Hashcat, to identify weak passwords and brute-force passwords.
Social engineering techniques, such as phishing and pretexting, to manipulate people into revealing sensitive information or performing actions that are harmful to their organization.
Exploit frameworks, such as Metasploit, to automate the process of identifying and exploiting vulnerabilities in systems and networks.
Packet sniffers and network analysis tools, such as Wireshark and Tcpdump, to capture and analyze network traffic for security purposes.
Forensic tools, such as EnCase and FTK, to gather and analyze digital evidence of security incidents and data breaches.
Malware analysis tools, such as IDA Pro and OllyDbg, to analyze and reverse-engineer malware to understand its functionality and behavior.
Virtualization and sandboxing tools, such as VirtualBox and Cuckoo Sandbox, to create isolated environments for testing and experimenting with potentially harmful software.
The tools and techniques used in ethical hacking are constantly evolving and changing, so it is important for students to stay up-to-date with the latest trends and developments in the field. By mastering these tools and techniques, students can become proficient in ethical hacking and develop the skills necessary to identify and address security vulnerabilities in computer systems and networks.
-
 2:02:36
2:02:36
Badlands Media
11 hours agoBaseless Conspiracies Ep. 157
22.2K17 -
 2:06:09
2:06:09
Inverted World Live
8 hours agoMysterious Crash at Area 51 | Ep. 134
15.6K10 -
 2:48:59
2:48:59
TimcastIRL
6 hours agoTrump Endorses Cuomo, Says NO COMMIE MAMDANI, Obama REFUSES To Endorse Mamdani | Timcast IRL
253K144 -
 LIVE
LIVE
Drew Hernandez
1 day agoGOP CIVIL WAR: TUCKER CARLSON DERANGEMENT SYNDROME AT ALL TIME HIGH
1,002 watching -
 14:44
14:44
Sponsored By Jesus Podcast
1 day agoYou Can't Serve God & MONEY | Is Money the Root of All Evil?
15.9K15 -
 2:47:28
2:47:28
Barry Cunningham
9 hours agoYOU'VE BEEN MISINFORMED! GREED IS ACTUALLY GOOD! ESPECIALLY NOW! (AND MORE NEWS)
89.3K37 -
 7:18:24
7:18:24
SpartakusLIVE
9 hours agoSNIPING in Battlefield 6 - REDSEC || Monday MOTIVATION to CONQUER the Week
49.8K4 -
 49:25
49:25
ThisIsDeLaCruz
5 hours ago $5.80 earnedBack Stage Pass with Avenged Sevenfold
49.2K8 -
 6:43:40
6:43:40
GritsGG
10 hours agoWorld Record Win Streak Attempt! #1 Most Wins 3880+!
26K2 -
 3:12:05
3:12:05
Tundra Tactical
7 hours ago $12.45 earnedProfessional Gun Nerd Plays Battlefield 6
56.1K5