Premium Only Content
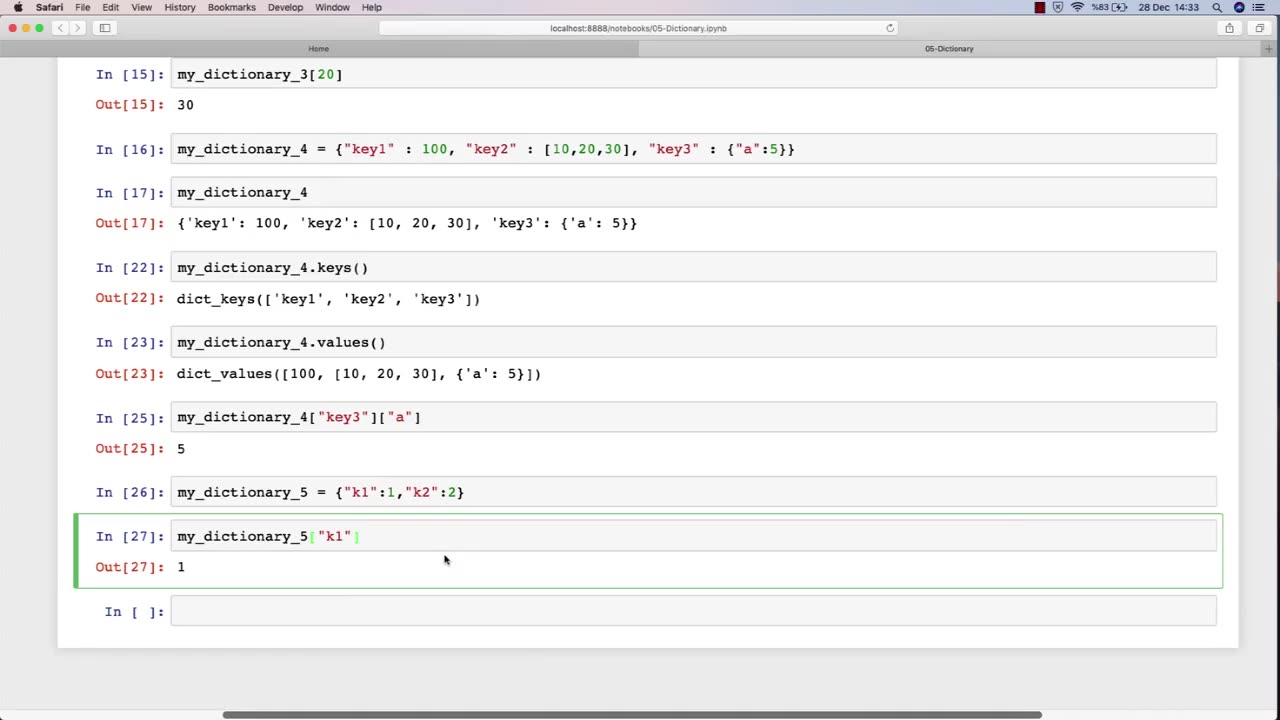
Chapter-27, PEC-10 | Dictionary | #ethicalhacking #hacking #education #growthhacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking
Dictionary: "Ethical Hacking Terminology"
Description: The ethical hacking terminology dictionary is a collection of technical terms and jargon commonly used in the field of ethical hacking. These terms are used to describe various tools, techniques, and methodologies used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a list of some of the common terms that may be included in an ethical hacking course:
Exploit - A piece of software or code that takes advantage of a vulnerability in a computer system or network.
Payload - The part of an exploit that performs a malicious action, such as stealing data or taking control of a system.
Vulnerability - A weakness in a computer system or network that can be exploited by attackers to gain unauthorized access or perform malicious actions.
Penetration Testing - The process of identifying and exploiting vulnerabilities in a computer system or network to assess its security posture.
Social Engineering - The use of psychological manipulation to trick people into revealing sensitive information or performing actions that are harmful to their organization.
Malware - Software that is designed to perform malicious actions, such as stealing data or taking control of a system.
Brute Force Attack - A method of guessing a password by trying every possible combination until the correct one is found.
Rootkit - A type of malware that hides its presence on a system and gives an attacker privileged access to the system.
Denial of Service (DoS) Attack - A type of attack that floods a network or system with traffic to make it unavailable to legitimate users.
Firewall - A security measure that monitors and controls incoming and outgoing network traffic to prevent unauthorized access.
The ethical hacking terminology dictionary is an important resource for students to learn and understand the technical terms and jargon used in the field of ethical hacking. By mastering these terms, students can communicate effectively with other professionals in the field and better understand the technical aspects of ethical hacking.
-
 18:11
18:11
Tactical Considerations
14 hours agoIs This the Best Truck Gun for 2025?
2233 -
 8:37
8:37
The Art of Improvement
19 hours agoLife Lessons I’d Tell My Teenage Self
74 -
 LIVE
LIVE
BEK TV
22 hours agoTrent Loos in the Morning - 9/19/2025
200 watching -
 17:22
17:22
Adam Does Movies
12 hours ago $0.47 earnedIce Road: Vengeance - Movie Review
28.3K4 -
 45:05
45:05
Uncommon Sense In Current Times
16 hours ago $0.08 earnedDarwin vs. DNA | Dr. Nathaniel Jeanson on Creation Science, Evolution & the Case for Genesis
8.8K2 -
 32:19
32:19
The Lou Holtz Show
13 hours agoThe Lou Holtz Show S2 EP18 | Danica Patrick on Fearlessness, Faith & Finding Purpose #podcast
3.5K4 -
 23:41
23:41
The Official Corbett Report Rumble Channel
9 hours agoDiscord Democracy is Coming For Us All! - New World Next Week
3.47K12 -
 49:14
49:14
CharLee Simons presents DO NOT TALK
1 day agoSCREW YOU, ZUCKERBERG (Sam Anthony is back!)
3.25K1 -
 1:04:26
1:04:26
SinCityCrypto
17 hours ago $0.36 earnedAltcoins About to EXPLODE (ETF Approvals)
4.3K1 -
 LIVE
LIVE
Times Now World
2 days agoLIVE | Putin in Military Gear Leads Massive Zapad 2025 Drills With 100,000 Troops | TIMES NOW WORLD
718 watching